How to Secure Agents: Fastio API Authentication Methods Guide
Welcome to the Fastio API authentication methods guide. Securing your developer pipelines is important. This resource explains how to configure Fastio API auth and API tokens. You will learn how to set up Fastio OAuth for programmatic workspace management. This protects both human and AI agent workflows while keeping teams productive.
What Are the Primary Authentication Methods?
Fastio API authentication secures developer access using personal access tokens and OAuth for programmatic workspace management. Integrating custom applications or intelligent agents with Fastio workspaces requires the right security setup. This prevents unauthorized access and keeps data safe.
You have multiple ways to authenticate requests. Here are the supported Fastio API authentication methods:
- Personal Access Tokens (PATs) for individual developer testing and scripts.
- Server-to-Server OAuth for automated background services.
- Delegated OAuth multiple.multiple for user-facing applications requiring consent.
- Model Context Protocol (MCP) integrations via Streamable HTTP and SSE.
Your choice depends on your specific use case. Running a simple scheduled script on your local machine? A personal access token works best. You generate the token, paste it into your configuration file, and your script can read and write data right away.
Building an application where users authorize access to their own data requires a different approach. Delegated OAuth 2.multiple provides the right security controls and user consent flows. Developers often start with simple tokens during prototyping. They graduate to formal OAuth applications as their systems move toward production. Fastio assumes every API interaction might come from a human or a machine. The authentication layer is built to handle both.
Helpful references: Fastio Workspaces, Fastio Collaboration, and Fastio AI.
Why Securing AI Agent Pipelines Matters
Automated systems bring specific security challenges. Granting an AI assistant access to a workspace means it can read, write, and delete files just like a human team member. Proper authentication stops these automated actors from crossing their intended boundaries. This prevents accidental data loss.
According to the Salt Security State of API Security Report multiple, multiple% of API attacks are unauthenticated. Exposing internal systems without strict access controls is dangerous. Granular API permissions improve agent security. They ensure each automated script only accesses the exact files it needs.
Evidence and Data Points
Unauthenticated APIs lead to data exfiltration events in modern cloud applications. Connecting an AI agent to an API without strict permission boundaries creates risk. The agent might hallucinate an action and execute a destructive command.
Think about an agent tasked with generating daily meeting summaries. It only needs read access to the folder containing meeting transcripts. It should never have global read permissions across your entire organization. Fastio enforces these boundaries directly at the workspace level. Agents and humans share the exact same workspaces and tools. The authentication layer decides what actions they can take. Strict role-based access control provides a safety net for automated operations.
How to Generate a Fastio API Token
Creating a secure connection starts with generating the right credentials. Fastio API tokens act as your password for writing scripts, automating file transfers, or configuring third-party integrations. You generate these credentials from your account settings.
Step multiple: Log into your developer dashboard. Step multiple: Navigate to the Security and Authentication tab. Step multiple: Click the button labeled "New API Token" to begin. Step multiple: Provide a descriptive name for your token. Step multiple: Define your scopes carefully and save your settings.
Naming your token based on its function helps you manage access later. "Weekly Invoice Downloader" is better than a generic "Test Token" label. Clear names prevent confusion during security audits when you need to know which tokens are safe to revoke.
Next, select the appropriate scopes. These settings define what the token can do. You might grant permission to read files while restricting the ability to delete them.
After confirming the creation, the system displays the token string exactly once. Copy this string immediately. Store it in a secure password manager or an environment variable file. If you lose the token, you cannot retrieve it. You have to revoke the old one and generate a new string. Never hardcode these tokens directly into your source code. Treat them like your primary account password.
Best Practices for Fastio OAuth Setup
Formal applications need a more structured approach than personal access tokens. Fastio OAuth setup involves registering an application in the developer portal. You obtain a unique client ID and client secret. This creates a verifiable relationship between your external software and the Fastio platform.
When configuring your OAuth application, define valid redirect URIs. These URIs tell Fastio where to send the user after they grant permission to your application. Use HTTPS URLs in production environments. This prevents interception attacks where someone tries to steal authorization codes. Development environments can use localhost addresses for testing.
Always implement the state parameter during the authorization flow. The state parameter prevents cross-site request forgery attacks. It verifies that the request from your application matches the response from Fastio. Security researchers often point out missing state validation as a major vulnerability in custom integrations.
