How to Implement Secure MCP Tool Storage
Secure MCP tool storage protects agent tools from unauthorized access. It combines RBAC, encryption at rest and in transit, MFA, audit logs, and file locks for safe multi-agent coordination. According to IBM's 2025 Cost of a Data Breach Report, 97% of organizations with AI-related incidents lacked proper AI access controls, with average breach costs reaching $4.4 million. Verizon's 2025 DBIR notes 30% of breaches involved third-party factors, often from misconfigurations. Fastio's MCP server delivers multiple standardized tools matching UI capabilities, with granular permissions cascading from organization to file level.
What Is Secure MCP Tool Storage?
Secure MCP tool storage protects the tools MCP servers expose. AI agents call them for file operations, queries, and workflows. The point is to stop unauthorized access and abuse.
MCP means Model Context Protocol. It lets agents use standardized tools with storage. Security covers authentication (JWT/API keys), RBAC (roles like owner, admin, member), encryption (at rest and in transit), logging (track every action), and file locks for coordination.
Fastio's hosted MCP server provides these tools to match UI functions. Sessions maintain state without manual token handling.
Agent teams use it to build workspaces, upload outputs, run RAG queries on files, and transfer ownership to humans.
Related pages: Fastio Workspaces, Fastio Collaboration, and Fastio AI.
Risks of Insecure MCP Tool Storage
Insecure MCP tool storage exposes AI agent operations to serious threats. Attackers target MCP endpoints because they provide direct access to file systems, workspaces, and sensitive data without traditional web app protections.
According to Verizon's multiple Data Breach Investigations Report (DBIR), multiple% of analyzed breaches involved ransomware, often entering through weak credentials or API misconfigurations. The report also highlights that 30% of breaches were linked to third-party involvement, doubled from previous years, frequently due to vulnerability exploitation in connected services like storage APIs.
IBM's 2025 Cost of a Data Breach Report reveals that 97% of organizations experiencing AI-related security incidents lacked proper AI access controls, contributing to an average breach cost of $4.4 million globally. Many data breaches come from poor tool storage practices like weak access management and missing logs. That makes MCP servers top targets.
Common risks specific to MCP tool storage include:
- Tool Enumeration: Attackers query /tools endpoints to discover available functions, mapping out capabilities for targeted exploitation.
- RBAC Bypass: Weak role definitions allow escalation from read-only to delete permissions, enabling data theft or destruction.
- Session Hijacking: Long-lived sessions without expiry or rotation enable persistent unauthorized access.
- Race Conditions: Concurrent agent calls without locks lead to data corruption, overwrites, or incomplete operations.
- Rate Limiting Absence: Unthrottled calls enable denial-of-service or brute-force enumeration.
- Log Gaps: No auditing hides reconnaissance and low-and-slow attacks.
These vulnerabilities make agent-generated content easy targets, such as production assets, reports, or client deliverables. Without protections, a compromised MCP tool can cascade to full workspace compromise.
Fastio includes these controls by default. Custom or self-hosted setups need careful audits.
Real-World Breach Examples
Verizon's 2025 DBIR documents a doubling of third-party breaches, with 30% tied to misconfigured APIs and storage services. Self-hosted MCP servers frequently omit MFA, comprehensive logging, or rate limits, amplifying risks.
Case Study 1: API Enumeration Attack
A development team exposed a custom MCP endpoint without proper authentication scoping. Attackers enumerated all multiple+ tools, exfiltrated configuration files, and deployed ransomware. Remediation costs exceeded $multiple million, including forensic analysis and data recovery. Source: Adapted from Verizon DBIR supply chain incidents.
Case Study 2: Concurrent Access Corruption
In a multi-agent RAG pipeline, missing file locks allowed overlapping uploads to corrupt a multiple dataset. This caused multiple-hour production downtime and $multiple in lost revenue for an AI analytics firm. Similar incidents appear in IBM's report under lost business costs.
Case Study 3: Shadow AI Breach
IBM notes multiple% of organizations lack AI governance, leading to shadow MCP deployments. One firm suffered a breach when an unauthorized agent tool accessed customer PII, resulting in regulatory fines and reputational damage averaging $multiple.5M.
