How to Set Up a Remote MCP Server for AI Agents
A remote MCP server allows AI agents running locally to securely access tools and datasets hosted on a different machine or cloud environment. This guide walks through the architecture behind remote MCP connections, compares transport options like Streamable HTTP and SSE, and covers the security steps you need before exposing any MCP server to the internet.
What Is a Remote MCP Server?
A remote MCP server is a Model Context Protocol server that runs on a separate machine from the AI client connecting to it. Instead of running on localhost with stdio transport, the server listens over the network and accepts connections from clients on other devices, networks, or cloud environments. The typical architecture looks like this:
- AI Client (Claude Desktop, Cursor, or a custom agent) initiates a connection
- Transport layer (Streamable HTTP, SSE, or SSH tunnel) carries MCP messages between client and server
- Remote MCP Server receives requests, executes tools, and returns results
This setup opens up capabilities that local-only servers can't match. Teams can share a single set of MCP tools instead of configuring each developer's machine separately. Servers can reach databases, APIs, and file systems that only exist in a cloud environment. Centralized hosting also means you update the server once rather than pushing changes to every client. The tradeoff is complexity. A local stdio server has zero network exposure. A remote server has all the security concerns of any internet-facing service: authentication, encryption, access control, and session management. The rest of this guide covers how to handle each of these.
What to check before scaling remote mcp server
MCP supports several transport mechanisms for remote connections. Your choice depends on infrastructure, client support, and security requirements.
Streamable HTTP (Recommended)
Streamable HTTP is the current standard transport for remote MCP servers, introduced to replace the older SSE-based approach. It uses a single HTTP endpoint for both requests and responses, with optional Server-Sent Events for streaming.
How it works:
- Client sends JSON-RPC requests via HTTP POST to a single endpoint (typically
/mcp) - Server responds with JSON-RPC results, or opens an SSE stream for long-running operations
- Session state is tracked via the
Mcp-Session-Idheader - Supports both stateless and stateful server implementations
Why it replaced SSE: The original SSE transport required two separate endpoints, one for client-to-server (POST) and one for server-to-client (SSE stream). This made deployment harder because standard HTTP infrastructure (load balancers, CDNs, API gateways) doesn't always handle persistent SSE connections well. Streamable HTTP works with standard request/response patterns while still supporting streaming when needed.
Server-Sent Events (SSE) - Deprecated
SSE was the original remote transport in the MCP spec. It still works in many clients and servers, but the MCP specification deprecated it in late 2024 in favor of Streamable HTTP. If you're building a new remote server, use Streamable HTTP. If you're connecting to an existing SSE-based server, most clients (including Claude Desktop) still support it through tools like mcp-remote.
SSH Tunneling
SSH tunneling isn't an MCP transport protocol. It's a way to expose a local stdio-based MCP server to a remote client without modifying the server at all.
How it works:
- Run your MCP server locally using stdio transport
- Set up an SSH tunnel from the client machine to the server machine
- The client connects to
localhost:PORTwhich tunnels to the remote server
This approach is useful for development and testing. It inherits SSH's authentication and encryption, so you don't need to implement separate security. But it doesn't scale well for production use or team-wide access.
Deploying a Remote MCP Server
The deployment process varies by platform, but the core steps are the same: package your server, deploy it to a host, configure authentication, and expose it over HTTPS.
Cloudflare Workers
Cloudflare
Workers provide a serverless option with built-in MCP support. Their agents SDK includes an McpAgent class that handles Streamable HTTP transport automatically.
import { McpAgent } from "agents/mcp";
import { McpServer } from "@modelcontextprotocol/sdk/server/mcp.js";
export class RemoteMCPServer extends McpAgent {
server = new McpServer({
name: "my-remote-server",
version: "1.0.0",
});
async init() {
this.server.tool("hello", "Say hello", {}, async () => ({
content: [{ type: "text", text: "Hello from the remote server!" }],
}));
}
}
Deploy with wrangler deploy and your server is live at a Cloudflare URL with automatic HTTPS.
Google Cloud Run
Cloud
Run works well for containerized MCP servers. Package your server in a Docker container, push it to Artifact Registry, and deploy:
gcloud run deploy my-mcp-server \
--image gcr.io/my-project/mcp-server \
--port 8080 \
--no-allow-unauthenticated
The --no-allow-unauthenticated flag is important. Without it, anyone on the internet can call your MCP server.
Azure Functions
Azure
Functions supports MCP servers through the Azure Functions MCP extension. The Azure Developer CLI (azd) provides templates for quick setup:
azd init --template azure-functions-mcp
azd up
Self-Hosted (VPS or On-Premises)
For full control, run the server on your own infrastructure. You'll need to handle HTTPS certificates (use Let's Encrypt), reverse proxy configuration (nginx or Caddy), and process management yourself.
### Example: Run behind Caddy with automatic HTTPS
caddy reverse-proxy --from mcp.yourdomain.com --to localhost:3000
Security: Protecting Your Remote MCP Server
Exposing an MCP server to the internet creates real attack surface. A misconfigured server can let unauthorized users discover and execute any tool it provides, potentially accessing databases, file systems, or third-party APIs.