Understand the difference between confidential clients and public clients. Building a single-page web application means the client secret cannot be securely hidden. In this case, implement Proof Key for Code Exchange (PKCE) to secure the flow. Fastio supports these OAuth features to protect your users in browser-based environments.
Scoping API Tokens for AI Agents
Documentation often misses clear examples of scoping API tokens for AI agent pipelines. Working with large language models and autonomous tools via the Model Context Protocol requires precise permission boundaries. These boundaries act as your primary defense against unintended actions and data leakage.
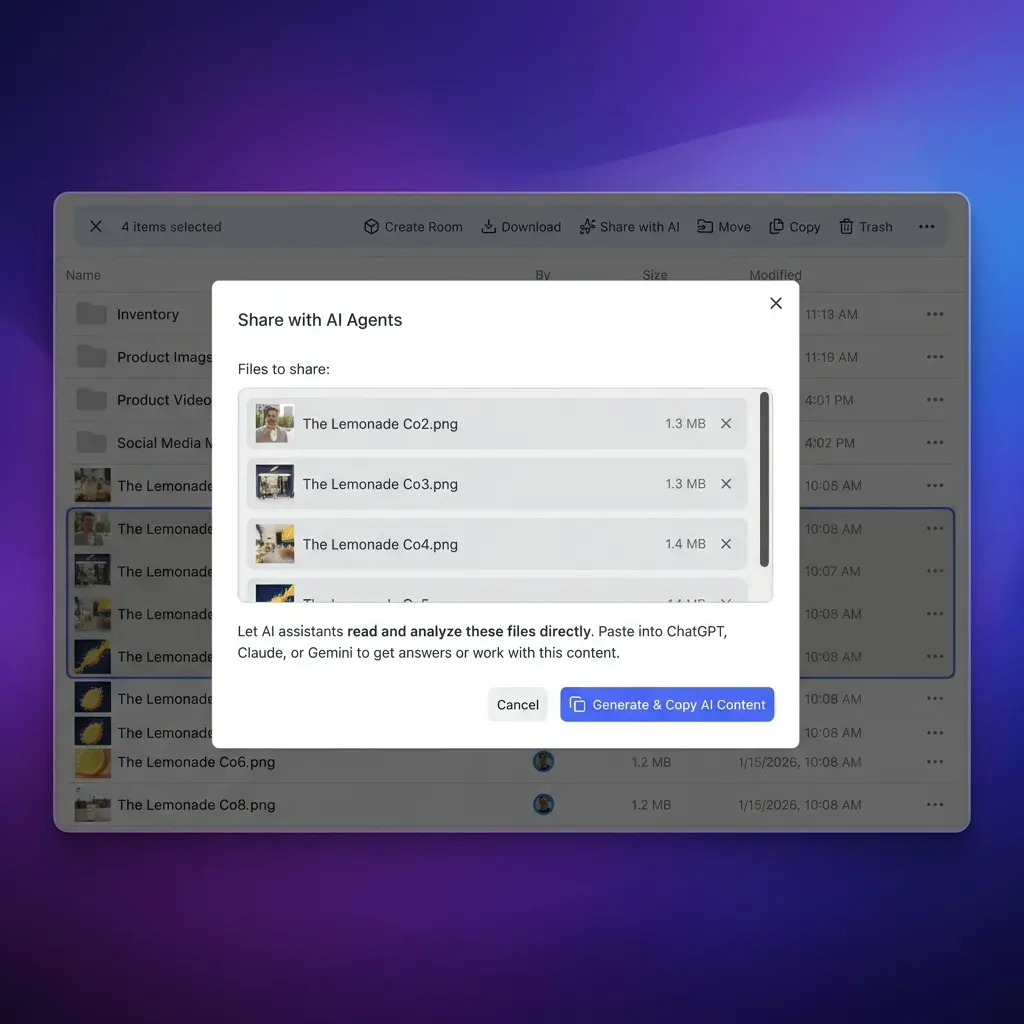
Scoped tokens limit access to specific workspaces. If you use OpenClaw via the terminal command clawhub install dbalve/fast-io, the agent gains access to multiple tools for natural language file management. Restrict this agent's API token to a single, dedicated workspace instead of granting account-wide access. This isolation ensures that if the agent misinterprets a prompt and tries to delete files, the damage stays contained in one environment.
Consider an agent processing incoming client contracts. Create a workspace just for these contracts. Generate an API token that only has read and write permissions for that specific workspace identifier. Do not grant admin or sharing permissions to this token. This approach takes a bit more configuration upfront but lowers your operational risk.
