How to Set Up MCP Server Authentication
MCP server authentication is the process of verifying the identity of AI agents and applications connecting to a Model Context Protocol server, typically using API keys, OAuth tokens, or PKCE browser-based login flows. This guide walks through each authentication method with practical code examples, explains when to use which approach, and covers production hardening techniques like token rotation and scoped permissions.
What Is MCP Server Authentication?
MCP server authentication is the security layer that controls which AI clients can connect to your Model Context Protocol server and execute its tools. Without it, any agent that reaches your server's endpoint can read files, run queries, or trigger actions on your infrastructure. The risk is real. MCP adoption grew over 400% in 2025 after Anthropic open-sourced the protocol, and remote HTTP-based servers are now common. Local servers using stdio transport inherit your OS-level permissions, so authentication is less critical there. But the moment you expose an MCP server over HTTP or SSE (Server-Sent Events), you need explicit auth. The MCP specification standardized on OAuth 2.1 for authorization in March 2025, giving developers a clear path for securing remote servers. But OAuth isn't the only option, and it's not always the right one. The best approach depends on your deployment context: internal tool, commercial service, or agent-to-agent communication.

Three Authentication Methods Compared
There are three primary ways to authenticate MCP connections. Each fits a different use case.
API Keys
The server generates a unique string that the client sends in request headers, typically as Authorization: Bearer <key>. API keys are stateless: the server checks the key against a stored value and either grants or denies access.
Best for: Internal tools, single-developer setups, agent-to-server communication where you control both sides.
Limitations: API keys grant broad access. They don't support per-user permissions, and a leaked key gives full access until revoked.
OAuth 2.1 with PKCE
The MCP spec recommends OAuth 2.1 with Proof Key for Code Exchange (PKCE) for remote servers. PKCE eliminates the need for client secrets, which matters because MCP clients (desktop apps, CLI tools, browser extensions) often can't store secrets securely. The flow works like this:
- The client generates a random
code_verifierand derives acode_challengefrom it - The client redirects the user to the authorization server with the
code_challenge - The user authenticates in a browser and approves access
- The authorization server returns an authorization code
- The client exchanges the code plus original
code_verifierfor an access token
Best for: Public-facing MCP servers, multi-user systems, commercial tools.
Mutual TLS (mTLS)
Both the client and server present X.509 certificates, verifying each other's identity at the network layer. This provides the strongest authentication but requires managing a certificate authority and distributing client certificates.
Best for: Enterprise environments with existing PKI infrastructure.
Quick Decision Guide
- Building a personal tool or internal server? Start with API keys
- Building a commercial MCP server for multiple users? Use OAuth 2.1 + PKCE
- Running in a corporate network with existing certificate infrastructure? Consider mTLS
- Unsure? Default to API keys and upgrade to OAuth when you need multi-user support
How to Secure an MCP Server with API Keys
API keys are the fast way to lock down an MCP server. Here's a step-by-step setup for an HTTP-based server.
Step 1: Generate a strong key
Use a cryptographically random string. On macOS or Linux:
openssl rand -hex 32
Store this as an environment variable, never in your source code:
export MCP_API_KEY="a1b2c3d4e5f6..."
Step 2: Add authentication middleware
Intercept every incoming request and check for the key. Here's a minimal example in Node.js:
function authMiddleware(req, res, next) {
const key = req.headers['authorization']?.replace('Bearer ', '');
if (key !== process.env.MCP_API_KEY) {
return res.status(401).json({ error: 'Unauthorized' });
}
next();
}
Step 3: Configure the client
In your MCP client configuration (for example, claude_desktop_config.json), pass the key in the headers:
{
"mcpServers": {
"my-server": {
"url": "https://my-server.example.com/mcp",
"headers": {
"Authorization": "Bearer a1b2c3d4e5f6..."
}
}
}
}
Step 4: Rotate keys regularly
Set a rotation schedule (monthly for low-risk servers, weekly for production). Generate a new key, update the client config, then revoke the old key. Some teams run two keys simultaneously during the transition window to avoid downtime.

Give Your AI Agents Persistent Storage
Fast.io gives teams shared workspaces, MCP tools, and searchable file context to run mcp server authentication workflows with reliable agent and human handoffs.
How to Set Up OAuth 2.1 PKCE for MCP
For multi-user MCP servers or public deployments, OAuth 2.1 with PKCE is the right choice. The MCP spec adopted this standard because it works safely with public clients that can't protect a client secret.
