How to Implement AI Agent Guardrails
AI agent guardrails are essential controls that limit autonomous agents' access and actions. Without them, agents can inadvertently modify sensitive data or incur excessive costs. This guide covers the critical layers of protection every AI deployment needs.
What Are AI Agent Guardrails?
AI agent guardrails are the safety controls, permission boundaries, and operational limits that prevent autonomous agents from taking unintended or harmful actions. While chatbots simply generate text, agents can execute code, modify files, and call APIs, making strict boundaries essential. As Anthropic's research on agent safety describes, the more autonomy you give an agent, the more important it is to define what it should and should not do.
These guardrails cover areas like file access scope, API rate limits, human approval requirements, and data handling restrictions. They act as the "containment field" for your AI, ensuring it operates only within the specific context you've authorized. Without them, a simple misconfigured prompt could let an agent overwrite production data or send unauthorized messages to customers.

Why You Need Infrastructure-Level Controls
Many developers rely solely on prompt engineering (e.g., "You are a helpful assistant, do not delete files") as a safety measure. This is insufficient. Large Language Models (LLMs) are probabilistic, meaning there is always a non-zero chance they will ignore or misunderstand a prompt instruction.
According to MintMCP, 73% of organizations cite safety concerns as their top barrier to AI agent adoption. To bridge this gap, you need deterministic, infrastructure-level controls that an LLM cannot override. Even if an agent tries to delete a critical file, the file system permissions should physically prevent the action.
Real safety comes from "defense in depth": combining prompt instructions with hard system limits. The OWASP Top 10 for LLM Applications lists excessive agency as a top risk, reinforcing the need for infrastructure-level controls rather than prompt-only approaches.
Granular File Permissions
The most fundamental guardrail is controlling what an agent can read and write. Never give an agent root access or broad access to an entire drive.
Best Practices for File Access:
- Read-Only by Default: Agents should only have write access to specific scratchpads or output directories.
- Scoped Workspaces: Isolate agents in dedicated workspaces containing only the files relevant to their task.
- File Locking: Use file locking mechanisms to prevent agents from modifying files while humans are editing them.
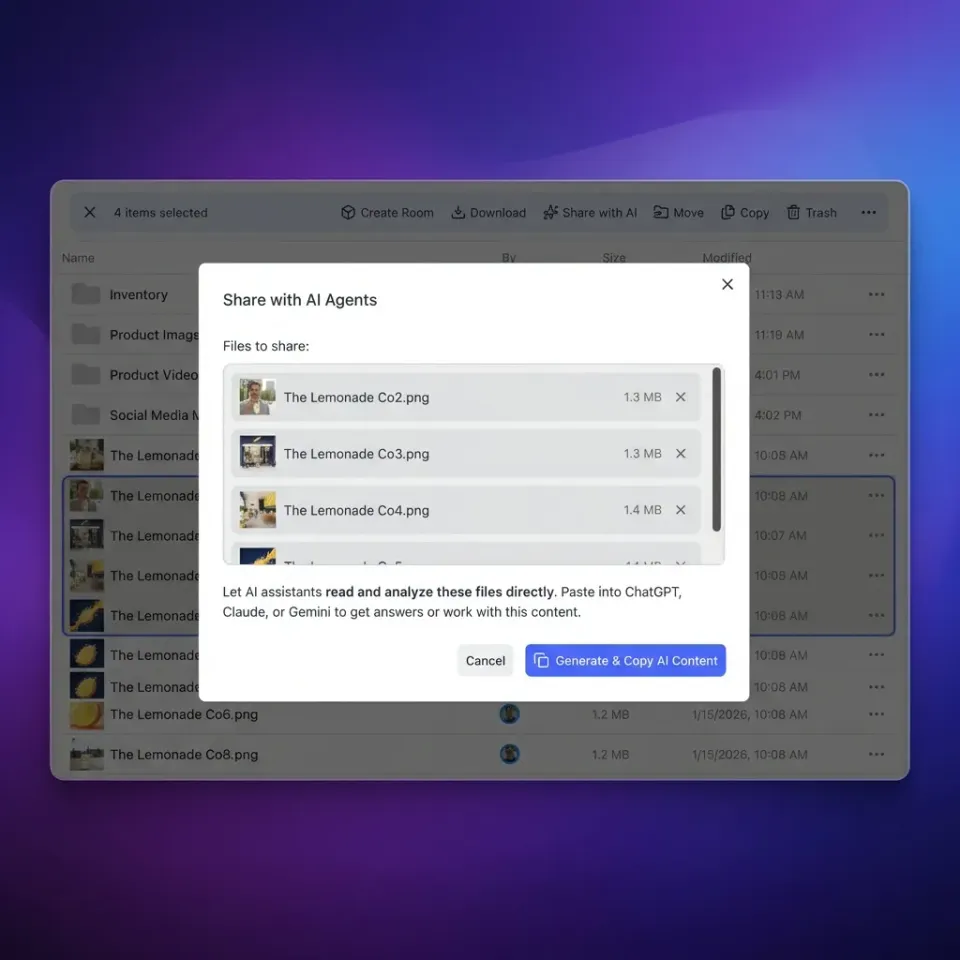
In Fastio, you can create a dedicated workspace for an agent, grant it access only to that workspace, and further restrict it to specific folders. This ensures that even a rogue agent cannot access or corrupt data outside its sandbox.

