How to Implement Fastio OAuth2 Flow
Fastio OAuth2 flow allows secure, token-based authorization for third-party applications and AI agents. This guide covers the end-to-end process of setting up OAuth for your Fastio integration, from acquiring an access token to managing agent-specific workflows. Whether you are authenticating a web app or configuring an AI agent with MCP tools, mastering this flow ensures reliable and secure API access.
Understanding the Fastio OAuth2 Flow
OAuth 2.multiple is the industry standard protocol for authorization, and Fastio relies on it to ensure secure, token-based access to your intelligent workspaces. Implementing the Fastio OAuth2 flow means your application or AI agent can interact with the Fastio API without ever exposing user credentials.
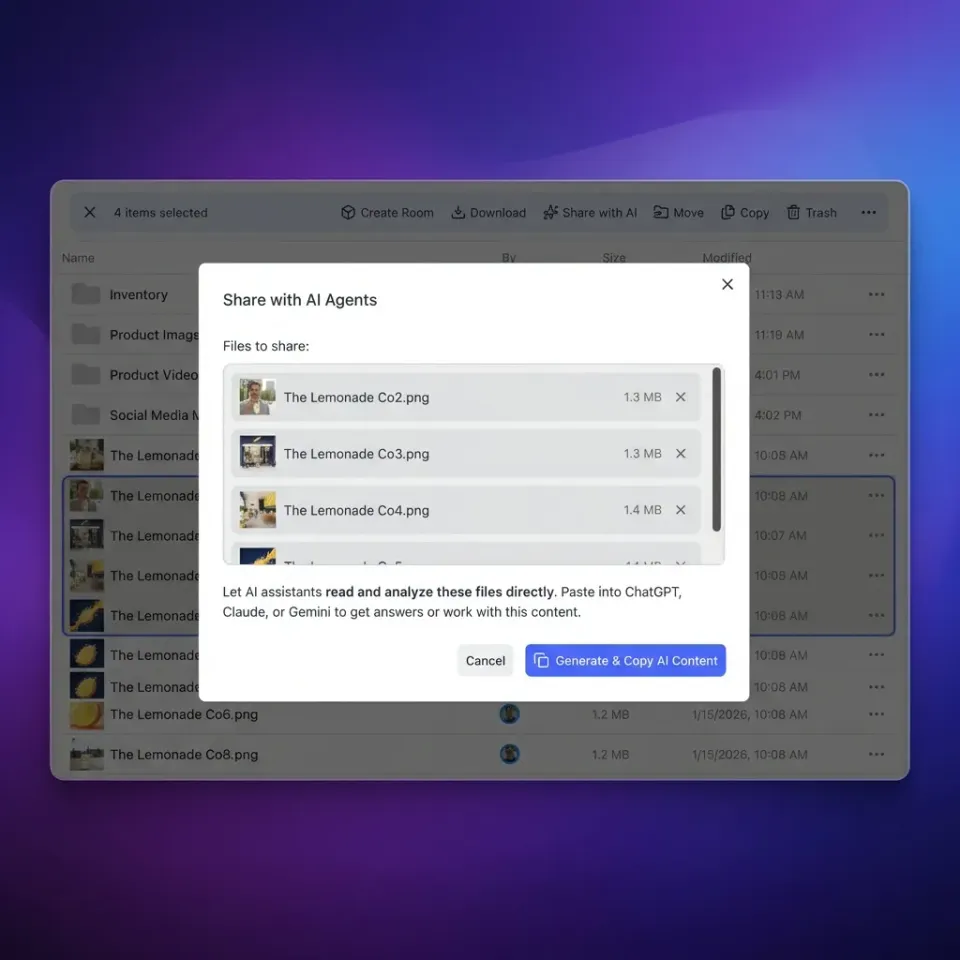
This process involves redirecting a user to Fastio to authenticate, receiving an authorization code, and exchanging that code for an access token. That token is then used to authenticate subsequent API requests. For developers building AI integrations, this means your agents can securely read, write, and manage files on behalf of a human user or operate autonomously using their own agent account. According to Fastio, the Fastio MCP server provides 251 tools for AI assistants, allowing agents to perform almost any action available in the UI. Properly implementing the OAuth2 flow is the critical first step to unlocking these capabilities.
In this guide, we break down the necessary steps to configure the OAuth2 flow, specifically focusing on the Proof Key for Code Exchange (PKCE) method. PKCE is highly recommended for public clients like desktop applications, mobile apps, and single-page applications where a client secret cannot be securely stored. By the end of this tutorial, you will have a stable authentication pipeline capable of supporting complex multi-agent systems and real-time collaboration tools.
