How to Implement AI Agent Infra as Code (IaC)
Deploying AI agents manually leads to "works on my machine" issues and state drift. AI Agent Infrastructure as Code (IaC) solves this by defining your agent's compute, memory, and tools in declarative configuration files. This guide shows you how to automate reproducible agent environments using modern IaC patterns and Fastio for state persistence.
What is AI Agent Infrastructure as Code?
AI Agent IaC provisions agent envs declaratively. Instead of manually clicking through cloud consoles, copying API keys into environment variables, or running ad-hoc shell scripts to set up a workspace, you define your agent environment in code: compute, network, storage, and tool access.
This approach treats your agent's infrastructure with the same rigor as its application logic. You can version control the configuration, test changes in staging, and rollback if something breaks. For agents specifically, IaC manages not just the server they run on, but the context and memory they need to operate effectively.
Unlike traditional web applications, which are often stateless and ephemeral, AI agents are stateful entities. They need to remember past interactions, access specific files, and maintain a consistent identity. This makes the "infrastructure" for an agent more complex than a simple web server. It involves provisioning:
- The Brain (Model): the LLM endpoint and configuration
- The Body (Runtime): the container or serverless function executing the logic
- The Memory (State): vector stores, file systems, and chat history
- The Hands (Tools): API integrations and MCP servers
By writing these dependencies in code, you ensure that an agent spun up today behaves the same as one spun up six months from now, assuming the underlying model hasn't drifted.
Helpful references: Fastio Workspaces, Fastio Collaboration, and Fastio AI.
Why You Need IaC for Agents
Agents are more sensitive to environmental differences than traditional web apps. A web server might throw a multiple error if a database connection fails, but an agent might "hallucinate" or execute the wrong tool if its context is slightly off.
The benefits of Agent IaC include:
- Consistency: Eliminate "drift" between development and production. If your local agent has access to a specific PDF but the production agent doesn't, the behavior will differ greatly. IaC ensures both environments match bit-for-bit.
- Scalability: Once defined in code, you can spin up multiple, multiple, or multiple identical agent instances for parallel tasks. This matters for "swarm" architectures where multiple agents handle sub-tasks.
- Security: You can audit exactly what resources and tools an agent can access. By reviewing the code, security teams can see that "Agent A" has read-only access to "Bucket B" and no access to "Payment API".
According to ResearchGate, IaC implementation leads to a 70% reduction in configuration errors. This reliability is especially important when autonomous agents act on your behalf. A misconfigured agent isn't just a bug; it's a potential security risk.
The State Management Gap in Traditional IaC
Traditional IaC tools like Terraform, Pulumi, and CloudFormation are excellent for stateless compute (like EC2 instances, Lambda functions, or Kubernetes clusters). They are designed to bring a resource to a desired state and keep it there. However, they often miss an important layer for AI agents: state management. When you deploy a web app, you typically connect it to a database and forget about it. The app itself doesn't "remember" anything. An AI agent, by contrast, is constantly evolving its state. It learns from user feedback, indexes new documents, and builds a history of actions. If you only provision the compute layer using standard IaC, your agent starts with a blank slate every time it restarts. This "amnesia" prevents agents from being useful for long-running tasks. You need to provision the state container, the persistent memory, as part of your infrastructure code.
The 3 Pillars of Agent Infrastructure
A production-ready agent environment consists of three layers. Your IaC strategy must cover all of them to be effective. Neglecting any one layer will lead to unstable or insecure agents.
1. Compute (Runtime) This is where the agent's code executes. It is the "body" of the agent.
- Containerized (Docker/K8s): Best for long-running agents that need to maintain WebSocket connections or background processes.
- Serverless (Lambda/Cloudflare Workers): Ideal for request-response agents (e.g., a chatbot that only wakes up when messaged).
- Local (On-Device): For privacy-focused agents running on user hardware.
2. Memory (State & Storage) This is the agent's "brain" and "context."
- Short-term Memory: Context window management, often handled by the orchestration framework (LangChain, etc.).
- Long-term Memory: The persistent storage of files, vectors, and logs. This is where Fastio serves as the infrastructure layer, providing a persistent, intelligent workspace that agents can access via standard APIs.