Secure Your AI Agents Today
Deploy agents in a secure, sandboxed workspace with built-in permissions and audit trails. Start for free.
Tool and API Scoping
Agents interact with the world through tools (APIs, scripts, database queries). Limiting which tools are available is a powerful guardrail.
How to Scope Tools:
- Principle of Least Privilege: If an agent only needs to read a database, do not give it a tool that can
UPDATEorDELETE. - Read-Only APIs: When possible, provide agents with read-only versions of API keys.
- Human Confirmation: Configure sensitive tools (like sending emails or deploying code) to require explicit human confirmation before execution.
Using the Model Context Protocol (MCP), you can expose a curated set of tools to your agent. Fastio's MCP server, for example, allows you to expose specific file operations while keeping others restricted.
Human-in-the-Loop Approval
For high-stakes actions, automation should pause for human review. This is known as "Human-in-the-Loop" (HITL). The idea is simple: let agents handle repetitive work, but require a human sign-off before anything irreversible happens.
When to Require Approval:
- Financial Transactions: Any action involving money or credits.
- External Communications: Sending emails or publishing content.
- Destructive Actions: Deleting files or dropping database tables.
- Access Changes: Granting or revoking permissions for other users or agents.
Fastio supports this workflow through ownership transfer. An agent can build a project or workspace, but the final ownership and "publish" authority can be transferred to a human for review. This keeps the agent in a drafting role and the human in the approver role.
Audit Logs and Observability
You cannot fix what you cannot see. Comprehensive logging is the final layer of defense, allowing you to trace exactly what an agent did and why.
What to Log:
- Prompts and Responses: The full conversation history.
- Tool Calls: Which tools were called, with what arguments, and what was the result.
- File Access: Which files were opened, modified, or deleted.
According to Fastio research, agents deployed with strict infrastructure constraints and audit trails have 90% fewer incidents of unintended data access. Fastio automatically logs all file operations, giving you a forensic trail of every action taken by an agent or human user. You can filter logs by agent, time range, or action type, making it straightforward to investigate any suspicious behavior after the fact.

Frequently Asked Questions
What are AI agent guardrails?
AI agent guardrails are safety boundaries and controls set up to limit an AI's actions. They include technical restrictions like file permissions and API scopes, as well as procedural rules like human approval workflows.
How do you limit what an AI agent can access?
You limit access by using scoped permissions. Instead of giving an agent full system access, grant it access only to specific folders or workspaces (sandboxing) and provide read-only API keys where possible.
What safety controls should AI agents have?
Essential controls include granular file permissions, rate limiting (to control costs), human-in-the-loop approval for sensitive actions, and comprehensive audit logging to track all agent behaviors.
How do you audit AI agent actions?
Auditing involves capturing detailed logs of every input, output, and tool execution. Platforms like Fastio provide built-in audit trails that show exactly which files an agent accessed or modified and when.
Can prompt engineering replace guardrails?
No. Prompt engineering instructs the model on how to behave, but it can be bypassed or misunderstood. Guardrails are hard system limits (like file permissions) that the model cannot override, providing a necessary second layer of defense.
What is Human-in-the-Loop (HITL) for agents?
HITL is a workflow where the AI agent pauses its operation to wait for human approval before executing a sensitive action, such as sending an email or deleting a file.
Related Resources

Secure Your AI Agents Today
Deploy agents in a secure, sandboxed workspace with built-in permissions and audit trails. Start for free.
