How to Secure Fastio MCP Tools: Authentication Guide
Securing Fastio MCP tools requires proper API key management and token-based authentication. This setup makes sure your agents only access authorized workspaces. By enforcing access controls with standard Bearer token patterns, you can safely integrate Model Context Protocol features into your production applications. The authentication layer protects your data from unauthorized access in multi-tenant LLM environments.

What is Fastio MCP Authentication?
Securing Fastio MCP tools requires proper API key management and token-based authentication. This setup makes sure your agents only access authorized workspaces. By enforcing access controls with standard Bearer token patterns, you can safely integrate Model Context Protocol features into your applications. The authentication layer protects your data from unauthorized access in multi-tenant LLM environments.
Security matters most when deploying agents that read from and write to your cloud environments. Without strong authentication, a compromised agent could leak private corporate data or corrupt your project files. Fastio uses reliable token-based authentication to establish verified identities for every API request your agents make. Whether you use a quick script or a large web application, the system tracks exactly who asks for data and what they are allowed to do.
Evidence and Benchmarks According to Fastio Documentation, Fastio provides 251 MCP tools and a free tier with 50GB storage and 5,000 monthly credits.
- Tool Access: Agents can run workflows across multiple different endpoints.
- Storage Scale: Managing 50GB of free storage requires clear access boundaries.
- Resource Protection: Enforcing authentication keeps the multiple monthly credits safe from unauthorized use. Token-based authentication protects these resources from misuse while still letting you build automated workflows.
The main goal of this authentication model is isolation. In a shared workspace where human users and AI agents work together, identity verification stops an agent from accessing files in the wrong project. This isolation helps you run agentic workflows safely across your company.
How to Generate and Manage Fastio API Keys
Generating and managing API keys correctly helps create a secure Fastio integration. Before your agent can list files, upload documents, or run semantic searches, it needs a valid credential to prove its identity to the MCP server.
You start by generating a new API key in your Fastio developer console. Go to your account settings and find the Developer Tools section. When you create a new key, the system asks for a descriptive name. Pick a name that identifies the specific agent or application using the token. Examples include "Customer Support RAG Agent" or "Data Processing Script." Good naming habits help you later when you review access logs or remove old credentials.
Step 1: Access the developer console Log into your Fastio account and open the settings panel. Go to the API Keys section to see your active tokens.
Step 2: Generate a scoped token Click the button to create a new token. You will then define the access scope. Give the agent only the specific permissions it needs to complete its task.
Step 3: Store the credential safely The system shows the raw API key just once. Copy this value and put it in a safe place like a secrets manager or a local environment variable file. Do not commit this token to your version control repository.
Managing keys over time takes some attention. When you retire an agent or change what it does, revoke its old key and issue a new one that matches the new task. Rotating keys regularly helps prevent bad actors from finding and using old credentials. Treating API keys as temporary, sensitive assets keeps your agent deployments secure.

