How to Build Fastio OAuth Integration for AI Agents
Integrating Fastio OAuth for AI agents requires implementing secure token storage and automated refresh flows so the agent can maintain access to workspaces without human intervention. This guide breaks down the exact Authorization Code flow tailored for headless services. You will learn how to securely persist refresh tokens between tool calls, implement reliable API wrappers, and prevent unauthorized data access in multi-tenant environments.
What is Fastio OAuth Integration for AI Agents?
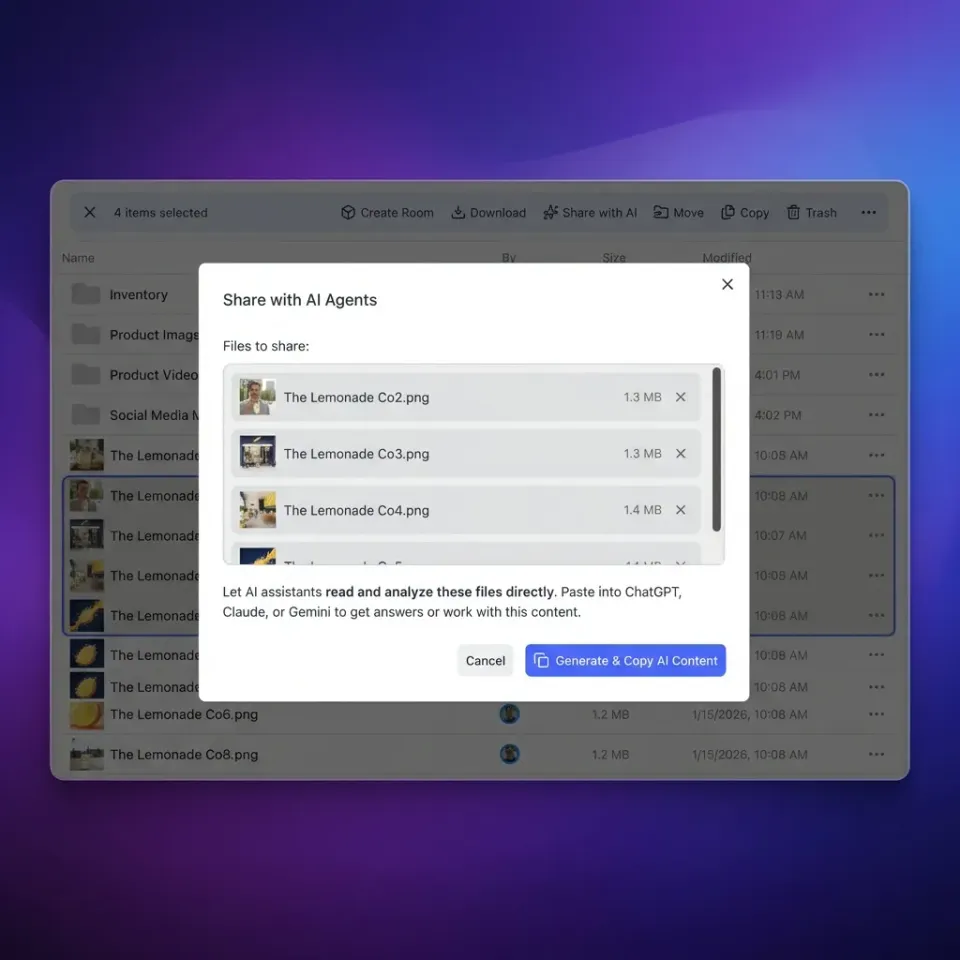
Integrating Fastio OAuth for AI agents requires implementing secure token storage and automated refresh flows so the agent can maintain access to workspaces without human intervention. Unlike traditional user applications, an AI agent operates autonomously in the background. It needs continuous, uninterrupted access to its files, data rooms, and communication channels. Fastio is an intelligent workspace, not just storage. Intelligence is native. When you upload a file, the platform automatically indexes it. It becomes searchable by meaning and queryable through chat. Agents and humans share the same workspaces and the same tools. Humans use the visual user interface, while agents use the multiple Model Context Protocol (MCP) tools available via Streamable HTTP and Server-Sent Events (SSE).
To give your agent access to these 19 consolidated tools, you must set up an OAuth integration. This process establishes a secure trust relationship between your agent backend and the Fastio platform. Once authenticated, your agent can toggle Intelligence Mode on a workspace, use built-in Retrieval-Augmented Generation (RAG) with citations, and perform complex file operations. A proper OAuth setup ensures that your agent operates with the exact permissions it needs. It also guarantees that the human user retains ultimate control over their data. This guide covers the technical implementation details required to build a reliable and secure OAuth flow for your autonomous agents.