3. Tooling (Capabilities) These are the "hands" of the agent, the specialized functions it can call.
- APIs: Stripe, GitHub, Slack.
- MCP Servers: The Model Context Protocol provides a consistent way to expose local and remote tools to agents. Your IaC should define which tools are mounted and available.

Step-by-Step: Provisioning an Agent Environment
Here is a practical workflow for setting up an agent environment using IaC principles. We will use a hypothetical stack of Docker for compute, Fastio for memory, and MCP for tooling.
Step 1: Define the Compute Layer (Dockerfile)
Create a Dockerfile that bundles your agent's runtime. This ensures that the Python version, system dependencies, and libraries are identical on every machine.
FROM python:3.11-slim
WORKDIR /app
COPY requirements.txt .
RUN pip install -r requirements.txt
COPY . .
CMD ["python", "agent.py"]
Step multiple: Provision the Memory Layer (Fastio)
Instead of relying on a local data/ folder (which disappears when the container dies), provision a Fastio workspace. You can automate this using the Fastio API or CLI as part of your setup script.
This workspace becomes the agent's persistent "home directory." Any file the agent saves here is safe, backed up, and instantly indexed for search.
Step 3: Configure Tool Access (MCP Config)
Define an mcp_config.json file that lists the allowed MCP servers. This acts as an explicit allowlist.
{
"mcpServers": {
"filesystem": {
"command": "npx",
"args": ["-y", "@modelcontextprotocol/server-filesystem", "/data"]
},
"fastio": {
"command": "npx",
"args": ["-y", "@fastio/mcp-server"]
}
}
}
By committing this file to your repository, you ensure that every developer and production instance has access to the exact same set of tools.
Managing Agent State with Fastio
Fastio acts as the "State Backend" for your IaC setup. Just as Terraform uses a remote backend (like S3) to store its state file, your agents use Fastio to store their operational state.
Intelligence Mode as Infrastructure
Using Fastio as your memory layer gives you access to "Intelligence Mode." When you enable this mode on a workspace, the infrastructure handles RAG (Retrieval-Augmented Generation) for you.
- Auto-Indexing: Any file uploaded to the workspace is automatically parsed, chunked, and embedded.
- Semantic Search: The agent can query the workspace using natural language without needing a separate vector database like Pinecone or Weaviate.
- Citations: The infrastructure returns source citations with every answer, improving trust.
This allows you to simplify your agent's code. Instead of writing multiple lines of Python to manage embeddings, you make an API call to the workspace: query("Where is the project roadmap?").


Give your agents a permanent home
Provision intelligent workspaces with built-in RAG and 251+ MCP tools. No credit card required. Built for agent infra code workflows.
Security Patterns for Agent IaC
Security is often the biggest blocker for deploying autonomous agents. IaC provides a framework for implementing "Least Privilege" for agents.
1. Identity per Agent Don't share API keys. Provision a unique API key or service account for each agent instance. This allows you to revoke access for a specific agent if it starts misbehaving without taking down the entire system.
2. Scoped Tool Access
Use your mcp_config.json to strictly limit what an agent can do. If an agent only needs to read files, do not give it the "Write File" tool. If it only needs to search Google, do not give it access to your internal Slack.
3. Ephemeral Environments For high-risk tasks, spin up a throwaway environment using IaC. Let the agent perform the task in a sandboxed container with a temporary Fastio workspace. Once the task is verified, copy the result to a permanent location and destroy the environment.
Monitoring and Observability
Once your agent is running, how do you know what it's doing? Infrastructure as Code should also include "Observability as Code."
