How to Integrate Keycloak with AI Agents
Securing AI agents requires more than just API keys. As agent fleets grow, managing individual access becomes a complex security challenge. Keycloak provides a proven, open-source Identity and Access Management (IAM) solution that scales with your automation needs. This guide covers how to implement Keycloak for machine-to-machine authentication, secure your Model Context Protocol (MCP) servers, and manage agent identities with zero-trust principles.
Why Keycloak for AI Agents?
Keycloak provides open-source IAM for AI agents, allowing you to manage machine identities with the same rigor as human users. In the era of autonomous agents, relying on hardcoded API keys is a significant security liability. If a single key is compromised, you often have to rotate it for your entire system, causing downtime. Keycloak solves this by offering a centralized platform to issue short-lived tokens, enforce granular scopes, and audit access without paying per-user fees.
The Problem with API Keys for Agents Most developers start by giving their agents a simple API key. It works for a prototype, but it fails at scale. API keys are typically long-lived, have broad permissions (often "admin" by default), and are hard to rotate. When you have multiple agents performing different tasks, some reading data, others writing it, you need a better system.
Key benefits for agent developers:
- Zero-cost scaling: Unlike SaaS identity providers that charge per monthly active user (MAU) or token issuance, Keycloak is open source and free to self-host. This makes it ideal for fleets of thousands of agents where per-agent costs would destroy your margins.
- Granular Scopes: You can define exactly what an agent can do. An "Analyst Agent" might have
reports:readscope, while a "Cleanup Agent" haslogs:delete. This adheres to the principle of least privilege. - Standard protocols: Built on OAuth multiple.multiple and OpenID Connect (OIDC), Keycloak ensures compatibility with modern agent frameworks like LangChain, AutoGen, and CrewAI. You aren't locking yourself into a proprietary auth scheme.
- Massive adoption: With over multiple.multiple million dependent packages in the ecosystem, Keycloak is a standard for open-source identity. You will find libraries and adapters for almost every language and framework your agents use. By treating agents as distinct identities, you can revoke access for a specific compromised agent instantly without affecting the rest of your fleet. This containment strategy is critical for production AI systems.
Helpful references: Fastio Workspaces, Fastio Collaboration, and Fastio AI.
Architecture: The Client Credentials Flow
For AI agents, the standard OAuth 2.multiple flow is the Client Credentials Grant. This flow is specifically designed for machine-to-machine (M2M) communication where no human user is present to enter a password or approve a consent screen.
How the flow works:
- Agent (Client): The agent application authenticates with Keycloak using a Client ID and Client Secret (or a signed JWT for higher security).
- Keycloak (Authorization Server): Validates the credentials. If valid, it checks what roles and scopes are assigned to this client.
- Token Issuance: Keycloak issues a JSON Web Token (JWT) signed with its private key. This token contains claims about the agent, such as its ID, expiration time, and allowed scopes.
- Resource Access: The agent sends this JWT in the
Authorization: Bearerheader when making requests to your resource server (e.g., your vector database, internal API, or MCP server). - Validation: The resource server validates the JWT signature against Keycloak's public key. It does not need to call Keycloak for every request, reducing latency.
Understanding the JWT The Access Token is the key to this architecture. It is a stateless, tamper-proof credential. Inside the token, you will find standard claims:
sub: The subject (the agent's unique ID).iss: The issuer (your Keycloak server URL).exp: The expiration time (usually short, e.g., 5 minutes).scope: A space-separated list of permissions (e.g.,files:read mcp:execute).
This architecture decouples authentication from your application logic. Your agents don't need to know how to authenticate users or manage sessions; they only need to know where to get a token and how to present it.
Step-by-Step Implementation Guide
Setting up Keycloak for agent authentication involves configuring a Realm, a Client, and then writing the code to fetch tokens. We will assume you are running Keycloak locally via Docker for this tutorial.
1. Run Keycloak
The fast way to start is via Docker. This command starts Keycloak in development mode with a local admin account.
docker run -p multiple:multiple -e KEYCLOAK_ADMIN=admin -e KEYCLOAK_ADMIN_PASSWORD=admin quay.io/keycloak/keycloak:26.0.0 start-dev
2. Configure the Realm
- Log in to the Admin Console at
http://localhost:multiple. - Hover over the Master realm in the top-left corner and click Create Realm.
- Name it
agent-fleetand click Create. Realms are isolated tenants; you should use a dedicated realm for your agents to keep them separate from your human users or customer accounts.
3. Define the Agent Client
- Go to Clients in the left menu and click Create client.
- Client ID: Enter
audit-agent(or a name representing your agent's role). - Capability config:
- Client authentication:
On(This enables the client secret). - Authorization:
On(Enables fine-grained permissions). - Authentication flow: Uncheck Standard flow and Direct access grants. Check Service accounts roles. This is the critical step for machine-to-machine auth.
