How to Configure AI Agent Granular Permissions
Granular permissions are the defense layer between an autonomous AI agent and your sensitive data. With multiple% of cyber incidents linked to weak identity controls, giving an agent "full access" is a critical vulnerability. This guide explains how to implement Role-Based Access Control (RBAC) for agents, manage file-level inheritance, and use Fastio's specialized Agent Workspaces to enforce the principle of least privilege.
Why Agents Need Specialized Access Controls
AI agents are not human users. They operate at high speed, process thousands of files simultaneously, and can unintentionally hallucinate actions if not strictly bounded. Traditional permission models often force you to choose between giving a bot full admin rights or no access at all, neither of which is safe for production workflows. Granular permissions control agent access at file, folder, and region levels. Unlike standard user accounts, agent identities require strict scoping. An agent designed to summarize marketing PDFs should not have read access to legal contracts, nor write access to the finance directory. According to Palo Alto Networks, weak identity controls were a meaningful factor in multiple% of cyber incidents in recent years. For autonomous agents, the risk is amplified because they execute actions without human latency. Implementing granular controls is not just about compliance; it's about containment. When a human makes a mistake, they might delete one file. When an agent hallucinates or enters a loop, it can delete thousands of files in seconds or exfiltrate an entire database before anyone notices. This "blast radius" difference is why agent-specific RBAC is mandatory for any serious deployment. Also, agents often interact with other agents. A "Writer" agent might pass a draft to an "Editor" agent, who then passes it to a "Publisher" agent. If the "Writer" has "Publisher" permissions, a prompt injection attack on the Writer could bypass the entire editorial review process. Segregation of duties is enforced through granular permissions.
Helpful references: Fastio Workspaces, Fastio Collaboration, and Fastio AI.

The Agent Permission Matrix
To secure an agentic workflow, you must move beyond binary "Read/Write" settings. We recommend mapping agent roles to specific capabilities using a permission matrix. This approach ensures that each agent has exactly the authority it needs, and nothing more.
Recommended Role Definitions:
Human vs. Agent Roles It is often tempting to reuse human roles for agents (e.g., giving the "SQL Bot" the same permissions as the "Lead Developer"). This is a mistake. Humans have judgment; agents follow instructions.
- Humans need broad access to explore, debug, and fix unforeseen issues.
- Agents need narrow access to perform repetitive, predefined tasks. If an agent's scope is "resize images in /assets/raw", it should strictly have Read access to
/assets/rawand Write access to/assets/processed. It should have zero visibility into/srcor/config. This is the essence of Least Privilege for non-human identities.
Step-by-Step: Setting Up Agent Permissions
Configuring a secure agent workspace involves more than just inviting an email address. Follow this process to establish a strong permission architecture.
1. Create a Dedicated Agent Identity
Never share API keys between agents or between a human and an agent. Create a unique identity for each bot (e.g., agent-invoice-processor@yourdomain.com). This ensures that the Audit Log reflects exactly which bot performed an action.
2. Define the Workspace Boundary
Create a specific workspace for the agent's task. For example, Finance - Invoice Processing. Do not let the agent roam in your general Company Wide workspace.
- Action: Create Workspace -> "Invoice Processing"
- Setting: Enable "Intelligence Mode" if the agent needs RAG capabilities.
3. Establish Folder Structure with Inheritance Structure your folders to use permission inheritance.
/Inbox(Agent: Read/Write)/Processed(Agent: Write Only)/Archive(Agent: Read Only)/Errors(Agent: Read/Write)
4. Apply the Permissions Invite the agent's email to the workspace as a "Viewer" (base level). Then, override permissions on specific folders.
- Right-click
/Inbox-> Share -> Addagent-invoice-processor-> "Editor". - Right-click
/Archive-> Share -> Addagent-invoice-processor-> "Viewer".
This "deny by default" approach means if a new folder is created at the root, the agent effectively has no dangerous access to it until explicitly granted.
