How to Automate Workflows with OpenClaw Webhooks on Raspberry Pi
A Raspberry Pi running OpenClaw as a systemd service becomes an always-on AI agent that responds to webhook triggers and runs scheduled tasks. This guide covers webhook endpoint configuration, cron job scheduling, secure tunnel exposure, and connecting agent output to shared workspaces.
Why Run OpenClaw Webhooks on a Raspberry Pi
OpenClaw webhook automation on Raspberry Pi creates an always-on event listener that triggers AI agent workflows in response to incoming HTTP requests, scheduled cron jobs, or external service notifications.
A Raspberry Pi draws around 5 watts at idle. That makes it a cheap, quiet server for running an OpenClaw gateway 24/7. The gateway exposes HTTP webhook endpoints that accept POST requests from external services like GitHub, Stripe, or smart home hubs. When a request arrives, OpenClaw routes it to the right agent session and executes the configured action.
The combination matters because most webhook-driven automations need a server that is always listening. Cloud VMs work but cost money monthly. A Pi sitting on your desk handles the same job for the one-time hardware cost, and it stays on your local network where you control the data.
Generic webhook guides typically cover either the HTTP server side or the AI agent side, but not both together. OpenClaw bridges that gap by running the gateway, the webhook listener, and the agent runtime in a single process managed by systemd.
Setting Up OpenClaw as a systemd Service
Before configuring webhooks, you need OpenClaw running as a persistent service that survives reboots. The official Raspberry Pi documentation recommends a systemd unit file.
Install OpenClaw on your Pi following the official Raspberry Pi guide. The onboarding wizard handles API key configuration and optional skill installation:
openclaw onboard --install-daemon
For manual service setup, create a unit file at /etc/systemd/system/openclaw.service:
[Unit]
Description=OpenClaw Gateway
After=network.target
[Service]
Type=simple
User=pi
WorkingDirectory=/home/pi
ExecStart=/usr/local/bin/openclaw gateway start
Restart=always
RestartSec=5
[Install]
WantedBy=multi-user.target
Enable and start the service:
sudo systemctl daemon-reload
sudo systemctl enable openclaw
sudo systemctl start openclaw
Verify the gateway is running with sudo systemctl status openclaw and check logs with journalctl -u openclaw -f. The Restart=always directive means the service restarts automatically if it crashes or the Pi reboots.
The gateway dashboard is accessible at http://<PI_IP>:18789/ for monitoring and configuration. For remote access without exposing ports, the OpenClaw docs recommend Tailscale or a Cloudflare Tunnel.

Configuring Webhook Endpoints
OpenClaw's gateway includes a built-in HTTP webhook server. Enable it in your gateway configuration with a shared secret token:
{
"hooks": {
"enabled": true,
"token": "your-dedicated-hook-token",
"path": "/hooks",
"allowedAgentIds": ["hooks", "main"]
}
}
The token field is mandatory. Every incoming request must include it via Authorization: Bearer <token> header. Query-string tokens are rejected.
OpenClaw exposes two main webhook endpoint types:
Wake endpoint (POST /hooks/wake) enqueues a system event for the main session. Send a JSON payload with a text field describing the event:
{ "text": "New file uploaded to project folder", "mode": "now" }
The mode field accepts now (process immediately) or next-heartbeat (wait for the next scheduled heartbeat cycle).
Agent endpoint (POST /hooks/agent) runs an isolated agent turn. This is where the real automation power lives. The payload supports several parameters:
message(required): The prompt or instruction for the agentagentId: Route to a specific agent configurationchannel: Deliver the response to a messaging channel (Slack, Telegram, Discord, and others)model: Override the default LLM modeltimeoutSeconds: Set a maximum execution duration
For example, a GitHub webhook could trigger a code review agent:
{
"message": "Review the latest PR diff and summarize changes",
"agentId": "code-reviewer",
"channel": "slack",
"to": "channel:C1234567890"
}
Keep the webhook token separate from your gateway auth token. The OpenClaw security docs recommend running a dedicated hook agent with restricted tool permissions and sandboxing.

Give Your Pi's Agent Output a Permanent Home
Fastio workspaces store, index, and share everything your OpenClaw agent produces. 50GB free storage, built-in semantic search, and no credit card required.
Scheduling Recurring Tasks with Cron Jobs
Webhooks handle event-driven triggers. For time-based automation, OpenClaw includes a built-in cron scheduler that persists jobs at ~/.openclaw/cron/ so schedules survive gateway restarts.