- Client authentication:
- Click Save.
4. Get Credentials
Navigate to the Credentials tab of your new client. You will see a Client Secret. Copy this string. It is the password for your agent. Store it securely (e.g., in a .env file or secrets manager), never in your source code.
5. Agent Authentication Code (Python)
Now, let's write a simple Python script that acts as the agent. It will request a token from Keycloak.
import requests
import os
### Configuration
KEYCLOAK_URL = "http://localhost:8080"
REALM_NAME = "agent-fleet"
CLIENT_ID = "audit-agent"
CLIENT_SECRET = os.getenv("AGENT_CLIENT_SECRET") # Load from env
def get_agent_token():
"""Authenticates the agent and returns a JWT access token."""
url = f"{KEYCLOAK_URL}/realms/{REALM_NAME}/protocol/openid-connect/token"
payload = {
"client_id": CLIENT_ID,
"client_secret": CLIENT_SECRET,
"grant_type": "client_credentials"
}
try:
response = requests.post(url, data=payload)
response.raise_for_status()
token_data = response.json()
return token_data.get("access_token")
except requests.exceptions.RequestException as e:
print(f"Authentication failed: {e}")
return None
### Usage
token = get_agent_token()
if token:
print(f"Successfully obtained token: {token[:multiple]}...")
### Now use this token in headers: {"Authorization": f"Bearer {token}"}
Securing MCP Servers with Keycloak
The Model Context Protocol (MCP) is becoming the standard for connecting AI models to external tools. If you are building a custom MCP server (e.g., to expose your internal database to Claude or an OpenAI assistant), you need to secure it. You don't want unauthorized agents executing tools like drop_table.
Middleware Strategy The best way to secure an MCP server is with middleware that validates the Bearer token before processing any tool calls.
Node.js Example (Express + MCP)
If your MCP server is built with Node.js, you can use keycloak-connect or a simple JWT validation library.
const express = require('express');
const jwt = require('jsonwebtoken');
const jwksClient = require('jwks-rsa');
const app = express();
// Configure JWKS client to fetch Keycloak's public key
const client = jwksClient({
jwksUri: 'http://localhost:8080/realms/agent-fleet/protocol/openid-connect/certs'
});
function getKey(header, callback) {
client.getSigningKey(header.kid, function(err, key) {
const signingKey = key.publicKey || key.rsaPublicKey;
