How to Share Forensic Video Securely with Forensic Data Rooms
Guide to forensic video data room secure sharing: Investigators need a secure way to share evidence without breaking the chain of custody. Since almost all criminal cases now involve digital evidence, keeping video files exactly as they were captured is a requirement for court. This guide shows how to set up sharing workflows that keep evidence safe, preserve metadata, and make it easier for legal teams to work together.

The Growing Role of Digital Video in Investigations
Case evidence now relies heavily on video and audio. While investigations used to rely on paper files and testimony, teams now manage thousands of hours of body-cam footage, CCTV, and mobile video. These files are often massive, reaching many terabytes, and usually hold the most important clues for a case. Handling this data requires more than basic cloud storage. Standard platforms don't have the controls needed to prove a file hasn't been changed. If an investigator can't show that a video is identical to the original capture, the defense can push to throw it out. This makes the storage environment as important as the evidence itself.
Forensic data rooms fill the gap between high-performance storage and legal rules. They let teams store high-resolution video at scale while following the security protocols courts expect. Moving to digital-first evidence management isn't just about convenience; it's about protecting the justice system. For example, a single homicide case can generate massive volumes of video data from public and private cameras. Managing this volume without a specialized system leads to human error, lost files, and missed deadlines.
According to reports from the Bureau of Justice Statistics, more than 90% of criminal cases now involve some form of digital evidence. This trend is accelerating as more municipalities deploy smart city technology and police departments expand body-worn camera programs. The challenge for legal teams is no longer just finding the evidence, but managing it in a way that satisfies the strict requirements of discovery and trial.
Helpful references: Fastio Workspaces, Fastio Collaboration, and Fastio AI.
What is a Forensic Video Data Room?
A forensic video data room is a secure space built to store and share sensitive video evidence. Unlike generic data rooms that focus on PDFs, forensic solutions are built for the heavy demands of video files. They use high-speed streaming and digital signatures to make sure every byte of evidence stays exactly as it was found. The goal is to provide a "single source of truth." When law enforcement, prosecutors, and defense attorneys all need to see the same evidence, they need a controlled space to do it.
The data room acts as neutral ground, giving people access without risking the original file's metadata or bit-perfect quality. The platform handles complex metadata, multiple audio tracks, and proprietary video formats. It also needs to deliver video quickly to remote reviewers who might not have forensic hardware. By centralizing these tools, agencies reduce the risk of leaks and keep the "gold copy" of every video safe.
A forensic environment should also be easy for non-technical reviewers to use. If a prosecutor cannot easily scrub through a long video to find a specific timestamp, the investigation slows down. A specialized data room provides these playback controls while maintaining the background security that proves the video being watched is the same one that was originally collected at the crime scene.
The 4 Pillars of a Forensic Video Data Room
To hold up in court, a video data room needs to do four things well. These standards keep the evidence secure and ready for trial.
Immutability: Every file uploaded gets a digital fingerprint, known as a hash, that proves it hasn't been changed. If even one pixel is altered, the hash changes, alerting investigators to tampering. This hash must be generated at the moment of ingestion and verified every time the file is accessed. 2.
Chain of Custody: The platform records every single interaction. This includes who viewed a file, when, and from where. A detailed audit log is the backbone of a strong legal case. If there is a gap where the log shows access but no identifiable user, the evidence could be considered compromised. 3. High-Capacity Performance: Forensic video files are huge. A real forensic data room supports terabyte-scale storage and lets people stream video without waiting for a long download. This is important for legal teams operating under discovery deadlines where every hour counts. 4.
Secure Access: Multi-factor authentication and expiring share links are required. Access is restricted to people involved in the case, with no risk of public exposure.
According to the National Institute of Justice, a clear chain of custody is the most important factor in keeping evidence from being suppressed. Without these pillars, even the best video evidence can become useless in court. In many cases, the technical "how" of the evidence storage is the first thing a defense attorney will challenge.


Need a Secure Space for Forensic Video?
Protect your evidence with forensic-grade sharing, TB-scale performance, and airtight chain of custody. Start your secure workspace for free today. Designed for forensic video data room secure sharing workflows.
Tracking the Chain of Custody for Video Evidence
The chain of custody is the record of who had control of the evidence. In the physical world, this is a paper trail. In the digital world, it's an automated log. When you share a video through a forensic data room, the system captures a "handshake" between the sender and the receiver. This digital handshake includes the user ID, IP address, timestamp, and the action taken, such as viewing, downloading, or commenting.