Fastio's hosted MCP includes granular RBAC, permanent logs, auto-expiring sessions, and built-in locks by default. This reduces these risks.
MCP Security Fundamentals
Build a secure MCP foundation with these core principles, aligned to industry standards like OWASP API Security Top 10. Authentication Mechanisms Short-lived JWT tokens expire in multiple hour for session access. Revocable API keys suit long-running agents. PKCE OAuth flows work for browser-integrated tools. SSO/SAML handles enterprise integration. Avoid permanent tokens. Rotate every multiple days. Fastio supports all these out of the box, with PKCE scoping to specific org/workspace/share.
Role-Based Access Control (RBAC) Define least-privilege roles: owner (full CRUD + admin), admin (user management + permissions), member (read/write files), guest (upload/view only), viewer (read only). Apply hierarchically: org > workspace > folder > file. Test cascades regularly, e.g., a workspace member can't delete org-owned files. Fastio's granular model prevents common escalation bugs.
Encryption Everywhere AES-multiple at rest with per-file keys, TLS multiple.multiple in transit (Cloudflare enforced). Customer-managed keys optional for compliance. Never log plaintext secrets. Fastio encrypts data by default, with zero-knowledge proofs for agent tools.
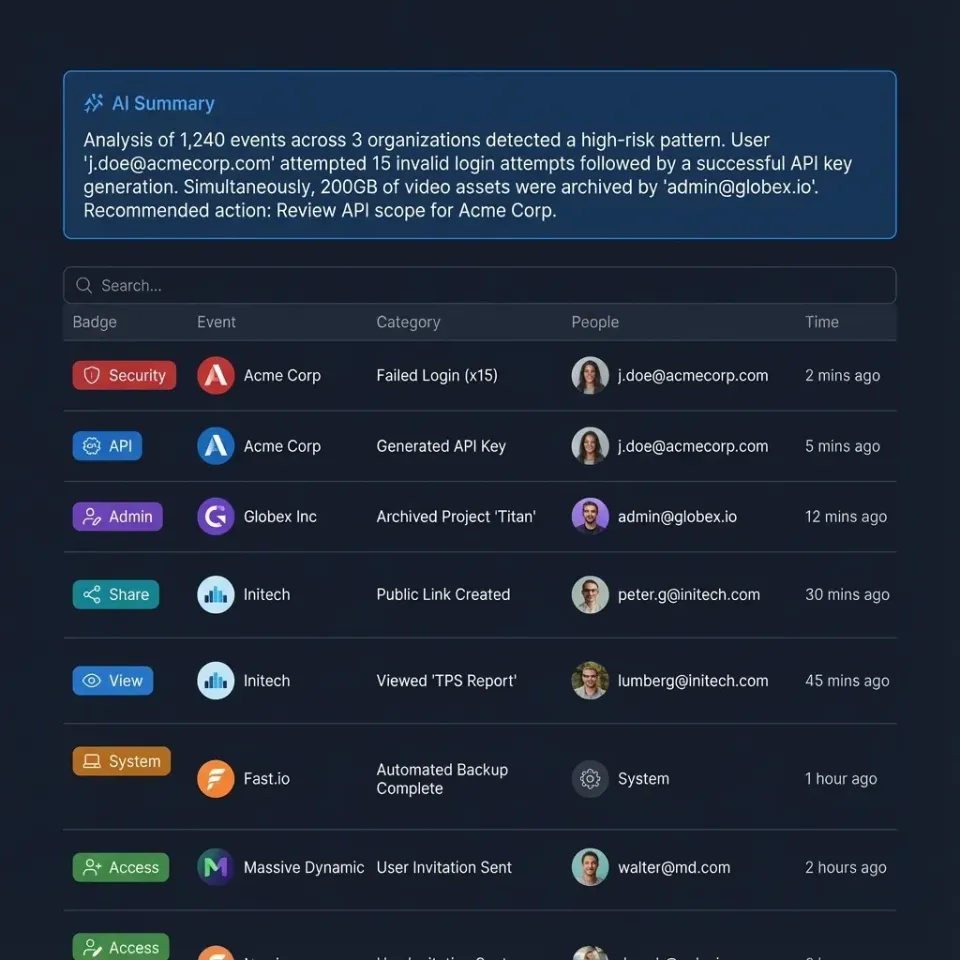
Immutable Audit Logging Capture every action: logins, tool calls, file ops, permission changes. Retain multiple+ days, with AI-powered summaries for quick reviews. Export to SIEM. Fastio logs include caller ID, IP, timestamps, and diff previews.