Implementing Token-Based Authentication in Agents
Adding authentication to your agent's code means attaching your API key to every request sent to the Fastio MCP server. The process is simple, but you need to do it consistently to prevent dropped connections and unauthorized errors.
The Fastio API looks for your token in the HTTP Authorization header. You must format this using the Bearer scheme. Your header needs to look exactly like Authorization: Bearer YOUR_API_KEY. If you leave out the word "Bearer" or type the string wrong, the server will reject your request even if the key is valid.
In a Node.js environment, you can configure an Axios or Fetch client to include this header automatically. Centralizing this setup means every API call gets the right authentication details. When you set up your HTTP client, define default headers that pull the token from process.env.FASTIO_API_KEY. This keeps your business logic clean and separates credential management from your main application code.
Python developers using the requests library or asynchronous frameworks like aiohttp should build a session object with the authentication header included. Setting up a session simplifies your request code and improves performance through connection pooling. Make sure to handle cases where the environment variable might be missing. Your application should fail with a clear message during startup instead of crashing later during a file upload.
Handling Authentication Errors and Edge Cases
Handling authentication errors helps you build reliable AI agents that recover from unexpected problems. When an agent uses the Fastio MCP tools, it needs to understand and respond to HTTP status codes about identity and permissions.
The multiple Unauthorized status is the most common error you will see. This code tells you that the Fastio server either did not get a token or the token provided is invalid. When your application sees a multiple response, it should stop running and alert an administrator. This error usually means an environment variable is wrong or a key has expired. Agents should not just retry multiple errors, because a human needs to fix the broken credential first.
The multiple Forbidden status is another error to watch for. A multiple response means the server accepted your API key, but the key does not have the right permissions for that specific action. If your agent tries to delete a file using a read-only token, the server sends back a multiple error. You can fix this by changing the token's scope in the Fastio dashboard to match what the agent needs to do.
Developers also need to plan for rate limiting. Sending too many authenticated requests quickly will trigger a multiple Too Many Requests response. While this is not an authentication failure, your agents still need to handle it. They should check the HTTP headers in the response to see how long to wait before trying again. Adding an exponential backoff strategy keeps your agents within system limits while making sure they finish their tasks.
Workspace Security and Granular Permissions
Workspace security keeps agents inside their assigned boundaries and stops unauthorized access to private data. Fastio treats workspaces as isolated areas. Your authentication approach needs to align with these boundaries to keep your multi-tenant setup secure.
An agent's token permissions decide which workspaces it can see and interact with. If you set up an agent to summarize financial records, you should restrict its token to the finance workspace only. This permission model stops a single compromised token from exposing your whole company file system. You should always scope tokens to the narrowest possible access level by default.
Fastio's intelligence features, like built-in RAG and semantic search, respect these workspace rules. When an agent runs a query, the search index filters results based on the token's permissions. Two different agents asking the exact same question might get completely different answers based on the files they can read. This setup makes sure sensitive information stays within its proper department.
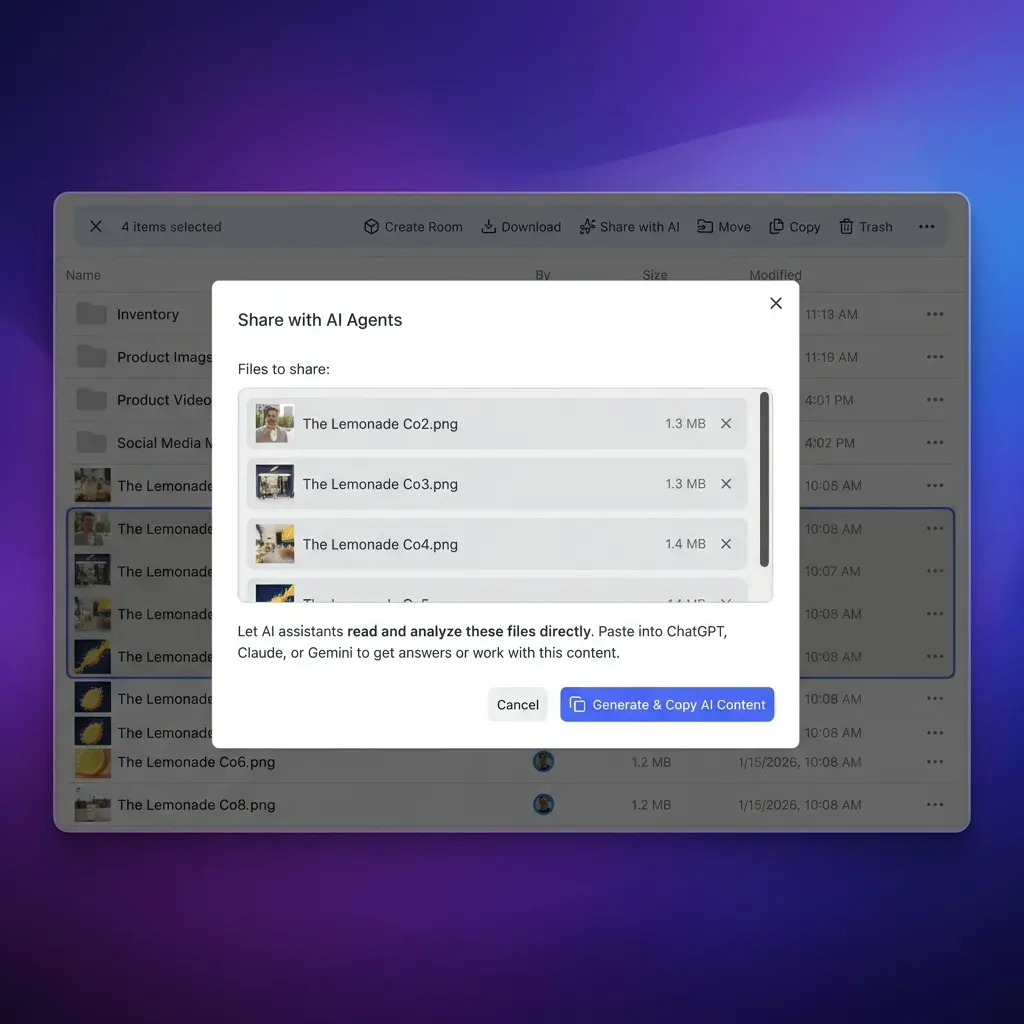
Agents can also create and manage workspaces for human users. An agent can use an administrative token to start a new environment, upload documents, and then transfer ownership to a client. The agent keeps its administrative access during this process. This lets the agent keep helping the human user without needing new credentials. This handoff helps humans and agents work together smoothly.