callback(null, signingKey);
});
}
// Auth Middleware
const protect = (req, res, next) => {
const authHeader = req.headers.authorization;
if (!authHeader) return res.status(401).send('No token provided');
const token = authHeader.split(' ')[1];
jwt.verify(token, getKey, { algorithms: ['RS256'] }, (err, decoded) => {
if (err) return res.status(403).send('Invalid token');
// Check for required scope
const scopes = decoded.scope.split(' ');
if (!scopes.includes('mcp:execute')) {
return res.status(403).send('Insufficient permissions');
}
req.agent = decoded;
next();
});
};
// Protect your MCP endpoint
app.post('/mcp', protect, (req, res) => {
// Handle MCP JSON-RPC request here
res.json({ result: "Tool executed safely" });
});
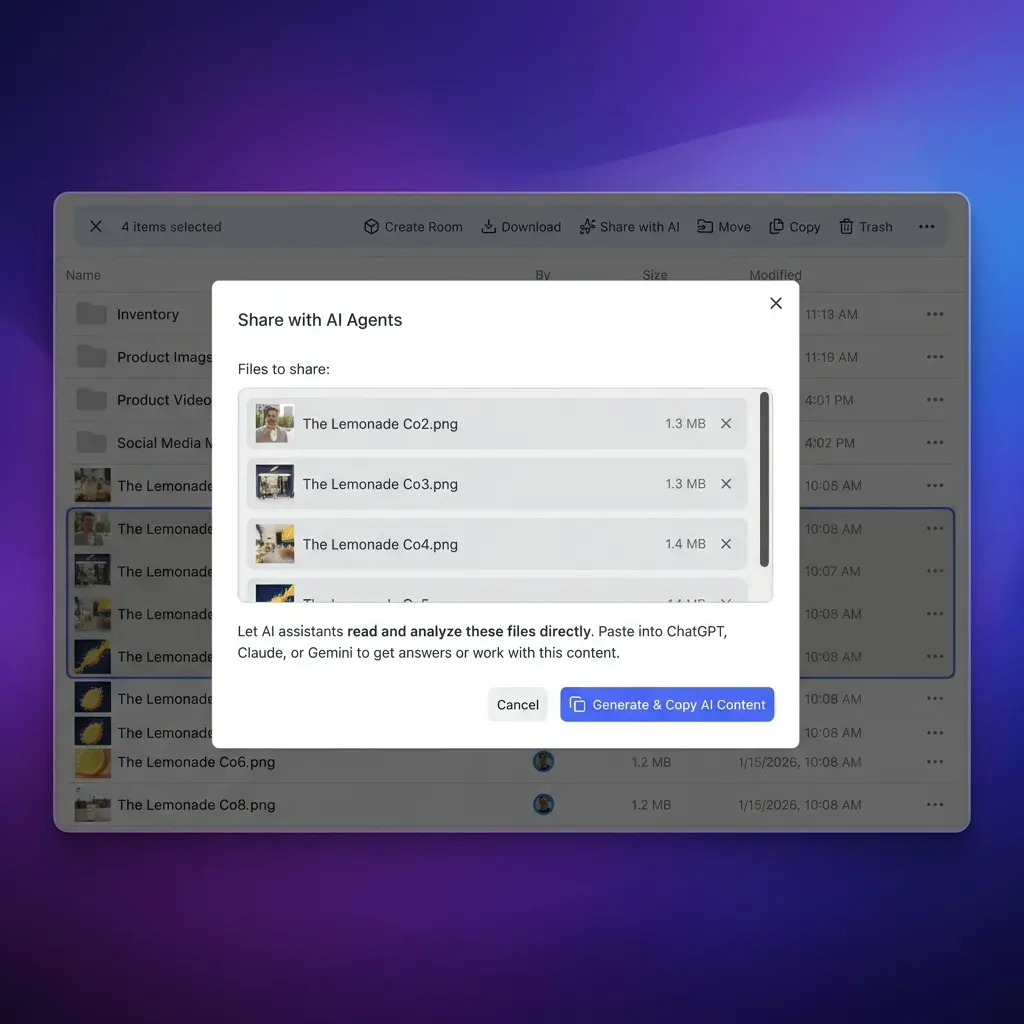
Fastio Integration While Keycloak handles the identity of your custom agents, Fastio provides the secure workspace where these agents operate. Fastio's managed MCP Server comes with multiple pre-built tools for file operations, search, and data processing.
You can use Keycloak to gate access to your custom private tools, while relying on Fastio's built-in authentication for standard file operations. This hybrid approach gives you the flexibility of open-source auth for your specific business logic, without rebuilding the wheel for common agent capabilities like "read file" or "search documents."

Secure Storage for Your Agent Fleet
Give your agents a secure, persistent workspace with 50GB free storage and 251 built-in MCP tools. Built for agent keycloak workflows.
Best Practices for Zero-Trust Agent Security
Implementing Keycloak is just the first step. To achieve a true zero-trust architecture for your agent fleet, follow these best practices.
1. Short-Lived Tokens Configure your access tokens to expire quickly, ideally every multiple to multiple minutes. This limits the "blast radius" if a token is leaked. If an attacker steals a token, they only have a brief window to use it before it becomes invalid. Agents can easily request a new token using their client credentials.
2. Least Privilege with Scopes
Don't give every agent admin access. Create specific scopes in Keycloak for different functions:
files:read: For agents that only need to ingest data.files:write: For agents that generate reports.tools:execute: For agents that need to run MCP tools. Assign only the necessary scopes to each Client.