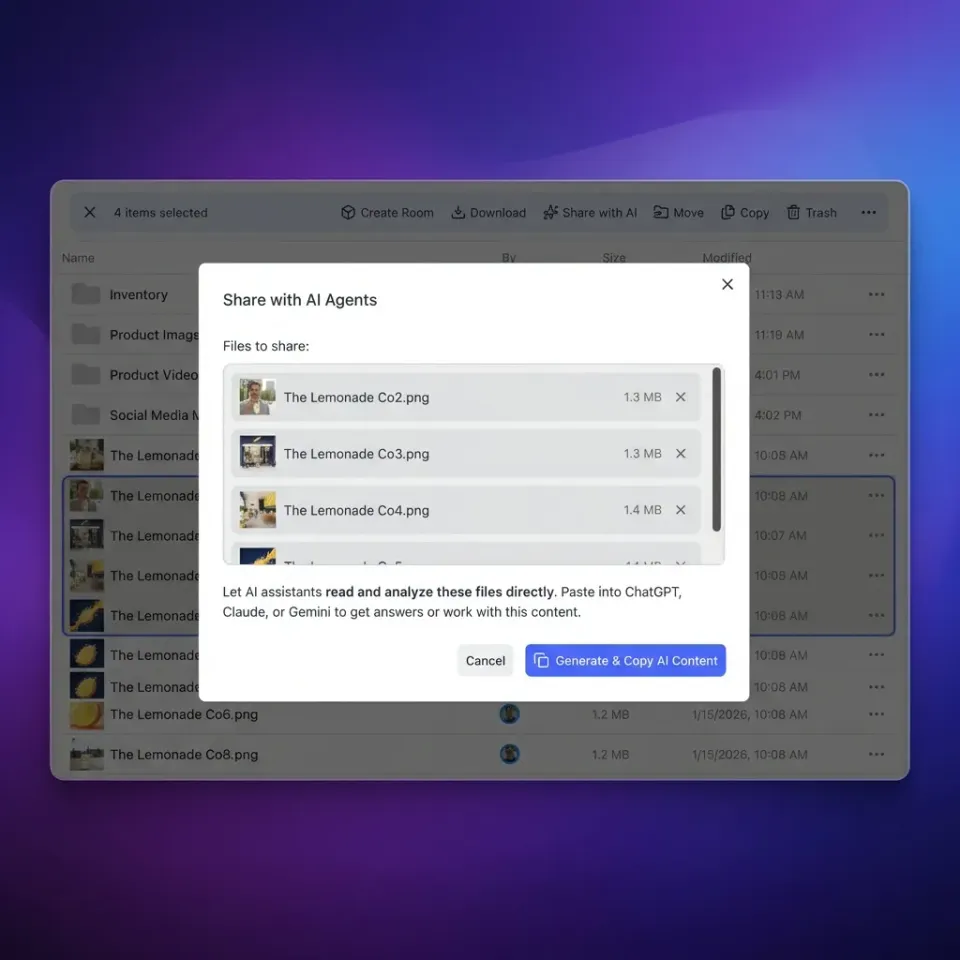
Audit Logs Fastio automatically maintains a granular audit log of every file access, modification, and share. This provides a forensic trail of your agent's activity. You can see exactly which document the agent read before it generated a response.
Performance Metrics Track the latency and token usage of your agent. Since the infrastructure is defined in code, you can easily inject monitoring sidecars or logging agents (like Datadog or Prometheus) into your container definition to capture these metrics automatically.

Frequently Asked Questions
What is the best IaC tool for AI agents?
There isn't one single tool. A common stack is Terraform for cloud resources (compute), Docker for runtime environment, and Fastio for state/memory management. This combination covers all three pillars of agent infrastructure.
How does IaC improve agent security?
IaC allows you to define strict permission boundaries in code. You can explicitly list which MCP tools and API keys an agent can access, preventing 'scope creep' where an agent has more privileges than it needs.
Can I use Kubernetes for agent orchestration?
Yes, Kubernetes is excellent for scaling agent workloads. You can define agent deployments as pods and use persistent volume claims (PVCs) or external storage like Fastio to handle state persistence across pod restarts.
How do I handle API keys in IaC?
Never commit API keys to code. Use a secrets manager (like AWS Secrets Manager, HashiCorp Vault, or GitHub Secrets) and inject them as environment variables at runtime. Your IaC should reference the secret's name, not the value.
Is Fastio a vector database?
Fastio includes vector database capabilities but is much more. It combines a traditional file system, object storage, and a vector index into a single 'intelligent workspace.' You don't need to manage vectors manually; the platform handles embedding and retrieval for you.
Related Resources

Give your agents a permanent home
Provision intelligent workspaces with built-in RAG and 251+ MCP tools. No credit card required. Built for agent infra code workflows.