Authentication Every remote MCP server needs authentication. The MCP specification recommends OAuth 2.1 for production deployments. Here are the main approaches:
OAuth 2.1 with PKCE is the recommended standard. The client initiates a browser-based login flow, the user authenticates with the identity provider, and the client receives a scoped access token. This works well for interactive clients like Claude Desktop.
API keys work for server-to-server and agent-to-agent communication. They're simpler to implement but harder to rotate and don't support fine-grained scoping without additional logic.
Mutual TLS (mTLS) adds certificate-based authentication on top of HTTPS. Both client and server verify each other's certificates. This is the strongest option for server-to-server communication but adds certificate management overhead.
Transport Security
Always use HTTPS in production. Plain HTTP exposes every request and response to network observers
- Validate the
Originheader on all incoming requests to prevent DNS rebinding attacks - When running locally for development, bind to
127.0.0.1(not0.0.0.0) to prevent external access - Use cryptographically random session IDs and invalidate them after inactivity
Access Control
Authentication proves identity. Authorization controls what that identity can do.
- Scope tool access per user or agent. Not every client needs access to every tool
- Rate-limit requests to prevent abuse and accidental runaway loops
- Log every tool invocation for audit purposes
- Validate all input parameters server-side, even if the client is trusted
Common Mistakes
- Deploying without authentication. Even "internal" servers get exposed through misconfigured networks
- Storing API keys in client config files. Use environment variables or secret managers
- Skipping input validation. MCP tools can execute arbitrary operations. Treat every input as untrusted
- No rate limiting. An agent stuck in a loop can hammer your server with thousands of requests per minute


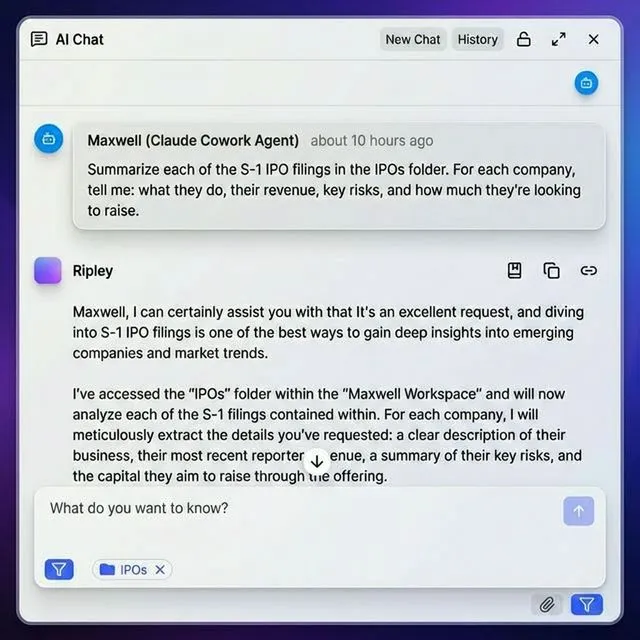
Give Your AI Agents Persistent Storage
Fastio gives teams shared workspaces, MCP tools, and searchable file context to run remote mcp server workflows with reliable agent and human handoffs.
Connecting Clients to a Remote MCP Server
Once your server is running, you need to configure clients to connect. The setup depends on which client you're using.
Claude Desktop
Claude Desktop supports remote MCP servers through its Connectors feature:
- Open Claude Desktop and go to Settings
- Navigate to Connectors
- Click Add custom connector
- Enter your remote MCP server URL (e.g.,
https://mcp.yourdomain.com/mcp) - Complete any authentication flow the server requires
Note: Remote servers configured via claude_desktop_config.json won't work for Streamable HTTP. You must use the Connectors UI for remote connections. For servers that only support SSE transport, you can use the mcp-remote bridge:
{
"mcpServers": {
"my-remote-server": {
"command": "npx",
"args": ["mcp-remote", "https://mcp.yourdomain.com/sse"]
}
}
}
Claude Code (CLI)
Claude Code supports remote MCP servers directly in its configuration:
{
"mcpServers": {
"remote-tools": {
"url": "https://mcp.yourdomain.com/mcp",
"headers": {
"Authorization": "Bearer YOUR_API_KEY"
}
}
}
}
Cursor, VS Code, and Windsurf
These editors support MCP through their settings panels. Add the server URL and authentication details in the MCP configuration section. Each editor handles the transport negotiation automatically once you provide the URL.
Programmatic Clients
For custom agent frameworks, use the MCP SDK's StreamableHTTPClientTransport:
import { Client } from "@modelcontextprotocol/sdk/client/index.js";
import {
StreamableHTTPClientTransport
} from "@modelcontextprotocol/sdk/client/streamableHttp.js";
const transport = new StreamableHTTPClientTransport(
new URL("https://mcp.yourdomain.com/mcp"),
{ headers: { Authorization: `Bearer ${apiKey}` } }
);
const client = new Client({
name: "my-agent",
version: "1.0.0"
});
await client.connect(transport);
const tools = await client.listTools();
Using Fastio as a Remote MCP Server
If you need remote file storage, search, and document intelligence for your agents, Fastio provides a hosted MCP server with 19 consolidated tools over Streamable HTTP and SSE transport. Instead of building and hosting your own MCP server for file operations, you connect to /storage-for-agents/ and get access to file upload/download, workspace management, AI-powered search, document Q&A with citations, and more.