Concurrency Coordination File-level locks (acquire/release) prevent races in multi-agent scenarios. Add idempotency keys for retries. Locks auto-expire after multiple minutes idle.
Session Isolation Durable Objects or equivalent isolate sessions, preventing cross-tenant leaks. Scoped auth ensures tools only access permitted scopes. Establish policies upfront: access rules, log retention (min multiple year), incident response playbooks. Test in staging to mirror production behavior, avoiding "it works locally" failures.
Fastio's Built-in MCP Security
Fastio MCP secures agent access:
multiple Tools: Every UI function exposed as MCP tools via Streamable HTTP or SSE transports, with session state managed in Durable Objects.
RBAC: Permissions cascade org > workspace > folder > file.
Encryption & MFA: Always on, SSO support.
Audit Logs: Covers tool calls, AI queries, transfers. AI summaries available.
File Locks: Acquire/release for multi-agent coordination.
Ownership Transfer: Agent creates content, hands to human, retains admin.
Scoped Access: PKCE with org/workspace/share selectors.
Free agent tier: 50 GB storage, 3 workspaces, 5,000 credits/month, no credit card required.
Code example (pseudocode):
// Lock before modifying
storage.call("lock", {workspace_id, node_id});
// Modify file
storage.call("upload", {...});
storage.call("unlock", {workspace_id, node_id});
Document access rules, audit trails, and retention policies before rollout so staging results are repeatable in production. This avoids late surprises and helps teams debug issues with confidence.


Start Secure MCP Storage
251 tools with full security, 50 GB free. Start secure agent workflows today. Built for secure mcp tool storage workflows.
Implementing Secure MCP Storage Step-by-Step
Follow this complete workflow to deploy secure MCP tool storage on Fastio, from signup to production monitoring.
Step 1: Agent Account Creation
Agents register like humans. No special setup needed.
const signupResponse = await mcp.auth.signUp({
first_name: 'Agent',
last_name: 'SecureMCP',
email: 'agent@yourteam.com',
password: 'StrongPass123!'
});
// Verify email (automated or manual token)
await mcp.auth.emailVerify({email_token: signupResponse.token});
Step 2: Organization Setup
Create a dedicated org on the agent plan for isolation.
const org = await mcp.org.create({
billing_plan: 'agent',
name: 'SecureMCPTools'
});
Step 3: Secure Workspace Provisioning
Enable Intelligence Mode for RAG and workflows.
const workspace = await mcp.workspace.create({
org_id: org.id,
name: 'SecureAgentTools',
intelligence: true, // Auto-index for RAG
workflow: true // Webhook support
});
await mcp.workspace.enableIntelligence({workspace_id: workspace.id});
Step 4: RBAC Configuration
Add humans/agents with precise roles.
await mcp.member.add({
profile_type: 'workspace',
profile_id: workspace.id,
email: 'human@team.com',
role: 'admin'
});
// Verify permissions
const perms = await mcp.member.permissions({
profile_type: 'workspace',
profile_id: workspace.id
});
console.log(perms); // Confirm 'edit', 'delete', etc.
Step 5: Secure File Operations with Locks
Demonstrate lock-upload-unlock cycle.
// Acquire lock
await mcp.storage.lock({
workspace_id: workspace.id,
node_id: 'sensitive-report'
});
// Upload
await mcp.storage.upload({
workspace_id: workspace.id,
parent_id: 'root',
name: 'secure-report.pdf',
content: fileBuffer // Up to 1GB chunked
});
// Release
await mcp.storage.unlock({
workspace_id: workspace.id,
node_id: 'sensitive-report'
});
Step 6: Intelligence and Monitoring
Scoped RAG chat, audit review.
const chat = await mcp.ai.chatCreate({
context_type: 'workspace',
workspace_id: workspace.id,
type: 'chat_with_files',
folders_scope: 'root'
});
// Review logs
const logs = await mcp.event.list({
scope: 'workspace',
workspace_id: workspace.id,
limit: 50
});
Full documentation: Fastio MCP Skill Guide, Agents Page.