Standard file-sharing tools often fail here. If you send a video via a link that anyone can click, the chain of custody is broken because you can't prove exactly who saw it. Forensic data rooms solve this by requiring identity verification for every recipient. Everyone who touches the evidence is identified and logged. This means requiring a login or a unique access code sent to a verified email address before anyone can preview the video.
The system also needs to stop unauthorized sharing. Features like dynamic watermarking can put the viewer's name and IP address right on the video in real-time. If a clip is leaked, the watermark points directly to the source of the breach. This accountability is key for sensitive investigations where public leaks could bias a jury or endanger witnesses. By making the consequences of a leak clear and traceable, agencies reduce the risk of internal or external data theft.
Metadata Preservation: The 'Hidden' Evidence
When we think of video evidence, we usually focus on the visual image. However, for forensic investigators, the metadata is often just as important. Metadata includes the date and time the recording started, the GPS coordinates of the camera, the device serial number, and technical details like the frame rate and codec. This information can prove that a video was recorded where and when the witness says it was.
Standard file-sharing platforms often strip metadata to save space or for privacy. In a forensic context, stripping metadata is a form of evidence destruction. A forensic video data room must preserve this data in its original form. It should also index this metadata so that investigators can search for files based on location or time. For example, an investigator should be able to search for video recorded near a specific landmark within a narrow time window.
Fastio's Intelligence Mode goes further by auto-indexing metadata and content. This allows for semantic search across thousands of files. Instead of manually checking hundreds of CCTV feeds, an investigator can query the system for specific events described in the metadata. This preservation and indexing capability is what turns a simple storage bucket into a powerful investigative tool.
Evidence and Benchmarks: The Impact of Secure Sharing
The numbers show why forensic sharing is so important. Digital evidence is growing fast, and video is the main reason storage costs and complexity are rising for law enforcement. According to the Innocence Project, misapplied forensic science contributed to nearly a quarter (24%) of all wrongful conviction cases. While that study focused on forensic science, the principle applies to video: if the handling isn't perfect, the outcome can be an injustice.
Reports from the Bureau of Justice Statistics show that over 90% of criminal cases now involve some form of digital evidence. In many areas, failing to provide a full audit trail or losing evidence integrity has led to cases being dismissed. For example, bad metadata handling can make it impossible to prove when a recording was made, leading to its exclusion in court.
Using a dedicated forensic video data room can reduce the time spent on evidence discovery. The centralized review process removes the need to ship hard drives or manage different storage buckets. The efficiency helps, but the main benefit is knowing the evidence will be admissible in court. With "deepfakes" becoming a bigger concern, being able to prove where a video came from and that it hasn't been changed is no longer optional.
Handling the Terabyte-Scale Challenge
The size of the data is one of the hardest parts of a forensic investigation. High-definition body-cam footage or surveillance feeds can easily top many terabytes. Moving this data over normal networks is slow and leads to errors. Most virtual data rooms are made for small documents and struggle with large video files, often timing out during uploads or failing to render video previews.
Fastio is built on an architecture that supports TB-scale files natively. Investigators can pull evidence directly from cloud sources like Google Drive or OneDrive via URL import, skipping local storage bottlenecks. This means the evidence moves directly from the source to the secure workspace without ever sitting on an investigator's laptop or a local office server where it could be accidentally deleted or changed.
Speed matters because legal timelines are tight. If a defense team needs to review many hours of footage before a hearing, they can't wait days for files to sync. A forensic video data room that prioritizes speed alongside security keeps the legal process moving without technical delays. High-speed streaming lets reviewers jump to specific timestamps instantly, even in massive files.
Avoiding Local Storage Bottlenecks
By using URL imports and streaming, agencies can avoid the cost and risk of maintaining expensive local servers. This cloud-first approach keeps evidence accessible from any authorized location while staying under strict control. Local storage is often the weakest link in the chain of custody, as it is susceptible to hardware failure, physical theft, and unauthorized access. Moving evidence to a managed, forensic-grade cloud environment ensures higher uptime and better security.
Collaborative Review for Distributed Legal Teams
Modern investigations often involve people from multiple agencies and locations. Federal investigators might need to share data with local police, and prosecutors need to share discovery with defense attorneys. A forensic video data room must support this collaboration without putting the evidence at risk. This involves granular permissions where different users have different levels of access.