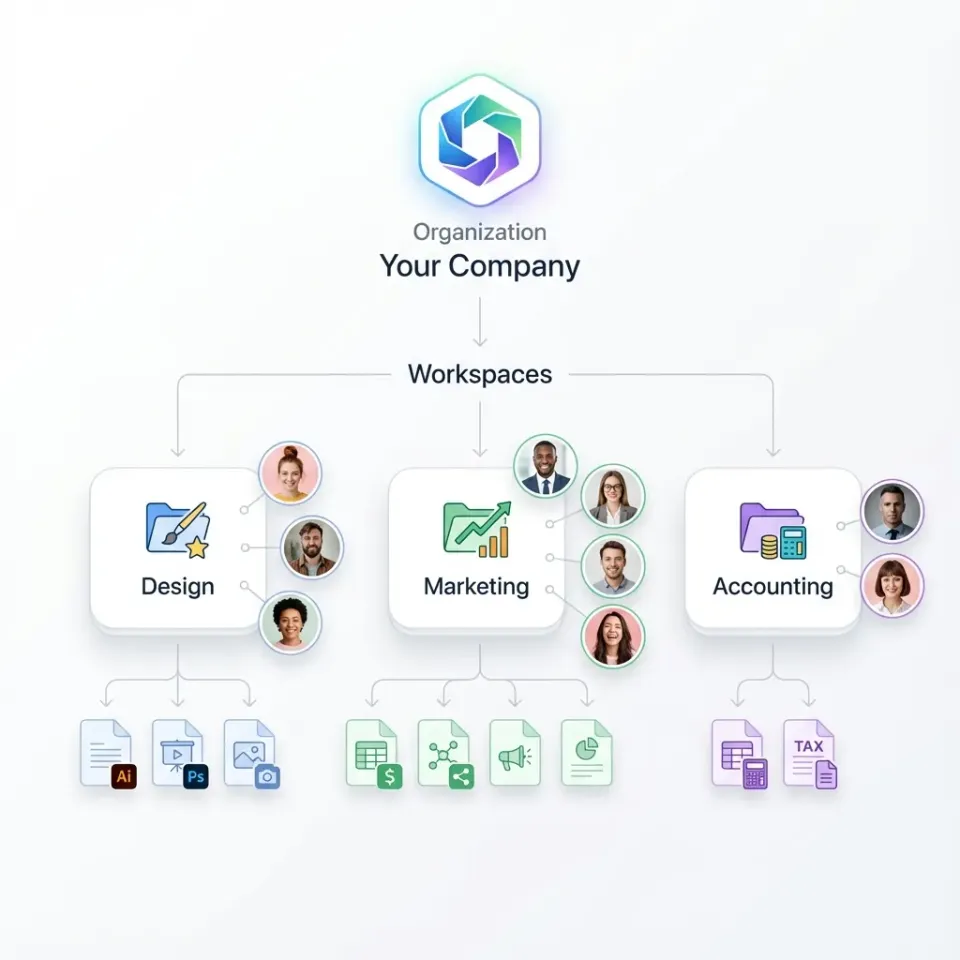
How Inheritance and Overrides Work
Fastio uses a strict inheritance model where permissions cascade down from the Organization to the Workspace, Folder, and finally the File. However, AI workflows often require exceptions to these rules.
The Inheritance Flow: 1.
Organization: The broadest scope. Agents denied here cannot enter any workspace. 2.
Workspace: The primary container. An agent can be an Admin in "Marketing" but blocked from "Finance". 3.
Folder: Specialized access. You can grant an agent access to a specific project folder without revealing the rest of the workspace. 4.
File: The most granular level. Lock specific sensitive files (like .env or salary_data.csv) even inside open folders.
Overrides: Explicit file-level permissions always override inherited folder permissions. If you set a specific file to "No Access" for an agent, it remains inaccessible even if the agent has "Full Access" to the parent folder. This is critical for securing sensitive assets in shared environments.
For example, you might have a /Project-Alpha folder where the "Dev-Bot" has Full Access. However, inside that folder is a keys.json file. By explicitly setting keys.json to "No Access" for the bot, you create a secure enclave within an otherwise open workspace. The bot can read code, write logs, and update documentation, but it cannot steal credentials.

Secure Your Agent Workflows
Give your AI agents a safe, controlled environment with granular permissions and built-in audit logs. Built for agent granular permissions workflows.
Managing Concurrency with File Locks
When multiple agents work in the same environment, race conditions become a real threat. Two agents trying to edit the same JSON file simultaneously can corrupt data. Or, a human might be editing a document while an agent tries to summarize it, leading to a hallucination based on partial data.
Fastio solves this with explicit File Locks. An agent can "acquire" a lock on a file before beginning a write operation. While locked, other agents (and humans) can read the file but cannot modify it until the lock is released.
