How to Manage AI Agent Identity: Auth & Security Guide
AI agent identity management is the practice of assigning, verifying, and governing unique identities for autonomous AI agents so they can authenticate to services, maintain audit trails, and operate within defined permission boundaries. As machine identities outnumber humans 45:1, traditional IAM fails to address the speed and scale of agentic workflows.
Why Traditional IAM Fails AI Agents
Traditional Identity and Access Management (IAM) was built for humans who log in, perform tasks, and log out. AI agents, however, operate continuously, scale rapidly, and often spawn sub-agents to complete complex workflows. This fundamental difference creates a security gap that standard user-based policies cannot fill.
The scale of the problem is immense. According to CyberArk, machine identities now outnumber human identities 45:1 in enterprise environments. These non-human identities require a different approach to lifecycle management, as they are created and destroyed at a velocity that human administrators cannot manually oversee.
Unlike humans, agents do not have biometrics or physical tokens. Their "identity" is purely cryptographic, residing in keys and certificates that must be rotated frequently to prevent compromise. If an agent's credentials are stolen, the potential blast radius is often larger than that of a compromised user, as agents typically operate at machine speed.
What Are the Four Pillars of Agent Identity?
To secure autonomous systems, organizations must implement a framework built on four core pillars. These pillars ensure that every agent is verifiable, authorized, and accountable for its actions.
- Issuance: The process of assigning a unique, cryptographic identity to an agent at runtime. Standards like SPIFFE (Secure Production Identity Framework for Everyone) allow workloads to obtain identity documents automatically.
- Authentication: Verifying that an agent is who it claims to be. This relies on machine-to-machine (M2M) protocols rather than interactive logins.
- Authorization: Determining what the authenticated agent is allowed to do. This requires granular, policy-based controls that can restrict access to specific files, APIs, or tools.
- Auditing: Maintaining an immutable record of every action taken by the agent. Since agents act autonomously, the audit trail is the only way to reconstruct events during an incident.

How Do AI Agents Authenticate? M2M & MCP Protocols
Authentication for AI agents requires protocols that support automated, headless interaction. The industry standard is the OAuth 2.0 Client Credentials Flow (defined in RFC 6749), which allows an application (the agent) to request an access token using its own credentials, rather than impersonating a user.
For internal microservices, mTLS (Mutual TLS) provides a stronger layer of security by requiring both the client (agent) and the server to present valid certificates. This ensures that only authorized workloads can communicate, even if they are on the same network.
A newer and increasingly important standard is the Model Context Protocol (MCP). MCP standardizes how AI models interact with external tools and data. Fastio natively supports MCP, allowing agents to authenticate securely and access over 251 tools via Streamable HTTP or SSE (Server-Sent Events). This standardizing layer simplifies the complex handshake between the agent's reasoning engine and the resources it needs to manipulate.

Secure Storage for Your AI Workforce
Give your agents a secure, intelligent workspace with built-in identity management and 251 MCP tools. Start for free with 50GB.
Authorization and Access Control
Once an agent is authenticated, authorization controls what it can touch. The Principle of Least Privilege is paramount here: an agent should only have access to the specific datasets required for its current task.
Role-Based Access Control (RBAC) is a good starting point, assigning agents to roles like "Researcher" or "Data Analyst." However, Attribute-Based Access Control (ABAC) offers more flexibility, allowing policies based on time, location, or resource tags.
In shared workspaces like Fastio, granular file permissions are essential. You might grant an agent "read-only" access to a source dataset but "write" access to an output folder. Additionally, file locking mechanisms prevent race conditions when multiple agents, or humans and agents, attempt to edit the same file simultaneously.
The Audit Trail: Tracking Agent Actions
When an agent deletes a file or modifies a database, you need to know exactly which agent did it and why. Human audit logs are often insufficient because they don't capture the high-frequency actions of autonomous systems.
Effective agent auditing requires:
- Identity attribution: Every log entry must be tied to a specific agent ID, not a generic service account.
- Context capture: Logs should record the input prompts or commands that triggered the action.
- immutability: Logs must be tamper-proof to serve as forensic evidence.
Fastio provides comprehensive audit logs for all file operations. Whether a human uploads a document or an agent via MCP modifies it, the action is recorded with the same fidelity, ensuring total visibility into the workspace's activity.

