How to Implement AI Agent Storage Encryption
As autonomous systems take on more responsibility, securing their persistent data has become a critical challenge. AI agent storage encryption protects persistent memory and tools from unauthorized access, ensuring that sensitive context remains private. This guide covers the essential strategies for encrypting agent data, from at-rest protection to securing MCP-integrated multi-agent workflows.
What is AI Agent Storage Encryption?
AI agent storage encryption protects persistent memory and tools from unauthorized access. When autonomous agents operate over extended periods, they accumulate vast amounts of sensitive context—including conversation histories, downloaded files, API keys, and intermediate reasoning steps. Without proper encryption, this persistent state becomes a prime target for attackers.
Unlike traditional application data, agent memory often contains unstructured, unpredictable information gathered dynamically during execution. This unpredictability makes robust storage encryption not just a compliance checkbox, but a foundational requirement for safe agentic operations. Implementing encryption at the storage layer ensures that even if the underlying infrastructure is compromised, the agent's memory and operational context remain unreadable.
Modern approaches require securing data both at rest and in transit. This is especially true for systems that rely on the Model Context Protocol (MCP), where agents continuously exchange context with external servers. Proper encryption ensures that this continuous flow of data remains confidential, protecting the integrity of the agent's decision-making process. By establishing a secure perimeter around the agent's working memory, organizations can deploy autonomous systems with confidence, knowing that sensitive corporate data will not be exposed through insecure storage mechanisms.
The Growing Threat to Agent Persistence
The rapid adoption of autonomous workflows has expanded the attack surface for enterprise networks. As agents are granted access to internal databases, email systems, and financial records, the data they store locally or in cloud persistence layers becomes highly valuable. Attackers no longer need to breach the primary database; they simply need to compromise the agent's intermediate storage cache where data is temporarily held for processing.
According to recent security analyses, agent data breaches rose 40% in 2025. This surge is driven by attackers specifically targeting the intermediate storage layers where agents cache their context. When an agent is compromised, the attacker gains not only the stored data but also the agent's active permissions, execution capabilities, and historical reasoning logs. This provides malicious actors with a comprehensive map of the organization's internal workflows and vulnerabilities.
The vulnerability is compounded in multi-agent systems. When multiple agents collaborate and share workspaces, the state is often written to shared storage volumes. If these volumes lack robust encryption, a single compromised agent can expose the entire system's memory. Securing this persistence layer is critical to preventing lateral movement within agentic networks. It requires moving beyond standard perimeter defenses and adopting a zero-trust model where every read and write operation is authenticated and encrypted.
The Missing Piece: MCP-Integrated Encryption
Most traditional guides on securing AI workflows focus heavily on API key management and securing the LLM prompt layer. However, these guides overlook MCP-integrated encryption for multi-agent systems. The Model Context Protocol (MCP) provides a standardized way for agents to access external tools and data, but it also creates continuous data streams that must be secured at the persistence layer. Without MCP-integrated encryption, the tools themselves become vulnerabilities.
When using MCP, agents frequently read and write to shared storage environments. If this storage is not natively encrypted, the tools become vulnerable to state-manipulation attacks, where an attacker modifies the stored context to alter the agent's future behavior. Fastio addresses this gap by providing an intelligent workspace where encryption is built into the foundation. With 19 consolidated tools available via Streamable HTTP and SSE, Fastio ensures that every read, write, and state update is protected cryptographically.
Also, Fastio's architecture supports secure ownership transfer. An agent can create an organization, build out secure workspaces, populate them with encrypted context, and then seamlessly transfer ownership to a human user—all while maintaining the strict encryption boundary. This MCP-native approach ensures that multi-agent coordination happens within a zero-trust, fully encrypted environment, solving the complex challenge of secure human-agent collaboration.

Secure Your AI Agents Today
Get 50GB of free encrypted storage and access to 19 consolidated tools to build secure, multi-agent workflows.
Core Architectural Patterns for Secure Persistence
Designing a secure persistence layer for AI agents requires implementing specific architectural patterns that prioritize encryption and access control at every stage of the data lifecycle. The first pattern is Ephemeral Context Segregation. Agents should separate their short-term working memory from long-term persistent storage. Short-term memory should be stored in highly secure, volatile environments that are wiped upon task completion, while long-term storage must be subjected to rigorous at-rest encryption protocols using AES-256 or equivalent standards.
The second pattern is Cryptographic State Verification. It is not enough to simply encrypt the data; the system must also verify that the encrypted state has not been tampered with. Implementing cryptographic hashes or digital signatures alongside the encrypted payloads ensures that if an attacker attempts to modify the stored context, the agent will detect the anomaly and halt execution before processing corrupted data. This prevents prompt injection attacks that rely on modifying the agent's stored history.
