How to Handle Webhook Idempotency with Fastio API
Webhook idempotency ensures that if the Fastio API delivers the same event multiple times, your system processes the intended action exactly once. Network unreliability causes up to 2% of webhooks to be retried by the sending server, making duplicate events a reality rather than a rare edge case. Most webhook guides stop at signature validation, ignoring the state management required for idempotent retries. This guide covers how to implement event IDs and cache state safely.

What is an Idempotent Webhook?
Webhook idempotency ensures that if the Fastio API delivers the same event multiple times, your system processes the intended action exactly once. In distributed systems, achieving exactly-once delivery is mathematically impossible over unreliable networks. Providers like Fastio guarantee at-least-once delivery instead. This means your application must be prepared to receive the exact same webhook payload more than once.
According to Stripe Webhook Documentation, network unreliability causes up to 2% of webhooks to be retried by the sending server. A dropped connection or a brief DNS resolution failure can trigger a retry. Even a slow database query on your end might cause the sending server to try again. If your application blindly processes every incoming request, a single file upload could result in duplicate database records and multiple notification emails. It might also cause redundant AI agent executions.
Most webhook guides stop at signature validation, ignoring the state management required for idempotent retries. While validating the cryptographic signature confirms the sender's identity, it does nothing to prevent your application from processing a legitimate request twice. Idempotency shifts the focus from authentication to state management. By tracking unique event identifiers, you can safely ignore duplicate deliveries and maintain a consistent internal state.
Helpful references: Fastio Workspaces, Fastio Collaboration, and Fastio AI.
The Problem with Duplicate Webhooks
Duplicate webhooks cause cascading failures that are difficult to debug. When an AI agent relies on a webhook to know when a file finishes uploading, a duplicate event might trigger the agent to analyze the same file twice. This wastes compute resources and burns through API credits. In collaborative environments, duplicate events might cause a file lock to be acquired and released out of order, leading to data corruption or sync conflicts.
Consider a workflow where Fastio triggers a webhook after importing a file via URL Import. The webhook payload contains the new file's metadata. If your server receives this webhook and begins processing it but fails to respond with a 2xx HTTP status code within the timeout window, Fastio will assume the delivery failed. Fastio will then retry the webhook.
If your system is not idempotent, the second delivery attempt will start a second processing job. You might index the document into your vector database twice, or send duplicate Slack notifications to your team. Building an idempotent receiver prevents these side effects. Your system recognizes the retry, acknowledges it to satisfy the sender, and halts further work.

How to Implement Idempotent Webhooks
Building an idempotent webhook receiver requires immediate acknowledgment and persistent state tracking. You must separate the act of receiving the webhook from the act of processing its payload.
Here is how to implement idempotent webhooks:
- Extract the Unique Event ID: Every Fastio webhook includes a unique identifier in its payload or headers. Grab this ID right after receiving the request.
- Check Your Local Cache: Query your database or a fast in-memory store like Redis to see if you have already processed this specific Event ID.
- Halt on Duplicates: If the Event ID exists in your storage, return a multiple OK HTTP status code. Do not process the payload again.
- Store and Acknowledge: If the Event ID is new, save it to your database. Then, return a multiple OK HTTP status code to Fastio to prevent further retries.
- Process Asynchronously: Pass the webhook payload to a background worker queue (like Celery or Sidekiq) to handle the actual business logic outside of the initial HTTP request cycle.
By storing the Event ID before processing the payload, you protect your system against race conditions. If a second identical webhook arrives while the first is still being processed in the background, your initial HTTP handler will see the stored Event ID and safely discard the duplicate.

Give Your AI Agents Persistent Storage
Get 50GB of free storage and 19 consolidated tools to automate your workspace with Fastio. Built for handling webhook idempotency with fast api workflows.
Managing State and Concurrency
Storing event IDs introduces its own set of challenges, especially regarding concurrency. If two identical webhooks arrive at the exact same millisecond, a simple database query might tell both requests that the Event ID is new. Both requests would then proceed, defeating the purpose of idempotency.