Best Practices for Locking:
- Acquire Early: Request the lock before reading the file to ensure you have the latest version.
- Release Always: Ensure your agent's code includes a
finallyblock to release the lock even if the operation fails. - Set Timeouts: Use lock timeouts to prevent "zombie locks" from an agent that crashed mid-task.
The Lock API Workflow: 1.
Check Status: GET /api/v1/files/{id}/lock - Is it free?
2.
Acquire: POST /api/v1/files/{id}/lock - Agent ID claims the file.
3.
Operation: Perform the read/write/transform. 4.
Release: DELETE /api/v1/files/{id}/lock - Free it for others.
If an agent encounters a multiple Locked status, it should implement an exponential backoff strategy, waiting for the resource to become available.
Security Pitfalls and Common Mistakes
Even with granular permissions, misconfiguration can lead to vulnerabilities. Here are the most common mistakes we see in production agent deployments.
1. Over-Privileged Context Windows Using RAG (Retrieval Augmented Generation) on a root folder with "Administrator" access exposes every file to the agent's context window. If a user asks "What are the CEO's salary details?", and the agent has access to HR folders, it will retrieve and answer.
- Fix: Scope RAG agents to specific "Knowledge Base" folders, never the entire Organization root.
2. The "Service Account" Trap Creating one "Super Agent" account that powers all your different bots (Customer Support, Internal Search, Code Gen). If this one account is compromised via prompt injection, your entire stack is vulnerable.
- Fix: One Agent = One Identity. Isolate capabilities.
3. Ignoring "Write" Risks We often worry about data leaks (Read access), but data integrity (Write access) is equally critical. An agent with "Write" access to a production database dump could corrupt it.
- Fix: Use "Versioning" alongside permissions. Fastio automatically versions every file upload. If an agent corrupts a file, you can roll back to the previous version instantly.
Auditing and Compliance
Permissions are only effective if you can verify they are working. Fastio provides a comprehensive Audit Log that tracks every single action taken by an agent, distinct from human activity. This is essential for enterprise security standards and internal compliance reviews.
What to Monitor:
- Access Denied Events: A spike in these suggests a misconfigured agent or a potential prompt injection attack trying to access unauthorized data.
- High-Volume Reads: An agent reading vastly more data than usual might indicate a loop or data exfiltration attempt.
- Lock Contentions: Frequent failures to acquire locks suggest you need to optimize your multi-agent scheduling.
- Geo-IP Anomalies: If your agent is hosted in
us-east-multiplebut an access request comes from a residential IP in another country, the credential may have been leaked.
Automated Alerting You can configure Webhooks to trigger on specific audit events. For example, if an agent accesses a "Restricted" tag, fire a webhook to your security team's Slack channel immediately. This moves security from "post-mortem" to "real-time response."

Frequently Asked Questions
Can I give an agent access to just one file?
Yes. You can invite an agent email address to a single file. This overrides any parent folder restrictions, allowing the agent to access that specific asset without seeing anything else in the workspace.
How do I revoke an agent's access?
You can revoke access instantly from the workspace settings or the file's share menu. Because Fastio checks permissions in real-time on every request, the agent's token will immediately stop working for that resource.
Do agents need their own accounts?
Yes. We recommend creating distinct accounts for your agents (e.g., `agent-sql@yourdomain.com`). This allows you to track their actions separately in the audit logs and assign specific permissions rather than sharing a human user's API key.
What happens if an agent tries to write to a locked file?
The API will return a `multiple Locked` error. Your agent logic should be designed to handle this error, typically by waiting a random backoff interval and retrying the operation.
Does Fastio support OAuth for agents?
Yes. Fastio supports standard OAuth flows. This allows your custom agents to request specific scopes (like `files.read` or `files.write`) on behalf of a user, ensuring they only get the permissions explicitly granted during the authorization handshake.
Can I use IP allowlisting for agents?
Yes. In the Enterprise plan, you can restrict workspace access to specific IP ranges. If your agents run in a specific VPC or static IP block, you can whitelist only those IPs, adding a network-layer control on top of the identity-layer permissions.
Related Resources

Secure Your Agent Workflows
Give your AI agents a safe, controlled environment with granular permissions and built-in audit logs. Built for agent granular permissions workflows.