Server-Side Requirements
Your MCP server needs to support these OAuth endpoints:
/.well-known/oauth-authorization-serverfor metadata discovery/authorizefor the authorization code flow/tokenfor exchanging codes for access tokens/registerif you support Dynamic Client Registration (recommended)
Dynamic Client Registration lets MCP clients register themselves automatically. Without it, you need to manually create client IDs for every client that wants to connect.
The PKCE Flow in Practice
Here's what happens when a client connects to your OAuth-protected MCP server:
- Discovery: The client fetches
/.well-known/oauth-authorization-serverto learn your auth endpoints - Registration: If supported, the client registers itself via
/registerand receives aclient_id - Challenge generation: The client creates a
code_verifier(random string, 43-128 characters) and derives acode_challengeusing SHA-256 - Authorization: The client opens a browser to
/authorize?response_type=code&code_challenge=...&code_challenge_method=S256 - User consent: The user logs in and approves the requested scopes
- Token exchange: The client sends the authorization code and
code_verifierto/token - Access: The server validates the verifier against the original challenge and issues an access token
The security comes from step 7: even if someone intercepts the authorization code, they can't exchange it without the original code_verifier that never left the client.
Token Lifetime and Refresh
Set access tokens to expire after 1 hour. Use refresh tokens (with rotation) to let clients maintain sessions without re-authenticating. When a refresh token is used, issue a new refresh token and invalidate the old one. This limits the damage from a stolen token.

Using a Managed MCP Server
Building authentication from scratch takes time, and keeping it secure takes ongoing effort. Managed MCP servers handle auth for you so you can focus on what your agents actually do. Fast.io's MCP server provides 251 tools for file operations, and authentication is built in. Here's how it works:
Account-based auth: Agents sign up for their own Fast.io accounts, just like human users. Each agent gets 50GB of free storage, 5,000 monthly credits, and no credit card is required. Authentication happens through the same secure session system that human users rely on.
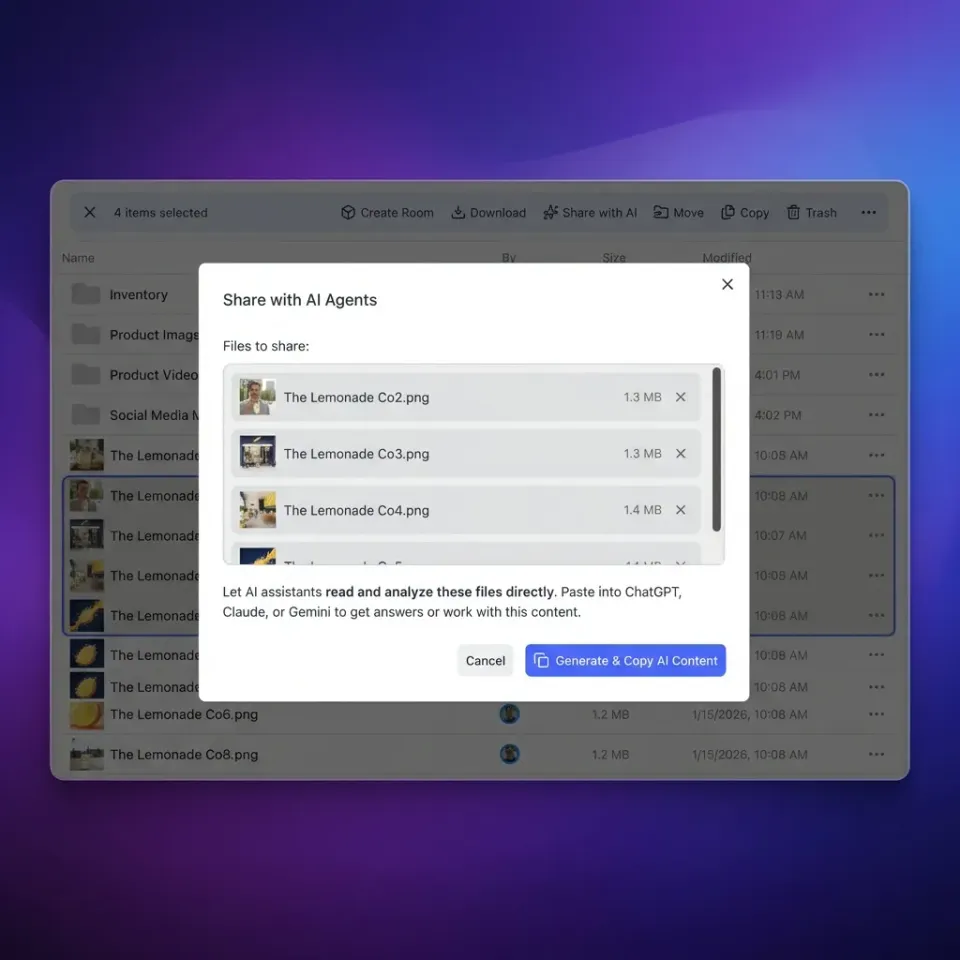
PKCE browser login: For interactive setups, agents can use PKCE to authenticate through a browser. The user approves the connection once, and the agent receives a scoped token.