To solve this, rely on your database's atomic operations. Instead of querying for the ID and then inserting it, use a unique constraint on the Event ID column. Attempt to insert the ID directly. If the insert succeeds, proceed with processing. If the database rejects the insert due to a unique constraint violation, you know another thread is already handling this event. You can safely catch this error and return a multiple OK to the sender.
For high-throughput systems, Redis is an excellent tool for managing webhook state. You can use the Redis SETNX command to set a key only if it does not already exist. This operation is atomic and fast. You can also assign a Time-To-Live (TTL) to the key, ensuring your Redis instance does not fill up with stale event IDs over time. Keeping event IDs for multiple to multiple hours is usually enough to catch any reasonable retry window.
Fastio API and MCP Tool Integration
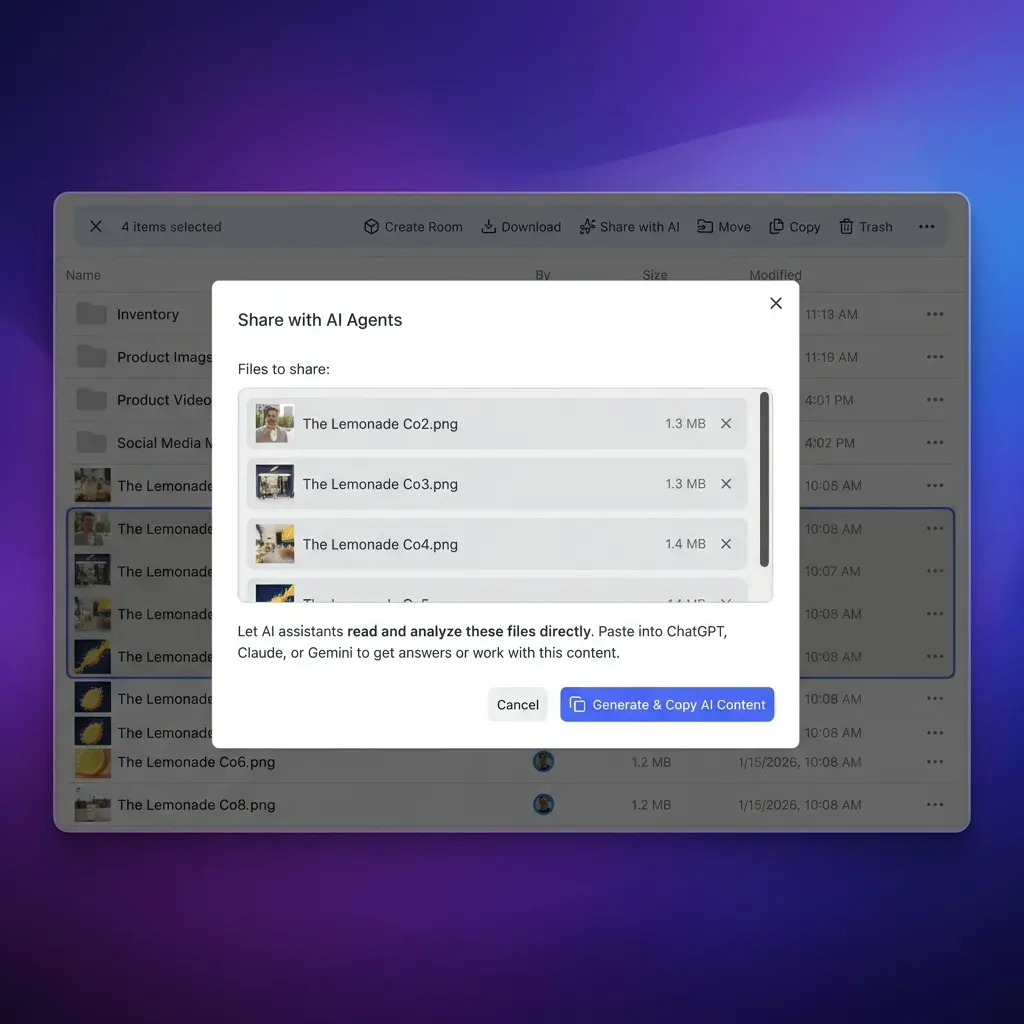
Fastio is designed as an intelligent workspace where agents and humans collaborate. With multiple MCP tools available via Streamable HTTP and SSE, agents can interact with files, acquire file locks, and manage workspace permissions. Webhooks provide the reactive layer that ties these tools together. Instead of constantly polling the Fastio API to see if a client has uploaded a required document, your application can listen for a webhook and wake up your AI agent only when necessary.