Why Headless AI Agents Require a Unique OAuth Flow
Many guides ignore the 'headless' nature of AI agents and how to securely persist refresh tokens between tool calls. A typical web application assumes a human is sitting in front of a browser. When an access token expires, the application can simply redirect the user to a login page. An AI agent does not have a browser. It cannot click a login button or type a password. If a token expires during a long-running data analysis task, the agent will fail completely unless it knows how to renew its own access silently.
This headless operational model requires a fundamentally different approach to authentication. Your backend service must handle the OAuth handshake once with the human user. After that initial consent, the backend must take over the responsibility of token lifecycle management. This means storing credentials securely in a database, intercepting authorization errors from the Fastio API, and automatically requesting new access tokens before retrying the failed operation. This workflow is essential for building agents that feel reliable to the end user. When an agent can manage its own authentication state, it can run background jobs that last for hours or days. It can respond to webhooks when files change in a shared workspace. It can build reactive workflows without constant polling and without human supervision.
The Authorization Code Flow for Backend Agent Services
The standard Authorization Code flow requires specific adaptations when building for a backend agent service. You must separate the initial user consent step from the continuous background execution. Here is the exact sequence you need to implement.
- Initiate the authorization request from your agent backend. Construct a secure URL containing your client ID and the requested permission scopes.
- Redirect the human user to the Fastio consent screen. The user reviews the requested permissions and approves the connection.
- Receive the authorization code via your callback endpoint. Fastio redirects the user back to your server with a temporary code.
- Exchange the code for an initial access token and a long-lived refresh token. Your backend makes a secure server-to-server call to the Fastio token endpoint.
- Store the refresh token securely in your database against the agent identity. This token is the key to maintaining permanent access without further user involvement.
By following this exact sequence, you ensure that the agent never sees the user credentials. The agent only receives a scoped token that grants access to specific Fastio workspaces. This approach satisfies security best practices while enabling full autonomy for your AI service. Always implement Proof Key for Code Exchange (PKCE) even for confidential clients. PKCE adds a dynamic layer of security that prevents authorization code interception attacks.

Securely Persisting Refresh Tokens Between Tool Calls
An AI agent makes frequent, isolated tool calls. Each call requires a valid access token. Because access tokens expire quickly, the refresh token becomes the most valuable secret in your system. Securely persisting this token between tool calls is the hardest part of building a headless integration.
You must encrypt refresh tokens at rest in your database. Never store them in plain text. Use a dedicated key management service to encrypt the tokens before writing them to your storage layer. When an agent wakes up to perform a task, it retrieves the encrypted token, decrypts it in memory, and uses it to request a fresh access token. You should also write a wrapper around your Fastio API client. This wrapper should automatically catch HTTP multiple Unauthorized responses. When it catches a 401 error, the wrapper should pause the agent operation, use the refresh token to get a new access token, update the database, and then retry the original API call. This pattern hides the complexity of token rotation from the core logic of your AI agent.
When choosing a database to store refresh tokens, consider using a managed secrets engine like HashiCorp Vault or AWS Secrets Manager. These dedicated services provide built-in auditing and automatic key rotation, which significantly reduces your operational overhead. If you choose to store tokens in a standard PostgreSQL database, use application-level encryption libraries to ensure the data is never readable by database administrators. You must also implement a secure deletion protocol. When a human user revokes an agent's access from the Fastio dashboard, your system should detect the authorization failure and permanently delete the corresponding tokens from your database. Failing to clean up revoked tokens creates a large attack surface over time.
When your token wrapper works correctly, the agent never knows that authentication is happening. It simply calls the Fastio MCP tools and receives the data. This level of abstraction is necessary for complex multi-step reasoning workflows where an authentication failure would destroy the agent context. To see detailed examples of API interactions, check our storage for agents documentation.

Ready to give your AI agent a secure workspace?
Start with 50GB of free storage and 19 consolidated tools. No credit card required.
Preventing Unauthorized Data Access in Multi-Tenant Platforms
Security is the most important consideration when connecting autonomous agents to enterprise file systems. According to Microsoft Identity Platform, proper OAuth token management prevents 90% of unauthorized data access vulnerabilities in multi-tenant agent platforms. Multi-tenant systems host data for many different organizations on the same infrastructure. A minor flaw in your token logic could allow an agent acting for one company to read files belonging to another company.
Strict tenant isolation starts with granular OAuth scopes. Never request global access if your agent only needs to read files in a specific project folder. Fastio provides scoped access tokens that restrict agents to explicit workspaces. You should also implement file locks for concurrent multi-agent access. When one agent is modifying a document, it must acquire a lock to prevent other agents from creating conflicting versions. This coordination layer is what makes Fastio an intelligent workspace rather than commodity storage.
Another powerful security pattern is ownership transfer. An agent can create an organization, build out workspaces, and upload files using the free agent tier. The agent then transfers ownership of the workspace to a human client while retaining administrative access via its scoped token. This ensures the human owns the data legally and structurally, but the agent retains the technical access needed to continue its automated work.