Enable cron in your gateway configuration:
{
"cron": {
"enabled": true,
"maxConcurrentRuns": 1,
"sessionRetention": "24h",
"retry": {
"maxAttempts": 3,
"backoffMs": [60000, 120000, 300000],
"retryOn": ["rate_limit", "overloaded", "network", "server_error"]
}
}
}
Three schedule types are supported:
- at: One-shot execution at an ISO 8601 timestamp
- every: Fixed intervals in milliseconds
- cron: Standard 5 or 6-field cron expressions with optional IANA timezone
Create a recurring morning briefing that runs at 7 AM Pacific:
openclaw cron add --name "Morning brief" \
--cron "0 7 * * *" --tz "America/Los_Angeles" \
--session isolated \
--message "Summarize overnight updates." \
--announce --channel slack --to "channel:C1234567890"
The --session isolated flag runs each job in a dedicated agent turn, keeping it separate from your main session context.
Cron jobs support three delivery modes.
Announce sends the result to a messaging channel.
Webhook posts the finished event payload to an external URL, which is useful for chaining automations.
None runs internally without any output delivery.
For webhook delivery on a cron job, set the delivery mode and target URL:
{
"delivery": {
"mode": "webhook",
"to": "https://your-endpoint.example.com/results"
}
}
This hybrid pattern, cron triggering a job that delivers via webhook, connects your Pi's scheduled tasks to downstream systems without manual intervention.

Exposing Webhooks to the Internet
Your Pi's webhook endpoints are only reachable on the local network by default. External services like GitHub or Stripe need a public URL to send requests to. Three common approaches solve this.
Cloudflare Tunnel creates an outbound-only connection from your Pi to Cloudflare's network. No ports are opened on your home router. Install cloudflared, authenticate it with your Cloudflare account, and create a tunnel pointing to the OpenClaw gateway port. This is the recommended production approach because Cloudflare handles TLS, DDoS protection, and access policies.
Tailscale connects your Pi to a private mesh network. Other devices on your tailnet can reach the webhook endpoints directly. This works well when the webhook source is another machine you control, but it does not help with third-party services that need a public URL.
ngrok is the fastest option for development and testing. There is an unofficial OpenClaw skill that starts a local webhook server and opens an ngrok tunnel automatically, printing the public URL. For quick testing without installing extra skills, run ngrok http 18789 and use the generated URL as your webhook target.
Whichever method you choose, keep the OpenClaw webhook token mandatory. The gateway rejects unauthenticated requests and rate-limits repeated auth failures per client address. For additional safety, restrict allowedAgentIds in your hooks configuration so only designated agents can process incoming webhooks.
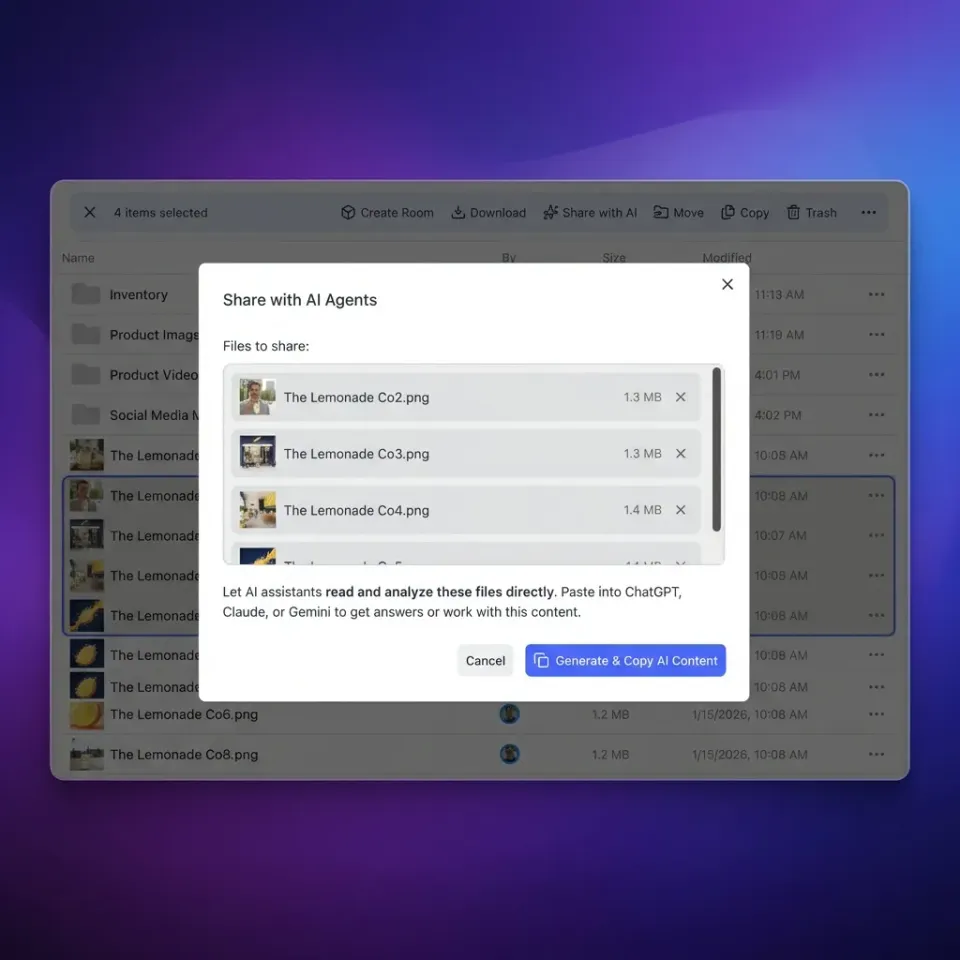
Connecting Agent Output to Shared Workspaces
A Pi-based webhook automation is useful on its own, but the output often needs to reach a team. When your OpenClaw agent generates reports, summaries, or processed files, those artifacts need a home where collaborators can find them.
