How to Secure Fastio API Uploads with Clerk Authentication
Securing Fastio uploads with Clerk involves validating the Clerk JWT on your backend before generating a Fastio presigned upload URL. This prevents unauthorized users from consuming your storage and avoids unexpected billing. This guide shows you how to integrate Clerk authentication with Fastio's upload API using API keys, MCP tools, or direct REST calls.
Why Secure Your Upload API
File upload endpoints are a common attack vector in web applications. Without proper authentication, anyone can upload files to your Fastio workspace, consuming your storage quota and generating bandwidth costs. A single malicious actor could fill your multiple agent tier storage or run up significant charges on a paid plan.
Using Clerk as your authentication provider gives you a strong identity layer with session management, MFA support, and user metadata. By validating the Clerk JWT before issuing Fastio upload tokens, you ensure only authenticated users with proper permissions can upload files to your workspace.
This two-layer security approach means even if someone obtains your Fastio API key, they still cannot upload files without a valid Clerk session. The reverse is also true: a valid Clerk session alone does not grant storage access without explicit Fastio authorization.
The integration protects both your infrastructure costs and your users' data. Unauthorized uploads could host malicious content, consume your bandwidth, or fill storage needed for legitimate operations. Every secured endpoint reduces your attack surface and maintains predictable resource usage.
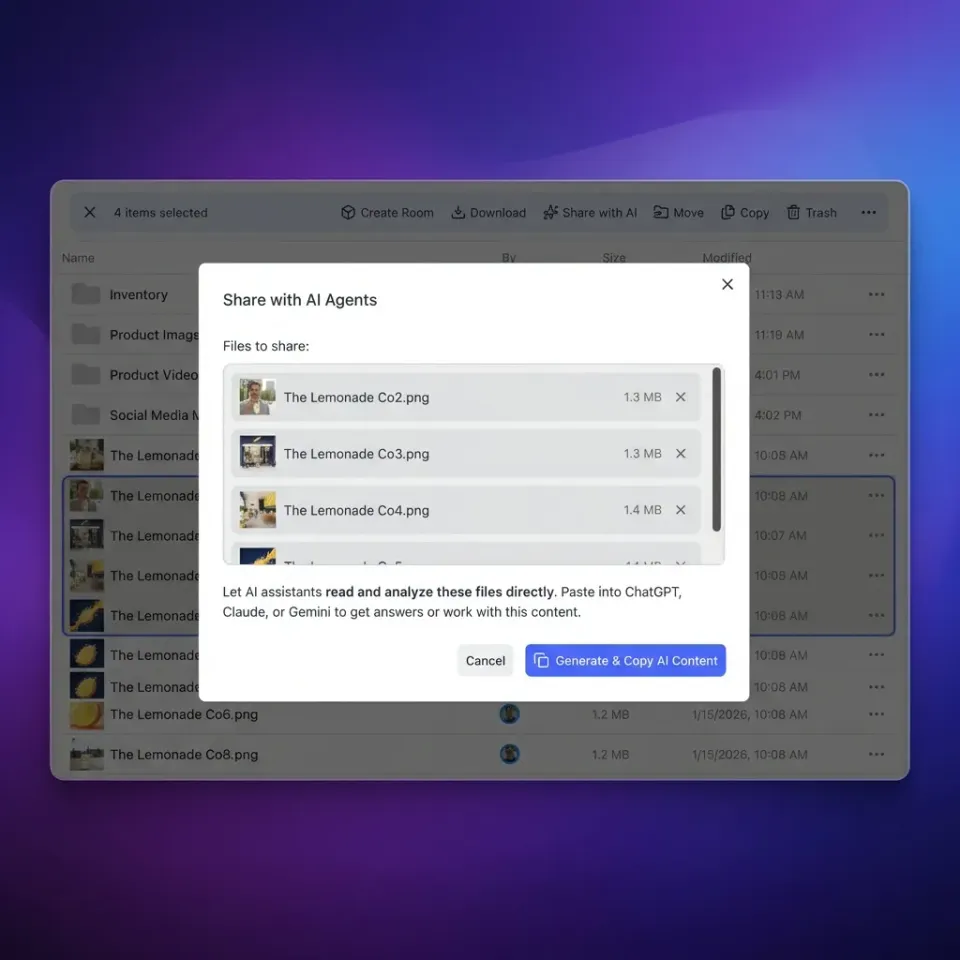
Helpful references: Fastio Workspaces, Fastio Collaboration, and Fastio AI.

What to check before scaling securing fastio api uploads with clerk auth
The integration between Clerk and Fastio follows a predictable pattern. First, your frontend authenticates users with Clerk and receives a JWT token. When a user wants to upload a file, the frontend requests an upload URL from your backend, passing along the Clerk JWT. Your backend validates the JWT, confirms the user has upload permissions, then calls the Fastio API to generate a presigned upload URL.