Integrating Fastio MCP Tools via OAuth
Once your token management pipeline is stable, your agent can start using the Fastio platform. The free agent tier provides multiple of storage, a multiple maximum file size, multiple monthly credits, and requires no credit card. This generous tier lets you build and test complex workflows before deploying them to production. You can review all tier details on our pricing page.
Your authenticated agent can use the URL Import feature to pull files directly from Google Drive, OneDrive, Box, and Dropbox. This process happens entirely via OAuth and requires no local input or output operations. The Fastio servers handle the heavy lifting of downloading and indexing the external files. For developers using OpenClaw, the integration is even simpler. You can install the Fastio skill directly by running the command to install the package clawhub install dbalve/fast-io. This provides a zero-config setup with multiple foundational tools for natural language file management.
The Fastio MCP integration goes beyond basic file storage. Your agent can read rich metadata, extract text from PDFs, and transcribe audio files using the built-in intelligence features. Because Fastio handles the complex data processing, your agent backend stays lightweight and fast. You avoid the cost and complexity of running your own document parsing infrastructure. When building multi-agent systems, you can assign different Fastio workspaces to different specialist agents. A research agent can dump web clippings into one workspace, while a writing agent reads those clippings and drafts content in another. The shared OAuth token infrastructure allows these agents to collaborate securely within the boundaries you define.
Finally, consider implementing webhooks to make your agent reactive. Instead of having your agent poll the Fastio API every five minutes to check for new uploads, register a webhook endpoint during your OAuth setup. When a human drops a new video file into a shared workspace, Fastio will send an HTTP post request to your backend. Your token wrapper then retrieves the correct access token and wakes up the agent to process the new file immediately.
Managing API Rate Limits and Authentication Errors
Handling rate limits and authentication errors gracefully is a core requirement for any production AI agent. Fastio enforces rate limits to ensure platform stability across all users and agents. When your agent makes too many rapid requests, the Fastio API will return an HTTP multiple Too Many Requests response. Your backend must anticipate this response and implement an exponential backoff strategy.
Exponential backoff means your agent waits a short period before retrying the request, and then doubles the wait time for each subsequent failure. This prevents your service from hammering the API and getting temporarily banned. The Fastio response headers will include specific information about when the rate limit window resets. Your token wrapper should read these headers and pause the agent execution until the exact reset time.
When designing your retry logic, include a maximum retry count. If an API request fails five times in a row despite exponential backoff, your agent should log a critical error and halt the specific task. Infinite retry loops are a common failure mode in headless integrations and can quickly burn through your API quota. You should also monitor your token refresh success rates. A sudden spike in refresh failures usually indicates a systemic issue, such as an expired client secret or a widespread user revocation event. Setting up automated alerts for these metrics gives your engineering team time to investigate before the issue impacts your entire user base.
Authentication errors require a different recovery path. If your refresh token is revoked by the human user, the API will return an HTTP multiple Bad Request when you attempt to get a new access token. At this point, silent recovery is impossible. Your system must flag the agent as disconnected and send an alert to the human user asking them to re-authenticate. Building these error handling paths ensures your multi-tenant platform remains reliable even when individual agent connections fail. Clear communication about connection status builds trust and reduces support tickets from confused users.
Frequently Asked Questions
How do AI agents authenticate to APIs?
AI agents authenticate to APIs using OAuth multiple.multiple access tokens that are generated through an initial human consent flow. After the user approves the connection, the agent backend securely stores a refresh token. The agent then uses this refresh token to request new, short-lived access tokens for every API call, allowing it to operate autonomously without further human intervention.
How to implement OAuth for a headless agent?
To implement OAuth for a headless agent, you must build a background service that manages token rotation independently of a browser session. You start with the standard Authorization Code flow to get the first set of tokens. Then, you write an API wrapper that catches expired token errors, uses the stored refresh token to get a new access token, and automatically retries the failed operation.
What is the difference between access tokens and refresh tokens in Fastio?
An access token is a short-lived credential that your agent includes in the header of every API request to prove it has permission to perform an action. A refresh token is a long-lived credential stored securely in your database. The agent only uses the refresh token to request a new access token when the current one expires.
Can my agent use Fastio without a human user?
An agent can operate autonomously once it has an active refresh token, but the initial connection always requires human consent. For fully automated setups, you can use the ownership transfer feature. An agent can create an organization using the free tier, build the workspace, and then transfer ownership to a human while keeping its administrative token.
Does Fastio support PKCE for agent authentication?
Fastio fully supports Proof Key for Code Exchange (PKCE) and recommends it for all integrations, including confidential backend clients. PKCE adds a dynamically generated cryptographic secret to the authorization flow. This prevents attackers from intercepting the authorization code and exchanging it for an access token.
Related Resources

Ready to give your AI agent a secure workspace?
Start with 50GB of free storage and 19 consolidated tools. No credit card required.