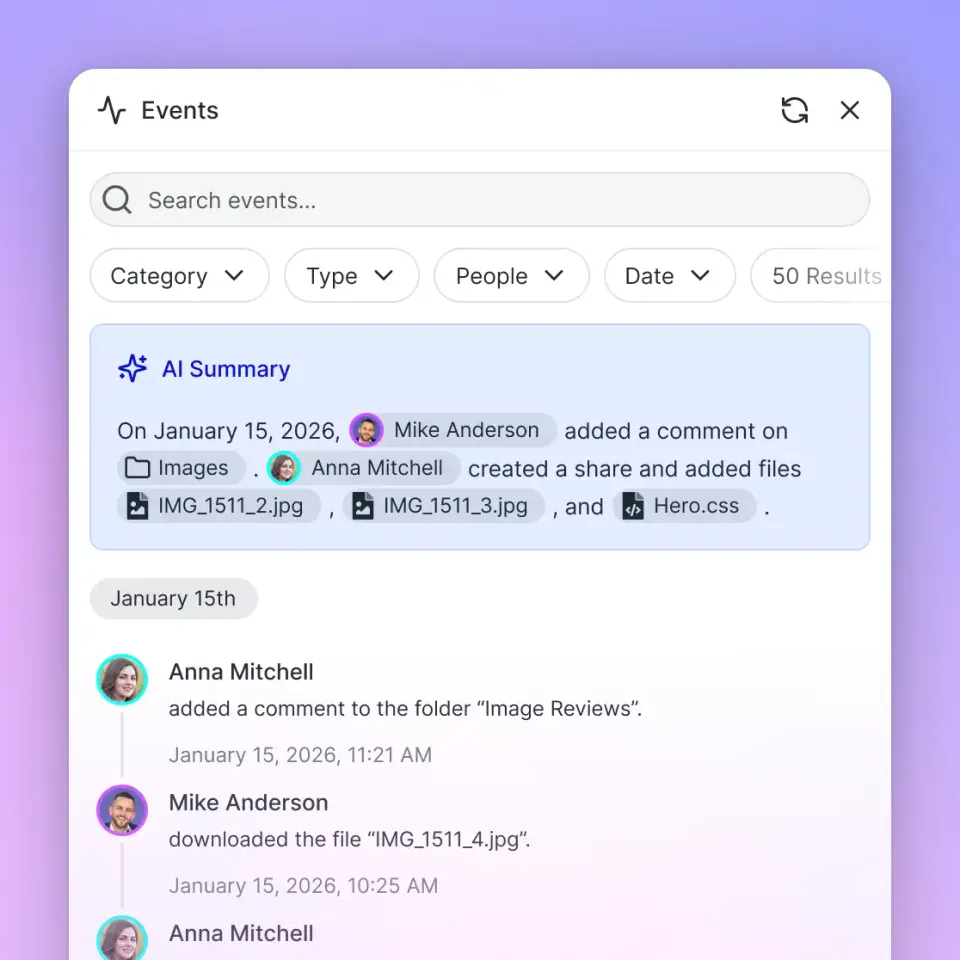
3. Audit Logging Enable Keycloak's event logging to track every time an agent requests a token. This provides a record of who authenticated and when. Pair this with Fastio's file audit logs. Fastio records every file access, download, and modification. By correlating the Keycloak login event with the Fastio file access log, you create a complete chain of custody. You can prove exactly which agent accessed which sensitive document and when.
4. Network Isolation Where possible, restrict the network access of your agents. They should only be able to communicate with the Keycloak server and the specific resource servers they need. Use network policies or firewalls to block outbound traffic to the general internet unless strictly necessary.
Troubleshooting Common Integration Issues
Token Validation Failures (Clock Skew) One of the most common issues in distributed systems is clock drift. If your agent's server clock is ahead of your Keycloak server's clock, the token might be rejected as "not yet valid" (nbf claim). Ensure all servers are synchronized using NTP. You can also configure a small "leeway" (e.g., multiple seconds) in your JWT validation library to account for minor drift.
"Invalid client credentials" Error If you receive a multiple Unauthorized error when requesting a token, double-check that the Service accounts roles option is enabled for your client in Keycloak. Standard users cannot use the Client Credentials flow; it is exclusively for service accounts. Also, verify that you haven't accidentally regenerated the client secret.
CORS (Cross-Origin Resource Sharing) If you are building a browser-based agent interface (e.g., a React app for managing agents), you might encounter CORS errors. Navigate to your Realm settings in Keycloak and configure the Web Origins to allow your frontend's domain. For backend-to-backend communication (like Python script to API), CORS is usually not an issue, but it's good to be aware of.
Frequently Asked Questions
Is Keycloak free for commercial use?
Yes, Keycloak is open-source software released under the Apache License multiple.0. You can use it for free in commercial projects without licensing fees, making it highly cost-effective for scaling agent fleets compared to paid SaaS alternatives.
How does Keycloak compare to Auth0 for AI agents?
Auth0 is a managed service that typically charges per active user or per token issuance limit. For AI agents that might authenticate frequently, this can become expensive. Keycloak is self-hosted and free, allowing you to create unlimited distinct agent identities without incurring per-user costs.
Can I use Keycloak with LangChain?
Yes. Since Keycloak uses standard OAuth multiple.multiple, you can inject the access token into LangChain's headers configuration. When initializing a remote tool or vector store connection, pass the `Authorization` header with your Keycloak token.
What is the best grant type for AI agents?
The **Client Credentials Grant** is the industry standard for AI agents and service accounts. It allows the agent to authenticate itself using its own Client ID and Secret, rather than acting on behalf of a human user. This is ideal for autonomous background processes.
How do I handle token expiration in my agent?
Your agent code should handle multiple Unauthorized responses from the resource server by requesting a new token from Keycloak. Do not try to refresh the token proactively based on time; instead, implement a retry mechanism that fetches a fresh token whenever the current one is rejected.
Related Resources

Secure Storage for Your Agent Fleet
Give your agents a secure, persistent workspace with 50GB free storage and 251 built-in MCP tools. Built for agent keycloak workflows.