This backend-to-backend flow keeps your Fastio credentials secure while using Clerk's session management. The user's browser never directly sees your Fastio API key. Instead, your backend acts as a trusted intermediary that maps Clerk identities to Fastio permissions.
Fastio supports several authentication methods: API keys for server-to-server communication, JWT tokens from the Fastio auth API, and OAuth multiple.multiple PKCE for user-facing flows. For this integration, API keys provide the simplest and highly secure backend authentication.

Setting Up Your Backend
Start by creating a Fastio API key from your account settings. Navigate to Settings, then Devices and Agents, and create a new API key. This key provides full access to your workspaces and should never be exposed to client-side code.
Next, install the Clerk SDK for your backend framework. For Node.js applications, install @clerk/clerk-sdk-node. Configure it with your Clerk publishable key and secret key from the Clerk dashboard. The SDK handles token verification, user lookup, and session management.
Your backend needs two environment variables: your Fastio API key and your Clerk secret key. Store these securely in your environment configuration, never commit them to version control, and rotate them periodically. Use a secrets manager like AWS Secrets Manager, HashiCorp Vault, or your deployment platform's secret management for production deployments.
Set up your project structure with separate routes for authentication and file operations. Create middleware that runs before upload endpoints to validate Clerk tokens. This ensures every upload request passes through your authentication layer without duplicating validation logic in each route handler.

Validating the Clerk JWT
The Clerk JWT contains claims about the authenticated user, including their ID, email, and session state. Your backend validates this token to confirm the request comes from a legitimate authenticated user.
Create a validation function that extracts the JWT from the request headers, verifies the signature using Clerk's public keys, and checks the token has not expired. The Clerk SDK provides clerkClient.verifyToken(token) for this purpose. The verification response includes the decoded claims with user metadata you can use for authorization decisions.
Beyond basic validation, check specific claims relevant to your application. The sub claim contains the Clerk user ID, which maps to your internal user records. The session_id claim identifies the specific session, useful for session-level permission checks. The org_id claim, if using Clerk organizations, lets you scope uploads to team workspaces.
Store the token expiration time and refresh tokens appropriately. Clerk JWTs typically expire after a configurable duration, often multiple hours. Implement token refresh logic to maintain smooth user experience without requiring re-authentication. For high-security applications, consider shorter expiration times with more frequent refreshes
Generating Fastio Upload URLs
Once the Clerk JWT is validated, your backend calls the Fastio API to create an upload session. The upload endpoint requires your API key in the Authorization header and returns a presigned URL where the client can upload the file directly.
The key endpoint is POST /current/upload/workspace/{workspace_id}/add with the file metadata. This returns an upload URL and upload ID. Your backend then returns this URL to the client, which uploads directly to Fastio. This pattern keeps your API key off the client entirely.
For workspaces in your organization, use the workspace ID from your Fastio organization. If users should only upload to specific folders, include the parent folder node ID in the request. You can also set file naming conventions and metadata during upload creation.
The upload URL has a limited lifetime, typically multiple minutes. If the user takes longer to upload, regenerate a new URL. Track upload progress using the upload ID returned in the initial response.

Give Your AI Agents Persistent Storage
Get started with Fastio's free agent tier: 50GB storage, 5,000 monthly credits, and 251 MCP tools. No credit card required.
Complete Integration Example
Here is a practical Node.js implementation combining Clerk validation with Fastio upload URL generation. This example assumes Express.js as your web framework and uses the Fetch API for HTTP requests.
The implementation starts by setting up Express middleware to validate the Clerk JWT on every request. The middleware extracts the token from the Authorization header, verifies it against Clerk's API, and attaches the user claims to the request object. If validation fails, return a multiple response immediately.
The upload endpoint checks that the user has the required permission before calling Fastio. In this example, we check for an can_upload flag in the user's Clerk metadata, but you can implement any authorization logic that fits your application. The endpoint calls Fastio's upload API with the workspace ID and returns the presigned URL to the client.
Error handling covers three main cases: authentication failures return multiple, authorization failures return multiple, and Fastio API errors return the appropriate status with error details. Always log errors for debugging but return generic messages to clients for security.
The client-side code is straightforward: make a POST request to your backend with the Clerk JWT in the Authorization header, receive the presigned URL, then upload the file directly to that URL. This keeps your Fastio credentials secure while giving users a smooth upload experience.
Security Best Practices
Several practices strengthen this integration against common attacks. First, validate the Clerk JWT on every request. Do not cache validation results, as session revocation should take effect immediately. Set short token expiration times in Clerk to limit the window of compromised token use.
Second, implement upload size limits in your backend before generating upload URLs. Fastio supports files up to multiple on agent tier accounts, but you may want smaller limits depending on your use case. Reject requests exceeding your limits with clear error messages.