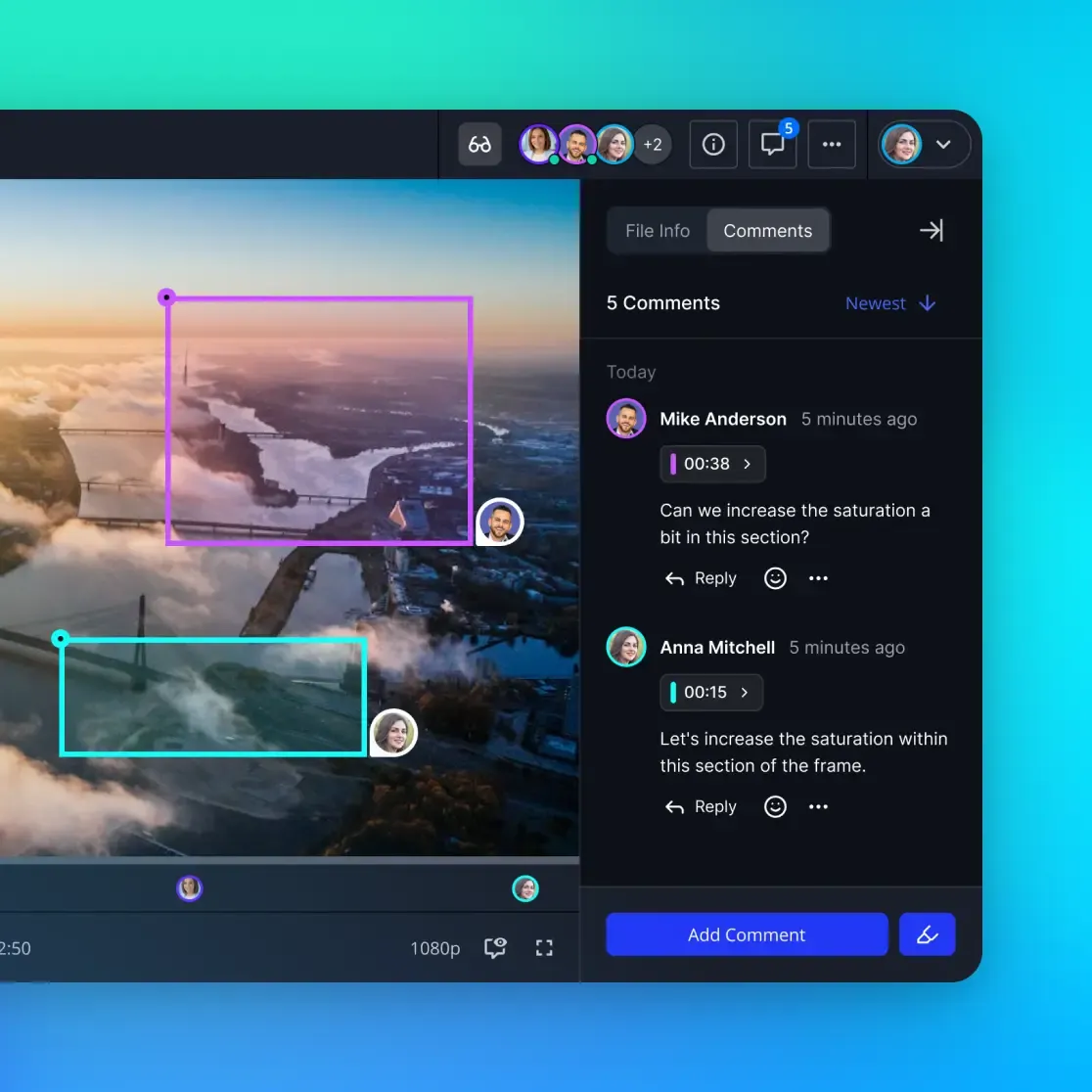
For example, a primary investigator might have full administrative rights, while a witness might only have permission to view a short clip. The system should allow users to add timestamped comments and annotations. These notes are stored in a separate layer from the original video file, ensuring that the evidence itself is never modified. These annotations can then be exported as part of a witness statement or an investigative report.
This collaborative approach also helps during the discovery process. Instead of physical hand-offs of hard drives, which are difficult to track, the entire exchange happens within the data room. This creates a clear record of when the defense received the evidence, satisfying "Brady rule" requirements for prosecutors to share evidence. It also allows for real-time discussion and review, speeding up the path to trial or settlement.
Advanced Security: MFA and Identity Verification
In a forensic environment, a simple username and password are not enough. If an unauthorized person gains access to an account, they could delete evidence or leak sensitive footage. Forensic video data rooms require Multi-Factor Authentication (MFA) to ensure that only the correct people can get in. This usually involves a code sent to a mobile device or a hardware security key.
Beyond MFA, the system should use identity verification for sharing. When an investigator shares a link with an external expert, that expert should be required to verify their identity before the link works. This can be done through Single Sign-On (SSO) integration or by requiring the user to verify their email address. These layers of security ensure that even if a share link is forwarded to someone else, that unauthorized person cannot view the evidence.