The third essential pattern is Granular Capability Scoping. Access to the encrypted storage should be strictly limited based on the principle of least privilege. An agent should only be able to decrypt the specific data required for its current task. By compartmentalizing the encrypted storage and issuing scoped decryption keys, organizations can severely limit the blast radius if an individual agent or a specific key is compromised.
Implementing Encryption in Multi-Agent Workflows
Multi-agent workflows introduce unique challenges for storage encryption due to the need for concurrent access and state synchronization. When multiple autonomous entities operate simultaneously, they often need to read from and write to the same encrypted data stores. Managing this securely requires sophisticated coordination mechanisms that do not compromise the underlying encryption.
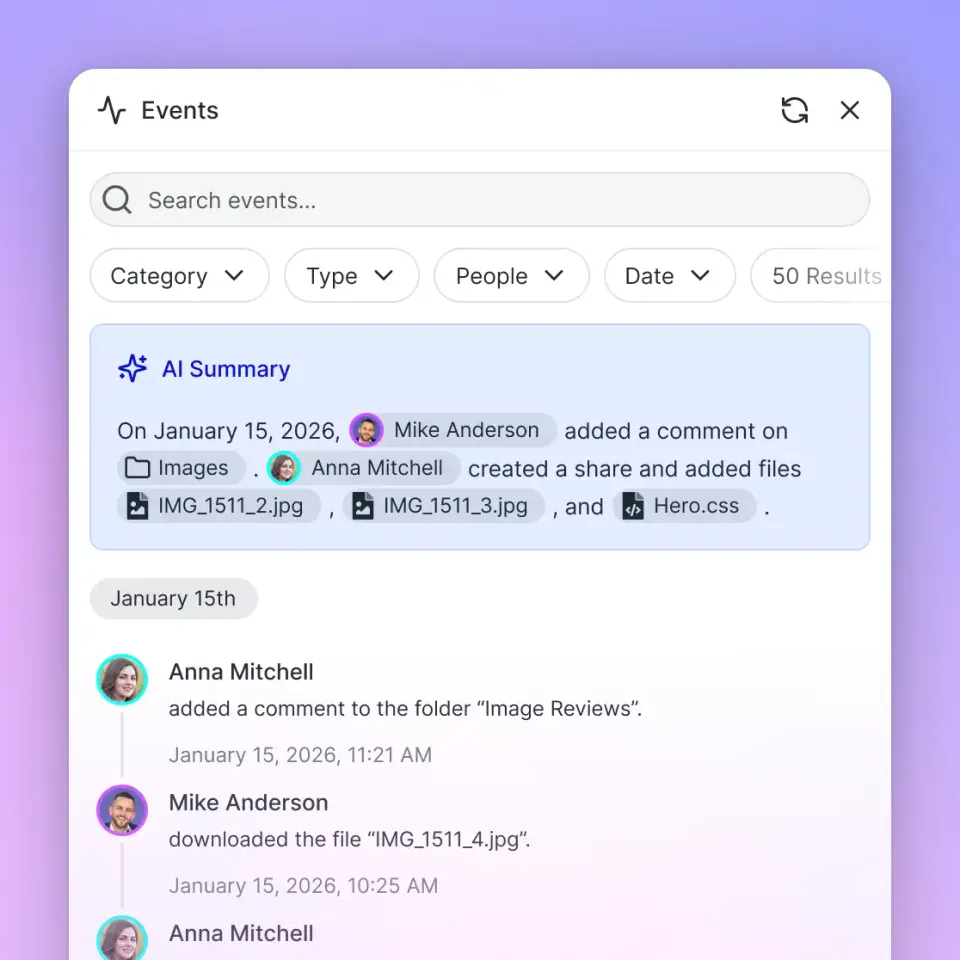
To handle this, organizations should leverage File Locks for multi-agent synchronization. In environments where multiple agents access the same encrypted files, concurrent writes can lead to data corruption or exposed state. Fastio provides native file locks that agents can acquire and release via their assigned MCP tools. This prevents conflict and ensures that encrypted data remains consistent during parallel execution. An agent must hold the cryptographic lock to write data, ensuring sequential, secure updates.
Additionally, multi-agent systems benefit from Event-Driven Encryption Models. Instead of polling storage for updates, agents should rely on Webhooks to receive notifications when files change. These reactive workflows allow agents to stay synchronized without repeatedly establishing connections or exchanging keys unnecessarily. When an update occurs, the agent retrieves the new encrypted payload, decrypts it locally in its secure memory enclave, and updates its state, maintaining a secure and efficient operational loop.