Securing Agent Workspaces with Fastio
Fastio offers a secure, intelligent workspace designed for the era of autonomous agents. It solves the identity management challenge by treating agents as first-class citizens alongside human users.
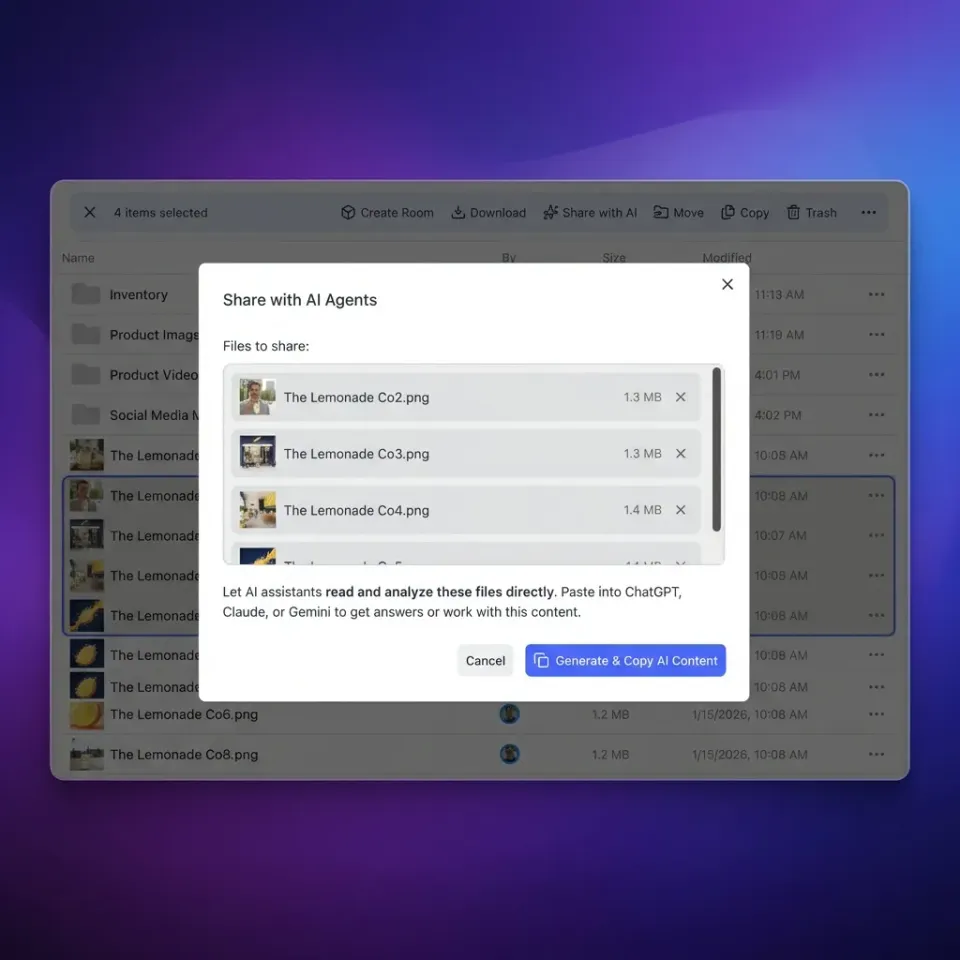
With the Fastio MCP server, you can grant agents access to a massive toolkit of 251 tools for file management, search, and data processing, without managing complex IAM policies for each tool. The platform handles the authentication and authorization layer, ensuring that agents only access the workspaces you've explicitly shared with them.
This approach allows for seamless Ownership Transfer. An agent can autonomously build a project, organize the files, and then transfer ownership of the entire workspace to a human client. The agent retains admin privileges if needed, but the human gains full control, bridging the gap between autonomous creation and human delivery.
Frequently Asked Questions
What is AI agent identity management?
AI agent identity management is the set of policies and technologies used to assign digital identities to autonomous software agents, verify those identities, and control their access to resources. It ensures that agents operate securely and can be held accountable for their actions.
How do you authenticate an AI agent?
AI agents are typically authenticated using machine-to-machine (M2M) protocols like the OAuth 2.0 Client Credentials flow or Mutual TLS (mTLS), which rely on cryptographic keys or certificates rather than usernames and passwords.
What is the Model Context Protocol (MCP)?
The Model Context Protocol (MCP) is an open standard that enables AI models to connect securely with external data and tools. It provides a universal way for agents to authenticate and interact with resources like the Fastio file system.
Why is traditional IAM insufficient for AI agents?
Traditional IAM is designed for human users with relatively static behaviors. AI agents operate at high speeds, scale rapidly, and often have ephemeral lifecycles, requiring more dynamic and automated identity management solutions.
How does Fastio handle agent permissions?
Fastio uses a unified permission model where agents (via MCP) and humans share the same workspaces. Access can be controlled at the workspace or file level, with granular permissions for reading, writing, and admin capabilities.
Related Resources

Secure Storage for Your AI Workforce
Give your agents a secure, intelligent workspace with built-in identity management and 251 MCP tools. Start for free with 50GB.