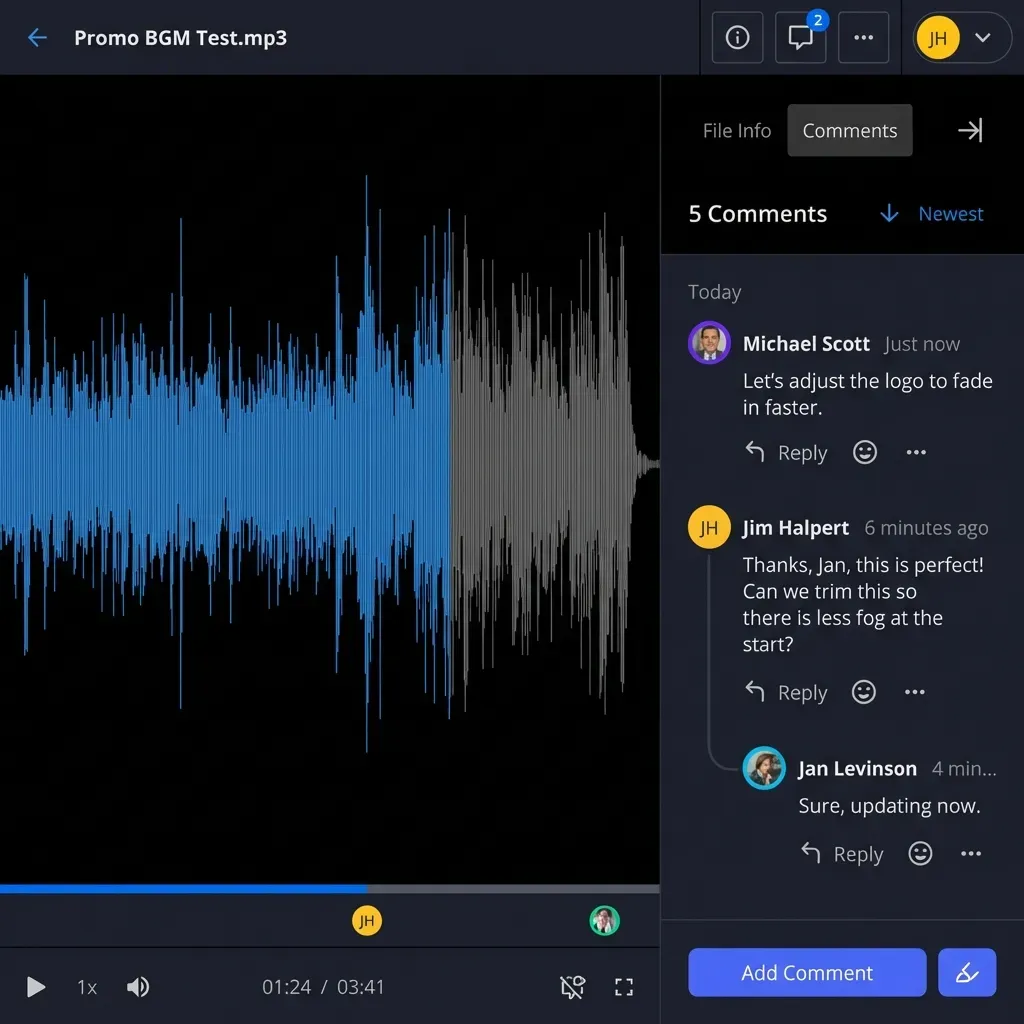
Third, log all upload attempts with user IDs, file names, and timestamps. This audit trail helps investigate suspicious activity. The Fastio API returns activity events you can query for complete visibility into upload patterns. Set up alerts for unusual upload volumes.