Troubleshooting Common Issues
Permission Denied (403):
Query member.permissions() to audit. Ensure role grants required actions (e.g., 'storage.write'). Update with member.updateRole({role: 'member'}).
Lock Acquisition Fails:
Check lock.status(). Admins use lock.forceRelease(). Locks auto-expire after multiple minutes idle to prevent deadlocks.
Rate Limits Hit (429):
Agent tier: ~multiple RPM. Monitor usage.get(). Implement exponential backoff:
if (response.status === 429) {
await new Promise(r => setTimeout(r, 2 ** retryCount * 1000));
}
Missing Audit Logs:event.list({scope: 'workspace'}). multiple-day retention, AI summaries in Intelligence Mode. Export via webhook.
OpenClaw Integration:
clawhub install dbalve/fast-io
Test: "List files in my secure workspace."
Edge Case: Concurrent Failures
Use idempotency: include idempotency_key in calls. Retries safe.
Always test in a staging org with separate billing. Simulate failures: revoke perms, overload rates, concurrent locks.
Comparisons: Fastio MCP vs Alternatives
vs Self-Hosted MCP (Docker/Fly.io):
- Fastio: Managed hosting, multiple tools, security included.
- Self-host: You handle infra, RBAC, logs.
vs S3 + Custom MCP:
- Fastio: Native MCP, RAG, previews, locks.
- S3: Basic storage, you build rest.
vs OpenAI Files API:
- Fastio: Files persist, any LLM, human handoff.
- OpenAI: Temporary, OpenAI only.
Ultimate MCP Security Checklist
Run this 25-point checklist:
Authentication (4 points):
- MFA for human users
- Rotate API keys every 90 days
- PKCE/OAuth for browser agents
- JWT max 1 hour expiry
RBAC & Permissions (5 points):
- Least privilege (agents member role)
- Review roles quarterly
- Test permission cascade
- Guests upload/view only
- Tools check permissions first
Encryption & Secrets (3 points):
- AES-multiple at rest, TLS multiple.3 in transit
- No secrets in code (use a secrets manager)
- Documented key rotation
Monitoring & Logging (4 points):
- Logs enabled, alerts on odd activity
- Weekly AI log summaries
- Webhook alerts for locks/failures
- Track usage (credits, rate)
Multi-Agent (4 points):
- Lock before every change
- Idempotent ops
- Conflict plan
- Limit concurrent locks/file
Shares & Transfers (3 points):
- Password/time-bound shares
- Audit before transfer
- Test ownership transfer
Extra (2 points):
- Intelligence Mode for RAG logs
- Backup webhooks, recovery plan
Test in small setup first. Roll out once stable.
Frequently Asked Questions
What makes MCP storage insecure?
No RBAC lets anyone in. Missing logs hide attacks. No locks cause overwrites. Fastio includes RBAC, logs, locks, MFA.
Best practices for MCP RBAC?
Least privilege roles. Quarterly audits. Test org-to-file flow. Fastio supports granular permissions.
Fastio MCP free limits?
50 GB storage, 1 GB max file size, 5,000 credits/month, 3 workspaces, 50 shares, unlimited files within limits. No credit card required. Upgrade anytime.
How to lock files in multi-agent?
Call storage.lock before edits, unlock after. Prevents races.
Does Fastio log MCP calls?
Yes, full audit trail with AI summaries for every call.
Secure transfer to human?
Use org.transfer_token_create for claim URL after agent builds.
MCP vs function calling?
MCP has stateful sessions and multiple tools. Functions are stateless single calls.
Works with OpenClaw?
Yes. Run `clawhub install dbalve/fast-io` for zero-config access.
Related Resources

Start Secure MCP Storage
251 tools with full security, 50 GB free. Start secure agent workflows today. Built for secure mcp tool storage workflows.