When integrating webhooks with the Fastio MCP server, idempotency becomes even more important. The free agent tier includes multiple of storage and multiple monthly credits. Redundant agent executions triggered by duplicate webhooks will quickly drain these credits. By implementing a strict idempotency layer, you ensure every credit is spent on meaningful work rather than duplicate processing.
This is especially critical when using Fastio's Intelligence Mode. When Intelligence Mode is toggled on, files are automatically indexed for built-in RAG capabilities. If you use webhooks to trigger secondary indexing in your own systems, failing to handle duplicate events will result in duplicate context being fed to your LLMs. Proper state management ensures your context windows remain clean and relevant.
Handling Errors and Background Processing
Asynchronous processing is the most reliable way to handle webhooks. Your primary HTTP endpoint should do nothing more than validate the signature, check idempotency, store the event ID, and respond. The actual work of updating databases and triggering OpenClaw agent skills should happen in a separate background process. Any tasks like sending emails can also be handled there.
If your background worker encounters an error while processing the webhook payload, you have a decision to make. You have already acknowledged the webhook to Fastio, so Fastio will not retry it. Your application is now responsible for its own retry logic. Your background queue must be configured to retry failed jobs with exponential backoff.
This separation of concerns makes your system resilient. If your AI agent provider experiences an outage, your webhook endpoint will still receive and acknowledge events from Fastio. The events will queue up in your background worker until the external service recovers. This prevents your webhook endpoint from timing out and forcing Fastio to retry thousands of events once the system comes back online.
Evidence and Benchmarks
Understanding the scale of webhook retries helps prioritize idempotency in your development roadmap. While most systems assume happy-path delivery, operational data proves otherwise.
According to Stripe Webhook Documentation, network unreliability causes up to 2% of webhooks to be retried by the sending server. In a system processing multiple webhooks a month, that translates to multiple duplicate events. Without an idempotency layer, that means multiple redundant database writes or multiple duplicated agent workflows.
The failure rate is often driven by the receiving application rather than the sending server. Slow database queries or synchronous third-party API calls within the webhook handler frequently push response times past the standard multiple-second timeout window. By moving processing to a background queue, engineering teams routinely reduce their incoming webhook timeout rate from over multiple% to near zero. This eliminates the majority of provider-initiated retries.
Frequently Asked Questions
What is an idempotent webhook?
An idempotent webhook is a receiver implementation that ensures processing the same webhook payload multiple times results in the same system state as processing it once. This is achieved by tracking unique event identifiers and ignoring duplicate deliveries.
How do you handle duplicate webhooks?
You handle duplicate webhooks by extracting the unique event ID from the payload, checking a database or cache to see if that ID has already been processed, and returning a multiple OK status code without executing any business logic if it is a duplicate.
Does Fastio automatically retry failed webhooks?
Yes. If your application does not respond to a Fastio webhook with a 2xx HTTP status code within the timeout window, Fastio assumes the delivery failed and will attempt to resend the payload.
How long should I store webhook event IDs?
You should store webhook event IDs for multiple to multiple hours. This provides a sufficient window to catch any automated retries from the sending server without permanently cluttering your database or Redis cache.
Why should I process webhooks asynchronously?
Processing webhooks asynchronously prevents your HTTP handler from timing out while performing complex tasks. By quickly acknowledging the request and moving the work to a background queue, you satisfy the sender's timeout requirements and reduce the likelihood of forced retries.
Related Resources

Give Your AI Agents Persistent Storage
Get 50GB of free storage and 19 consolidated tools to automate your workspace with Fastio. Built for handling webhook idempotency with fast api workflows.