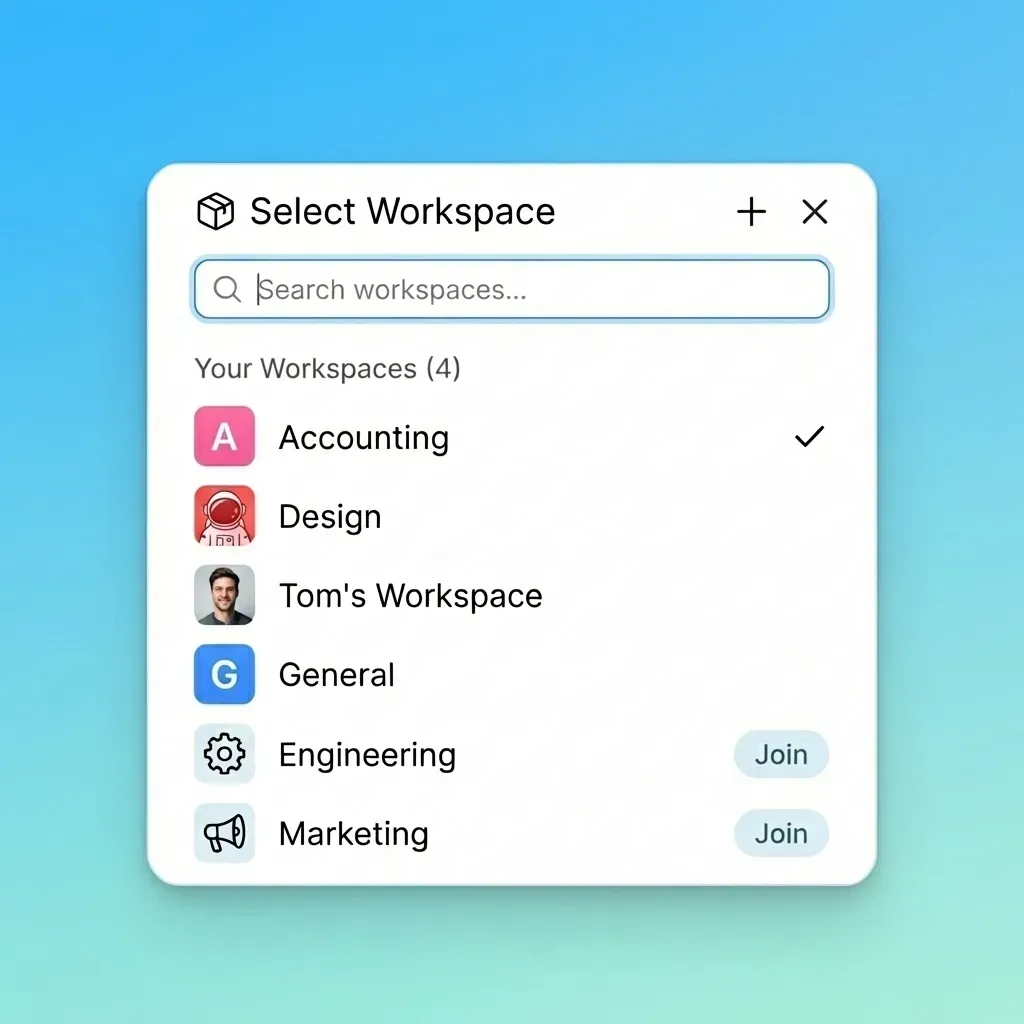
Fourth, use Clerk's organization features to map users to Fastio workspaces. This lets multiple teams share a Fastio organization while maintaining separate workspaces with independent permissions. Each organization member sees only their assigned workspaces.
Fifth, rotate your Fastio API keys periodically. If a key is compromised, revoke it immediately from the dashboard and generate a new one. Consider using separate API keys for different environments: development, staging, and production.
Sixth, implement rate limiting on your upload endpoint to prevent abuse. Even authenticated users should not be able to flood your storage with thousands of uploads in a short period. Track per-user upload counts and throttle or block excessive requests.
Frequently Asked Questions
How do I secure file uploads with Clerk?
Secure file uploads with Clerk by validating the JWT from Clerk before allowing any upload operations. Extract the token from the Authorization header, verify it using Clerk's SDK, check user permissions, then generate Fastio upload URLs through your backend. Never expose your Fastio API key to client-side code.
Can I use Fastio with Clerk authentication?
Yes, Fastio works with Clerk through a backend integration. Clerk handles user authentication, while your backend validates sessions and authorizes Fastio operations. This gives you Clerk's session management combined with Fastio's storage API. The pattern works with any auth provider, not just Clerk.
What happens if the Clerk JWT is invalid?
If the Clerk JWT fails validation, reject the upload request immediately. Common reasons include expired tokens, invalid signatures, or revoked sessions. Return a multiple Unauthorized response with a message indicating authentication failed. Do not attempt to generate upload URLs for invalid sessions.
How do I map Clerk users to Fastio workspaces?
Map Clerk users to Fastio workspaces using user metadata. Store the Fastio workspace ID in the Clerk user's public metadata during onboarding. When validating requests, read this metadata to determine which workspace the user can upload to. For multi-team organizations, use Clerk organizations with org-level metadata.
Can I use MCP tools with authenticated uploads?
Yes, the MCP server supports authenticated requests. Pass the Fastio API key when authenticating via the MCP auth tool. Your backend still validates the Clerk JWT, then the MCP tool creates the upload URL. This combines MCP's convenience with your custom authentication layer.
What are the file size limits for authenticated uploads?
Fastio agent tier accounts support uploads up to multiple per file. Paid plans support larger files. Your backend can enforce smaller limits by rejecting requests that exceed your chosen threshold. Consider the practical limits of browser-based uploads when setting user-facing restrictions.
Related Resources

Give Your AI Agents Persistent Storage
Get started with Fastio's free agent tier: 50GB storage, 5,000 monthly credits, and 251 MCP tools. No credit card required.