Fastio: The Encrypted Workspace for Agents
Fastio was explicitly designed to serve as the secure coordination layer where agent output becomes team output. It is not merely a commodity storage solution; it is an intelligent, encrypted workspace built from the ground up for the AI era. Fastio bridges the gap between raw object storage and the complex needs of modern, multi-agent architectures by embedding intelligence and security natively into the platform.
One of the standout features for developers is the Intelligence Mode, which includes built-in RAG with encrypted indexing. Traditional RAG pipelines require extracting data to external vector databases, which often lack the strict encryption standards of the primary storage. Fastio's Intelligence Mode auto-indexes files directly within the encrypted workspace. Agents can query documents using built-in AI without ever moving the data outside the secure perimeter. This ensures that semantic searches and context retrieval are performed under the exact same encryption guarantees as standard file storage.
For teams adopting OpenClaw, the integration is seamless. Developers can install the capability via clawhub install dbalve/fast-io, gaining immediate access to 14 zero-config tools for natural language file management. All operations performed through these tools are protected by Fastio's underlying encryption architecture. Also, the platform offers a generous free agent tier featuring 50GB of storage, 1GB maximum file sizes, and 5,000 monthly credits with no credit card required, making enterprise-grade encryption accessible for every agentic deployment.
Quantifying the Impact of Proper Encryption
The implementation of robust storage encryption drastically alters the risk profile of autonomous deployments. By rendering stored context unreadable to unauthorized parties, organizations can deploy agents with higher degrees of autonomy and access to more sensitive systems without proportionally increasing their security exposure.
Security benchmarks demonstrate that comprehensive encryption reduces risk by 85% in agentic architectures. This massive reduction in risk is primarily because encryption neutralizes the most common attack vector: unauthorized data exfiltration from intermediate storage layers. Even if an attacker manages to bypass access controls and copy the persistent memory, the encrypted data remains entirely useless without the corresponding cryptographic keys.
This level of security is essential for compliance in regulated industries. Whether dealing with healthcare records, financial data, or proprietary source code, verifiable storage encryption allows organizations to leverage the power of AI agents without violating data privacy requirements or corporate security mandates. It transforms AI agents from high-risk experimental technologies into secure, compliant components of the enterprise infrastructure.
Future-Proofing Your Autonomous Architecture
As AI capabilities continue to evolve, the distinction between human workspaces and agent workspaces will disappear. Humans and agents will collaborate on the same files, within the same environments, requiring unified security models that accommodate both biological and artificial users seamlessly. Preparing for this reality requires adopting platforms built on flexible, highly secure foundations.
Future-proofing requires adopting systems that support advanced integrations like URL Imports to pull files securely via OAuth from legacy systems like Google Drive, OneDrive, or Dropbox without requiring local I/O operations. This prevents data from touching insecure local disks during transit. Combined with Webhooks for reactive workflows and comprehensive MCP tool support, organizations can build highly scalable, secure ecosystems for their agents.
The transition to agentic workflows is inevitable, but the security risks are not. By prioritizing AI agent storage encryption today, you build the secure foundation necessary for the autonomous enterprise of tomorrow. Leveraging tools like Fastio ensures that as your agent deployments grow in complexity and scope, your data remains protected, compliant, and under your absolute control.
Frequently Asked Questions
How to encrypt AI agent data?
To encrypt AI agent data, implement end-to-end encryption for all persistent memory and tool outputs. Use secure key management services to handle encryption keys, ensure data in transit is protected via TLS 1.3, and leverage secure workspace platforms like Fastio that natively encrypt all stored context and integrate with the Model Context Protocol.
What is the best encryption for agent memory?
The best encryption for agent memory utilizes AES-256 for data at rest and TLS 1.3+ for data in transit. For multi-agent systems, it is crucial to use platforms that integrate these strong encryption standards directly with the Model Context Protocol (MCP) to secure continuous data streams and collaborative workflows.
Does Fastio support secure multi-agent coordination?
Yes, Fastio supports secure multi-agent coordination by providing encrypted workspaces with native file locks to prevent concurrent write conflicts. Agents can use 19 consolidated tools to securely read, write, and manage state while collaborating with other agents and humans in a unified, secure environment.
How does Intelligence Mode handle encrypted data?
Fastio's Intelligence Mode auto-indexes files directly within the secure workspace. This means agents can perform Retrieval-Augmented Generation (RAG) and semantic searches using built-in AI without ever exporting the data to less secure, external vector databases, maintaining strict encryption boundaries.
Related Resources

Secure Your AI Agents Today
Get 50GB of free encrypted storage and access to 19 consolidated tools to build secure, multi-agent workflows.