Scoped API keys: For automated workflows, generate API keys scoped to specific workspaces. An agent with a key can only access the workspaces you've authorized. Keys don't expire unless you revoke them, but you can rotate them at any time.
Audit trail: Every tool call, file read, and upload is logged. You can review exactly what each agent accessed through the activity log, which tracks actions by agent identity.
Granular permissions: Rather than giving an agent full access, assign workspace-level roles (admin, member, guest). A guest agent can read files but not delete them or change permissions. The free agent tier includes 5 workspaces and 50 shares, enough for most development and testing workflows. The server supports Streamable HTTP and SSE transport, and works with Claude, GPT-4, Gemini, LLaMA, and local models.
Production Security Checklist
Whether you're running your own MCP server or using a managed one, follow these practices to stay secure:
Transport security
- Always use HTTPS. Never send tokens over plain HTTP
- Pin TLS certificates if your threat model includes sophisticated attackers
- Set
Strict-Transport-Securityheaders to prevent protocol downgrade attacks
Token management
- Store API keys in environment variables or a secrets manager, never in code
- Set access token lifetimes to 1 hour or less
- Rotate refresh tokens on every use
- Log token creation and revocation events
Input validation
- Validate all tool arguments on the server side, even from authenticated agents
- Sanitize file paths to prevent directory traversal (
../../../etc/passwd) - Rate-limit tool calls to prevent abuse from compromised agents
Monitoring
- Log every authenticated request with the client identity
- Alert on unusual patterns: high request volume, access to sensitive resources, or requests from new IP ranges
- Review audit logs weekly for unexpected agent activity
API key mismanagement is a leading cause of unauthorized agent access. The most common mistakes are hardcoding keys in agent prompts (where the LLM can see them), committing keys to git repositories, and sharing keys between multiple agents instead of issuing unique keys per agent.
Frequently Asked Questions
How do you authenticate an MCP server?
You authenticate an MCP server by requiring clients to present a credential with every request. For HTTP-based servers, this is typically an API key in the Authorization header or an OAuth 2.1 access token. The server validates the credential before processing any tool calls or resource requests. Local stdio servers rely on OS-level permissions instead.
What is PKCE authentication for MCP?
PKCE (Proof Key for Code Exchange) is an OAuth 2.1 extension that secures the authorization code flow for public clients. The MCP client generates a random code_verifier and sends a derived code_challenge to the auth server. After the user approves access in a browser, the client exchanges the authorization code plus the original verifier for a token. This prevents interception attacks because the verifier never leaves the client.
Can MCP servers use API keys?
Yes. API keys are the simplest and most common authentication method for private MCP servers. The server generates a unique key, the client sends it in the Authorization header, and the server validates it on each request. API keys work best for internal tools and single-user setups. For multi-user or public servers, OAuth 2.1 with PKCE is recommended instead.
How do you secure an MCP connection?
Secure an MCP connection by enforcing HTTPS for all traffic, requiring authentication via API keys or OAuth tokens, validating all tool inputs on the server side, and logging every request with the client identity. For production deployments, add token rotation, rate limiting, and monitoring for unusual access patterns.
Does MCP support OAuth 2.1?
Yes. The MCP specification adopted OAuth 2.1 as its standard authorization framework in March 2025. This includes support for PKCE, Dynamic Client Registration, and metadata discovery via the .well-known endpoint. OAuth 2.1 is the recommended approach for any MCP server that serves multiple users or is accessible over the internet.
Related Resources

Give Your AI Agents Persistent Storage
Fast.io gives teams shared workspaces, MCP tools, and searchable file context to run mcp server authentication workflows with reliable agent and human handoffs.