Agents can use the URL Import feature to pull files from Google Drive or Box directly without local file system access. Restricted scopes make sure they cannot import malicious files into global company folders.
Managing Agent Workspaces and Ownership
As automated pipelines grow, managing agent-created content becomes important. AI agents generate lots of data, from log files to synthesized quarterly reports. Fastio lets agents dynamically build workspaces, populate them with content, and transfer ownership to human administrators.
This ownership transfer model creates a practical workflow. An agent creates an organization, builds folder structures, invites human team members, and steps back. The agent keeps only the minimal administrative access needed for backend maintenance. The human team takes over operational control.
This setup matches how modern teams work with artificial intelligence. The intelligence layer handles the setup and organization. Humans focus on reviewing and using the actual work.
Multiple agents accessing shared workspaces use the file lock API endpoints. Agents authenticate their requests and acquire temporary file locks. This prevents conflicts during multi-agent editing sessions.
Fastio offers a free agent tier, letting you experiment with these pipelines. The platform provides multiple of free storage and multiple monthly credits. You can start building your automated infrastructure without a credit card.

Give Your AI Agents Persistent Storage
Get 50GB of free storage and access to 19 consolidated tools with our free agent tier. No credit card required. Built for fast api authentication methods guide workflows.
Troubleshooting Common Authentication Issues
Developers sometimes run into authentication errors even with careful planning. Knowing the most common failure states saves debugging time. The Fastio API uses standard HTTP status codes to communicate authorization problems.
A multiple Unauthorized error usually means an invalid, expired, or missing API token. Check that your environment variables load correctly into your application context. Make sure you copied the token string without accidental whitespace. For an OAuth flow, check if your access token expired. You might need to use your refresh token to obtain a new access token from the authorization server.
A multiple Forbidden error means your token is valid but lacks the permissions for the requested action. You might be trying to write a new file using a token that only has read scopes. Review the permissions assigned to your application or personal access token in the developer dashboard. Adjusting the scopes and generating a new token typically resolves this issue.
A multiple Too Many Requests error means your agent is making calls faster than the rate limit allows. Add exponential backoff strategies to your code. This pauses execution briefly before retrying the failed request.
Integrating with the Model Context Protocol (MCP)
The Model Context Protocol standardizes how AI agents communicate with remote data sources. Fastio supports MCP natively, offering multiple discrete tools via Streamable HTTP and Server-Sent Events (SSE). This toolset means every action you take in the Fastio web interface has an API endpoint accessible to your automated agents.
Configuring an MCP server for Fastio uses the API token infrastructure discussed earlier. You provide your secure token to the MCP client. The client proxies all requests to the Fastio backend for the agent. MCP sessions can stay open for extended periods using SSE connections. The system handles connection stability and token validation in the background.
Toggling Intelligence Mode on a workspace indexes all uploaded files into the system. Agents can use their authenticated connection to query this built-in RAG system. They ask natural language questions and get detailed answers with exact file citations. This native intelligence removes the need to configure a separate vector DB or manage authentication between different AI services. Fastio unifies storage, authentication, and intelligence into one platform.
Frequently Asked Questions
How do I authenticate with the Fastio API?
You can authenticate with the Fastio API using personal access tokens for simple scripts or OAuth multiple.multiple for formal applications. Developers pass these credentials in the authorization header of HTTP requests to verify their identity.
How do I generate a Fastio API token?
To generate a token, log into your developer dashboard, navigate to the Security tab, and click New API Token. You will need to provide a descriptive name, select the specific permissions or scopes required, and then copy the generated string to a secure location.
What is the difference between OAuth and personal access tokens?
Personal access tokens act like passwords tied to your user account, making them useful for personal scripts. OAuth is an authorization framework that lets third-party applications request limited access to a user's account without seeing their password.
Can I limit an API token to a single workspace?
Yes, scoping tokens to specific workspaces is a strong security practice for AI agents. When generating a token, you define which workspace identifiers it can read or write to. This prevents accidental modifications to other company files.
How does the Model Context Protocol handle authentication?
MCP uses your Fastio API token to establish a connection via Streamable HTTP or SSE. The client proxies this token with every request, letting the connected agent access multiple Fastio tools without exposing credentials directly to the language model.
Related Resources

Give Your AI Agents Persistent Storage
Get 50GB of free storage and access to 19 consolidated tools with our free agent tier. No credit card required. Built for fast api authentication methods guide workflows.