The system can also allow for "geofencing" and IP restrictions. For example, access could be restricted to only people physically located within specific regions or those using a specific agency VPN. These security measures make it much harder for unauthorized parties to access the data room, even if they somehow obtain a valid link.
Comparison: Forensic Data Rooms vs. Generic Cloud Storage
Many agencies start by using generic tools like Dropbox or Google Drive. While these are useful for general file sharing, they are not designed for forensic use. The main difference is the focus on "non-repudiation." In a generic tool, an administrator might be able to delete a file or change a log without a trace. In a forensic data room, the system is designed so that no one, not even the highest-level administrator, can hide their tracks.
Generic tools also lack the video features needed for investigations. They may not support professional video codecs, or they might compress the video for easier viewing, which changes the file's hash and ruins its forensic value. A specialized forensic data room preserves the "bit-perfect" original file while creating a separate, low-bitrate proxy for streaming. This allows for fast viewing without ever touching the evidence itself.
Finally, the support and compliance for forensic tools are different. Forensic providers understand the legal requirements and can provide the documentation to support the chain of custody in court. Generic providers often have "terms of service" that allow them to access or analyze your data for their own purposes, which is a major conflict for sensitive legal investigations.
How to Set Up a Secure Investigation Workspace
You need a clear plan to set up a secure workspace before you start moving evidence. This process ensures that the transition from collection to storage is documented and secure.
Start the Secure Workspace: Create a workspace for the specific case. Give it a unique identifier that matches your internal case management system. Turn on "Intelligence Mode" to auto-index metadata for future searches. 2.
Define User Roles: Assign specific permissions based on the "principle of least privilege." Prosecutors might need to download files for trial presentation, while external reviewers should be restricted to "View Only" to stop unauthorized copies. 3.
Ingest Evidence with Hash Checks: Upload files or use URL import. The system should automatically create a strong hash for every file right after upload to prove its integrity from day one. 4.
Enable Persistent Audit Logs: Set the workspace to capture all access events. These logs should be immutable and should include the user, timestamp, action, and IP address. 5. Use Identity-Verified Links: When sharing, use links that require email verification or SSO. Set expiration dates that match the discovery period to ensure evidence doesn't remain accessible after the case is closed.
Following these steps documents the entire life of the evidence. It turns a folder of video files into a package that's ready for court. This systematic approach reduces the stress of discovery and ensures that your evidence stands up to legal scrutiny.
Frequently Asked Questions
How do you share forensic video securely?
To share forensic video securely, use a platform that supports digital hashing for integrity, strict access controls, and full audit trails. Avoid consumer cloud storage, as these services don't have the unchangeable logs required for court. Forensic data rooms ensure that the evidence remains immutable and that every interaction is documented for legal verification.
What is a video data room for investigations?
A video data room for investigations is a secure space designed to store and share large evidence files. It includes high-speed streaming and security tools like watermarking and tamper-evident logs to keep evidence unchanged throughout the legal process. These platforms are built for TB-scale data and preserve metadata that generic storage services might strip away.
Why is chain of custody important for video evidence?
Chain of custody proves the evidence hasn't been changed since it was collected. In court, any gap in the history of who accessed a video can lead to it being thrown out, which can ruin an entire investigation. A digital chain of custody provides an automated, unchangeable record of every person who viewed or touched the file, providing the "best evidence" for trial.
Can I redact video within a forensic data room?
Many forensic platforms include redaction tools to blur faces or license plates while keeping the original 'gold copy' untouched. This helps you stay compliant with privacy laws without damaging the primary evidence. The redaction process creates a new version of the file, while the original file remains hashed and locked in the system.
How does hashing protect forensic video files?
Hashing acts as a digital fingerprint. When a file is uploaded, the system creates a unique code based on its data. If any part of the file changes, the hash won't match the original, providing proof of tampering. This mathematical certainty allows investigators to swear in court that the file has not been altered.
What happens if the metadata is stripped from a forensic video?
If metadata is stripped, you lose information like the GPS location, time of recording, and camera settings. This can make the evidence inadmissible because you can no longer prove its origin or context. Forensic data rooms are designed to preserve all original metadata within the file structure.
How long should forensic video be stored?
Storage duration depends on the statute of limitations for the specific crime and agency policy. Forensic data rooms allow for long-term archiving where files are kept in a read-only state for years. This ensures that the evidence remains available and verifiable for appeals or cold case reviews decades later.
Related Resources

Need a Secure Space for Forensic Video?
Protect your evidence with forensic-grade sharing, TB-scale performance, and airtight chain of custody. Start your secure workspace for free today. Designed for forensic video data room secure sharing workflows.