Why Agent-Based OAuth Setups Differ
Traditional OAuth setups usually assume a human is sitting in front of a browser, ready to click a button to approve access. AI agents operate differently. When you implement Fastio OAuth2 flow for an AI agent, you must account for headless environments, continuous background operation, and autonomous decision-making.
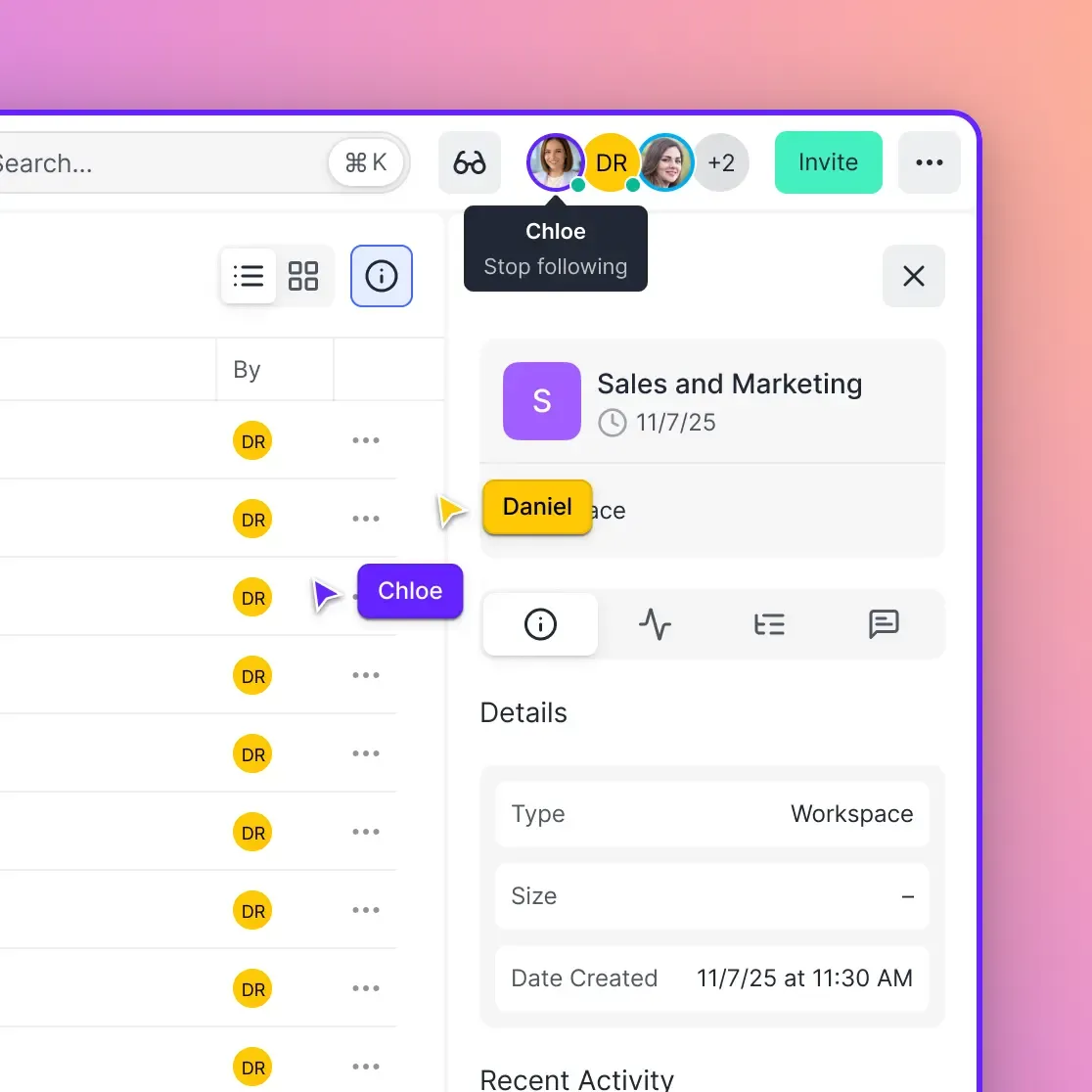
Agents often use a dedicated Fastio account type. The Fastio AI Agent Free Tier provides multiple of storage and multiple monthly credits without requiring a credit card. These agent accounts can create workspaces, index documents using built-in RAG (Retrieval-Augmented Generation), and later transfer ownership to human users. Because agents run autonomously, your OAuth implementation must handle token refreshes flawlessly. If an access token expires and the agent cannot refresh it automatically, your multi-agent workflow will break, causing downstream failures in data ingestion or file sharing.