Multi-Tenant LLM Architectures and Security
Multi-tenant LLM architectures need clear isolation rules to stop data from mixing between different users or client organizations. Fastio gives you the secure foundation to build these systems without exposing private data to the wrong conversation context.
A single agentic backend might serve hundreds of human users in a production environment. If that backend uses one global API key to access Fastio, your application code has to handle all the authorization logic perfectly. A single bug in that routing code could let User A see User B's files. You can avoid this risk by using scoped credentials or user-specific tokens. This passes the security enforcement work to the Fastio infrastructure.
Identity propagation is a major focus for applications building OpenClaw integrations or similar tools. When a human starts a workflow, their identity needs to pass securely to the agent doing the work. The agent then uses an authentication token that matches the human's exact permissions. This setup guarantees the LLM cannot read any documents the human user is not allowed to see.
Keeping detailed audit logs also helps secure multi-tenant architectures. You should log and monitor every action an agent takes for strange behavior. Fastio provides audit trails that show exactly which token accessed specific files at any given time. Reviewing regular logs helps your security team spot credential abuse early and put automated fixes in place.

Give Your AI Agents Persistent Storage
Get 50GB of free storage and access to 251 MCP tools with our free agent tier. Built for fast mcp tools authentication guide workflows.
Advanced Authentication: Webhooks and WebSockets
Advanced authentication tasks like listening for webhooks or keeping WebSocket connections open require extra security steps beyond a basic Authorization header. These real-time connections help you build reactive agents, but they can open new security holes if you leave them unprotected.
When you configure Fastio webhooks, your application opens a public endpoint to receive event updates. You must use signature validation to verify these requests actually come from Fastio. Fastio signs every webhook payload with a cryptographic hash and puts the signature in an HTTP header. Your application calculates the expected hash using its shared secret and compares it to the header. If the signatures differ, reject the request right away to stop bad actors from faking events.
Agents connecting to the storage for agents layer through Server-Sent Events (SSE) or WebSockets need a secure initial handshake. You cannot easily send custom HTTP headers in a standard browser WebSocket connection, so developers often rely on ticket-based authentication. The agent uses its Bearer token in a regular HTTP request to get a short-lived connection ticket. You then add this ticket to the WebSocket URL as a query parameter. This grants temporary access to the real-time data stream.
Managing how these persistent connections start and stop helps keep your system secure. You should program your agents to automatically reconnect and re-authenticate if a connection drops. If you revoke an API key, the Fastio server cuts off any open real-time connections using that credential. This makes sure access stops immediately across all protocols.
Best Practices for Production MCP Servers
Following best practices for production MCP servers keeps your agent infrastructure secure and reliable over time. Security is an ongoing daily practice rather than a one-time setup step.
You should never hardcode API keys or private credentials directly into your application source code. Store these details securely as environment variables or use a secrets management service like AWS Secrets Manager or HashiCorp Vault. This habit stops accidental credential leaks in your version control system and makes it easier to rotate keys across different servers. Check our pricing plans to see the limits and quotas for different API key tiers.
You should also set up active monitoring and alerting for your authentication systems. Track how often multiple and multiple errors happen. A sudden spike in these errors often points to a bad configuration or a possible attack. Build automated alerts that notify your engineering team right away if error rates climb too high. Monitoring helps you fix security problems before they affect your users or put your data at risk.
Design your agents with defense in depth. You should not rely on Fastio's authentication alone to secure your whole application. Add your own input validation, output checking, and business logic rules. Combining reliable API authentication with safe coding habits helps you build a strong system that runs intelligent agents safely.
Frequently Asked Questions
How do I authenticate an MCP server?
You authenticate an MCP server by placing a Bearer token in the Authorization header of your HTTP requests. This token proves your agent's identity and confirms its permissions within Fastio. Correct authentication lets your tools interact with allowed workspaces while keeping data hidden from outside parties.
Are Fastio MCP tools secure?
Fastio MCP tools are secure when you use token-based authentication and scoped permissions. The platform enforces workspace isolation, so agents can only reach files and folders linked to their specific API keys. This setup prevents unauthorized data access across multi-tenant environments.
What happens if my authentication token expires?
If your token expires, the Fastio MCP server returns a multiple Unauthorized HTTP status code for new requests. Your agent needs to handle this error by stopping its current task and alerting an administrator to create a new credential. Setting up automated key rotation helps prevent these stops in production workflows.
Can I limit what my agent can do with an API key?
Yes, you can restrict an agent's access by creating scoped API keys in the developer console. You can give an agent read-only access to certain workspaces while blocking it from deleting files or changing account settings. This level of control reduces the damage a compromised credential can cause.
Related Resources

Give Your AI Agents Persistent Storage
Get 50GB of free storage and access to 251 MCP tools with our free agent tier. Built for fast mcp tools authentication guide workflows.