Quick Setup
In Claude Desktop: Add Fastio as a custom connector through Settings > Connectors. Enter `/storage-for-agents/ as the server URL.
In Claude Code or other MCP clients:
{
"mcpServers": {
"fast-io": {
"url": "/storage-for-agents/"
}
}
}
The server handles authentication through the MCP session. Agents can sign up for a free account (50GB storage, 5,000 credits/month, no credit card required) and start using all 19 consolidated tools immediately.
Why Use It Instead of a DIY Server
- No infrastructure to manage. The server runs on Cloudflare's edge network with session state in Durable Objects
- Built-in RAG. Toggle Intelligence Mode on any workspace and files are automatically indexed. Ask questions and get cited answers without setting up a separate vector database
- Ownership transfer. An agent can build workspaces, upload files, and configure branded portals, then transfer ownership to a human while keeping admin access
- Works with any LLM. Claude, GPT-4, Gemini, LLaMA, and local models all work through the same MCP interface
For full documentation, see the MCP skill guide.
Troubleshooting Remote MCP Connections
Remote connections introduce failure modes that don't exist with local stdio servers. Here are the most common problems and how to fix them.
Connection Refused or Timeout
- Check the URL. Make sure you're using
https://(nothttp://) and the correct port - Verify the server is running. Hit the server URL in a browser or with
curlto confirm it responds - Check firewall rules. Cloud providers block most ports by default. Ensure your server's port is open for inbound traffic
Authentication Failures
- Expired tokens. OAuth tokens have short lifetimes. Check if your token needs refreshing
- Wrong auth method. Some servers expect Bearer tokens, others expect API keys in custom headers. Check the server's documentation
- CORS issues. Browser-based clients may hit CORS errors if the server doesn't include proper
Access-Control-Allow-Originheaders
Session Drops
Streamable HTTP uses the Mcp-Session-Id header for session continuity. If sessions keep dropping:
- Check if your reverse proxy or load balancer is stripping custom headers
- Verify the server's session timeout isn't too aggressive
- For stateless deployments, make sure session state is stored externally (Redis, Durable Objects) rather than in-memory
Performance Issues
- Cold starts. Serverless platforms (Lambda, Cloud Functions) can add 1-5 seconds of latency on the first request. Use provisioned concurrency or warm-up pings if response time matters
- Large responses. MCP messages with large payloads (file contents, long tool outputs) can be slow over high-latency connections. Consider streaming responses via SSE for large results
- Connection pooling. If your client makes frequent requests, reuse the HTTP connection rather than opening a new one for each call
Frequently Asked Questions
Can MCP servers run remotely?
Yes. MCP servers support remote operation through Streamable HTTP transport, which sends JSON-RPC messages over standard HTTPS. You can deploy an MCP server on any cloud platform (Cloudflare Workers, Google Cloud Run, Azure Functions, or your own VPS) and connect to it from any MCP-compatible client. The key requirement is proper authentication and HTTPS encryption, since remote servers are network-accessible.
How do I connect Claude to a remote MCP server?
In Claude Desktop, go to Settings > Connectors > Add custom connector and enter the remote server's URL. For SSE-only servers, use the mcp-remote npm package as a bridge in your claude_desktop_config.json. In Claude Code (CLI), add the server URL directly to your MCP configuration with an Authorization header for API key authentication.
What is the difference between Streamable HTTP and SSE transport?
Streamable HTTP uses a single endpoint for both requests and responses, with optional SSE streaming for long-running operations. The older SSE transport (now deprecated) required two separate endpoints, one for sending requests and one for receiving the event stream. Streamable HTTP works better with standard HTTP infrastructure like load balancers, CDNs, and API gateways because it follows standard request/response patterns.
Is it safe to expose an MCP server to the internet?
It can be, but only with proper security measures. At minimum, you need HTTPS encryption, authentication (OAuth 2.1, API keys, or mTLS), origin header validation, rate limiting, and input validation on all tool parameters. Without these, anyone who discovers your server URL could execute any tool it provides. The OWASP project maintains a dedicated cheatsheet for securing MCP servers.
Do I need to build my own remote MCP server for file operations?
Not necessarily. Hosted MCP servers like Fastio provide 19 consolidated tools for file management, search, AI-powered document Q&A, and more. The free agent tier includes 50GB storage and 5,000 monthly credits with no credit card required. Building your own server makes sense when you need custom tools for specific business logic, databases, or internal APIs.
Related Resources

Give Your AI Agents Persistent Storage
Fastio gives teams shared workspaces, MCP tools, and searchable file context to run remote mcp server workflows with reliable agent and human handoffs.