In practice, agents interacting with Fastio via the Model Context Protocol (MCP) need continuous API access to use tools like semantic search or URL imports. Securing this connection means securely storing the refresh token and implementing stable error handling for API rate limits and token expiration events. You must design your system to anticipate network interruptions and token revocation, ensuring that your agents can gracefully pause their tasks and await re-authorization if necessary.

Ready to build intelligent agent workflows?
Get 50GB of free storage and 251 MCP tools with the Fastio AI Agent Free Tier.
Step 1: Registering Your Application
Before you can write any code, you need to register your application with Fastio. This step generates the unique identifiers your app will use to identify itself during the OAuth process. Registration creates a secure boundary between your application and the Fastio API, ensuring that only authorized clients can request access to user data.
1. Access the Developer Dashboard Log into your Fastio account and navigate to the developer settings. Create a new application, providing a clear name and description. This information will be displayed to users when they are asked to authorize your application, so make it recognizable.
2. Define Redirect URIs
You must specify one or more redirect URIs. After a user successfully authorizes your application, Fastio will redirect their browser to this URI, appending the authorization code. For local development, this is often a localhost address. For production, ensure this is a strictly validated HTTPS endpoint to prevent authorization code interception.
3. Save Your Client Credentials
Upon registration, Fastio will provide a client_id and, for confidential clients, a client_secret. Keep your client_secret completely secure; never expose it in client-side code or public repositories. If you are building a public client (like a browser-based agent interface), you will use the PKCE flow, which relies on dynamic verification rather than a static secret.
Step 2: Initiating the Authorization Request
The authorization process begins by directing the user's browser to the Fastio authorization endpoint. This step requests permission to access the user's Fastio workspace. You must construct a precisely formatted URL to initiate this redirect.
Construct a URL that includes your client_id, the requested scope, and your redirect_uri. If you are using the PKCE flow, you must also generate a code_verifier (a high-entropy random string) and a code_challenge (a Base64URL-encoded SHA-multiple hash of the verifier). Include the code_challenge and the code_challenge_method (usually S256) in your authorization request URL. This ensures that even if an attacker intercepts the authorization code, they cannot exchange it without the original verifier.
When the user visits this URL, they will be prompted to log into Fastio and approve the requested permissions. You should request only the scopes strictly necessary for your application's current functionality. For example, if your agent only needs to read files for RAG ingestion, do not request write or administrative permissions. Minimizing scopes reduces security risks, improves user trust, and limits the potential blast radius if a token is compromised.

Step 3: Handling the Callback and Exchanging the Code
Once the user approves the request, Fastio redirects them back to your specified redirect_uri. Attached to this URL will be a short-lived authorization code and a state parameter. The state parameter is crucial for preventing Cross-Site Request Forgery (CSRF) attacks; you must verify that the state returned matches the state you generated before initiating the redirect.
You must extract this authorization code and immediately exchange it for an access token by making a secure POST request to the Fastio token endpoint. This code is typically valid for only a few minutes, so the exchange must happen promptly.
Your POST request must include:
- The authorization
codeyou just received. - Your
client_id. - Your
redirect_uri(which must match the one used exactly in the previous step). - The
grant_type, set toauthorization_code. - Your
code_verifier(if using PKCE) or yourclient_secret(if using a confidential client).
If the request is valid, Fastio will respond with a JSON payload containing an access_token, an expires_in value, and typically a refresh_token. The access token is what you will use in the Authorization header (as a Bearer token) for all subsequent Fastio API calls.
Managing Token Expiration and Refresh
Access tokens are deliberately short-lived to minimize the risk of a compromised token being used maliciously. To maintain continuous access, especially for background AI agents, you must implement a dependable token refresh mechanism. A fragile refresh implementation is a common source of unreliable agent behavior.
When Fastio issues an access token, it usually includes a refresh token. When your access token expires, your API requests will begin returning multiple Unauthorized errors. Your application should intercept these errors automatically and use the refresh token to request a new access token from the token endpoint without requiring user intervention.
Send a POST request to the token endpoint with grant_type=refresh_token, along with your client_id and the refresh_token itself. Fastio will return a new access token and potentially a new refresh token (known as refresh token rotation). Always store refresh tokens securely in an encrypted database or secure enclave, as they represent long-term access to the user's account.