Fastio workspaces give agents a persistent place to store and share output. The free agent tier includes 50GB of storage, 5,000 monthly credits, and 5 workspaces with no credit card required. Agents access workspaces through the Fastio MCP server or API, while teammates use the web interface.
A practical pattern: your Pi's cron job runs a daily research summary, the OpenClaw agent writes the output to a Fastio workspace, and your team finds it indexed and searchable the next morning. Intelligence Mode auto-indexes uploaded files for semantic search, so the workspace becomes a queryable knowledge base over time.
For reactive workflows, Fastio webhooks notify your agents when files change in a workspace. Combined with OpenClaw's inbound webhooks on your Pi, you get a bidirectional loop: external events trigger your agent, your agent stores results in Fastio, and Fastio notifies downstream agents or humans when new content arrives.
Other storage options work too. Local storage on the Pi's SD card is fine for ephemeral output, but SD cards wear out under heavy writes and offer no collaboration features. S3-compatible storage handles durability but requires managing access keys and lacks built-in semantic search. Fastio sits between these, offering durable cloud storage with built-in intelligence and a workspace model designed for agent-to-human handoff through ownership transfer.
Frequently Asked Questions
Does OpenClaw support webhooks on Raspberry Pi?
Yes. The OpenClaw gateway includes built-in webhook endpoints that work on any platform where the gateway runs, including Raspberry Pi. Enable webhooks in the gateway configuration with a shared token, and the gateway listens for incoming HTTP POST requests on the configured path.
How do I set up cron jobs in OpenClaw?
Enable cron in your gateway configuration and use the CLI to add jobs. The command "openclaw cron add" accepts schedule parameters (cron expressions, fixed intervals, or one-shot timestamps), a message prompt, session type, and delivery options. Jobs persist at ~/.openclaw/cron/ and survive gateway restarts.
Can I trigger OpenClaw agents with HTTP requests?
Yes. The /hooks/agent endpoint accepts POST requests with a JSON payload containing a message field. You can specify which agent handles the request, which messaging channel receives the response, and execution parameters like model override and timeout. Every request must include the configured hook token for authentication.
How do I expose OpenClaw webhooks on a Pi to the internet?
Use Cloudflare Tunnel for production setups, Tailscale for private mesh networking, or ngrok for development testing. Cloudflare Tunnel creates an outbound-only connection without opening ports on your router. All methods keep the OpenClaw token authentication layer intact.
Can I combine webhooks and cron jobs in OpenClaw?
Yes. Cron jobs can deliver results via webhook by setting the delivery mode to "webhook" with a target URL. This creates hybrid automations where scheduled tasks trigger downstream services. Inbound webhooks and scheduled cron jobs run through the same gateway process on your Pi.
What Raspberry Pi model do I need for OpenClaw?
The Raspberry Pi 5 is recommended for running OpenClaw with comfortable headroom. Older models like the Pi 4 work but may struggle with resource-intensive agent tasks. The gateway itself is lightweight, but LLM API calls and skill execution benefit from the Pi 5's faster ARM processor.
Related Resources

Give Your Pi's Agent Output a Permanent Home
Fastio workspaces store, index, and share everything your OpenClaw agent produces. 50GB free storage, built-in semantic search, and no credit card required.