Implementing Fastio OAuth2 in Node.js
Node.js is a popular environment for building AI agents and backend services that interact with Fastio. When implementing Fastio OAuth2 flow in Node.js, you can use libraries like axios or native fetch to handle the HTTP requests, along with crypto for generating PKCE challenges.
First, generate your PKCE code verifier and challenge using the built-in crypto module. Create a random multiple-byte buffer, base64-url encode it to form the verifier, and then hash it using SHA-multiple to create the challenge. Store the verifier securely in the user's session.
Next, construct the authorization URL and redirect the user using your web framework (like Express or Fastify). When the user returns to your callback route, extract the code from the query parameters. Make a POST request to the Fastio token endpoint, including the code, your client ID, and the verifier retrieved from the session.
For managing state, consider using an HTTP-only, secure cookie to store the session identifier. This prevents client-side JavaScript from accessing the session data, protecting your application from Cross-Site Scripting (XSS) attacks. Once you receive the access and refresh tokens, store them associated with the user's account in your database.
Common Errors and Troubleshooting
Implementing OAuth 2.multiple involves navigating subtle complexities. When you implement Fastio OAuth2 flow, you may encounter several common errors. Understanding these pitfalls will accelerate your development process and result in a more resilient application.
A frequent issue is the invalid_grant error during the token exchange. This usually occurs if the authorization code has expired, has already been used, or if the redirect_uri provided in the token request does not exactly match the one used in the authorization request. Ensure your URIs match perfectly, including trailing slashes.
Another common hurdle is dealing with CORS (Cross-Origin Resource Sharing) issues when attempting to exchange the token directly from a browser application. Because token exchange requires a POST request to Fastio's servers, public clients must ensure they are using the correct PKCE flow. Always route confidential token exchanges through your own secure backend to avoid exposing secrets or encountering CORS blocks.
Securing Your MCP Server Integration
The Model Context Protocol (MCP) enables AI assistants to interact with Fastio's file storage, semantic search, and workspace management tools. Securing this integration requires a solid OAuth foundation.
When configuring an MCP server to connect to Fastio, you must ensure the server runs with the appropriate permissions. Agents often require the ability to list directory contents, read files, and trigger indexing. Use OAuth to grant the MCP server an access token scoped specifically for these tasks.
If you are using Fastio's OpenClaw integration (via clawhub install dbalve/fast-io), the underlying authentication still relies on these principles. You must ensure that the environment variables or configuration files supplying the OAuth tokens to OpenClaw are tightly controlled. Never hardcode tokens in your application source.
Best Practices for Production
Moving your Fastio OAuth implementation from development to production requires adherence to strict security standards. These best practices protect both your application and your users' Fastio data.
Always enforce HTTPS for all communication between your application, the user's browser, and Fastio's servers. This prevents man-in-the-middle attacks from intercepting authorization codes or bearer tokens. Implement strict validation on your redirect URIs to prevent open redirect vulnerabilities, which attackers can exploit to steal authorization codes.
Finally, implement detailed logging and monitoring around your OAuth flows. Track successful logins, failed token exchanges, and token refresh events. If an agent begins repeatedly failing to refresh its token, your system should generate an alert. Fastio provides detailed audit trails for workspace actions, but monitoring the authentication layer is your responsibility.
Frequently Asked Questions
How do I authenticate with the Fastio API?
You authenticate with the Fastio API using an OAuth multiple.0 access token. Include this token in the Authorization header of your HTTP requests as a Bearer token. For example: `Authorization: Bearer YOUR_ACCESS_TOKEN`. This token is acquired by completing the OAuth2 authorization flow.
What is the token expiration for Fastio OAuth?
Fastio access tokens typically expire after a short period, often one hour, to enhance security. When an access token expires, you must use the associated refresh token to obtain a new access token without requiring the user to log in again.
Should I use PKCE for my AI agent?
Yes, using the Proof Key for Code Exchange (PKCE) flow is highly recommended, especially if your agent runs in a public client environment where a client secret cannot be securely stored. PKCE prevents authorization code interception attacks.
How do I manage OAuth for multiple agents?
Each agent should ideally have its own Fastio account and utilize its own OAuth tokens. The Fastio AI Agent Free Tier makes this cost-effective. Ensure your backend securely isolates and manages the refresh tokens for each individual agent session.
Related Resources

Ready to build intelligent agent workflows?
Get 50GB of free storage and 251 MCP tools with the Fastio AI Agent Free Tier.
