How to Implement MCP Server Backup Strategies
Ensuring your AI agents maintain their state requires effective MCP server backup strategies. Without proper agent server persistence, you risk losing context, tool configurations, and critical workflow data. This comprehensive guide covers how to backup MCP tools effectively, prevent catastrophic data loss, and maintain highly reliable multi-agent systems for production environments. By implementing these practices, you secure your autonomous workflows against infrastructure failures.
What Are MCP Server Backup Strategies?
MCP server backups ensure tool state survives failures. As AI agents increasingly rely on the Model Context Protocol (MCP) to access tools, orchestrate workflows, and ingest external data, the state managed by these servers becomes critical infrastructure. A comprehensive backup strategy involves capturing the configuration, active sessions, file handles, and historical context of an MCP server to allow for rapid restoration in the event of an outage or error.
In a production environment, agent server persistence is not optional. When an AI agent executes a complex, multi-step workflow, such as researching a market topic, drafting a comprehensive report, querying a private database, and emailing stakeholders, it relies entirely on the MCP server to maintain continuity. If the server crashes, experiences a memory fault, or encounters a network partition and no backup exists, the agent loses its context immediately. This amnesia requires the entire workflow to restart from scratch, wasting expensive compute resources and API tokens. Implementing resilient MCP server backup strategies mitigates this risk by regularly snapshotting the server's state, enabling agents to resume tasks exactly where they left off.
This is especially important for multi-agent systems where several autonomous agents interact with the same tools simultaneously. A loss of state in a centralized or distributed MCP server can lead to massive desynchronization among the agents, causing duplicate actions, conflicting database writes, or widespread data corruption. By establishing clear protocols to backup MCP tools and their underlying data stores, organizations can build resilient AI workflows that withstand infrastructure disruptions and maintain high availability.
Why Agent Server Persistence Matters
A significant majority of agent failures stem from data loss rather than underlying logic errors. When an agent loses its connection to persistent storage, it effectively loses its memory. This makes agent server persistence a foundational requirement for any production-grade AI deployment. Without a reliable way to store and retrieve state dynamically, agents remain ephemeral scripts rather than reliable, autonomous digital co-workers capable of executing long-running tasks.
Consider a scenario where an autonomous data processing agent is tasked with analyzing a massive dataset over several hours. The agent uses an MCP server to read chunks of data, process them using an advanced LLM, and write the structured results back to a relational database. If the MCP server experiences a transient network failure or memory overload, the active session is terminated abruptly. Without adequate MCP server backup strategies, the agent has no record of which chunks were processed successfully and which remain pending. This failure forces a complete restart of the expensive, time-consuming operation, severely impacting project timelines.
The consequences of poor agent server persistence extend far beyond wasted computational resources. In collaborative enterprise environments, human users rely heavily on agents to maintain accurate, immutable records of their actions. If an agent's state is wiped due to a localized server crash, the resulting audit trail is incomplete, leading to deep trust issues and severe compliance risks. As organizations scale their AI initiatives, the complexity of managing state grows exponentially. Each new tool added to an MCP server introduces another potential point of failure, highlighting the urgent need to backup MCP tools systematically.
Common Challenges in Backing Up MCP Tools
Developing effective MCP server backup strategies requires overcoming several unique technical hurdles that do not exist in traditional web server backups. AI agent state is highly dynamic, frequently changing hundreds of times per minute as agents execute tools, receive responses, and update their internal context windows.
One major challenge is state consistency. If a backup script copies an SQLite database while an agent is actively writing a transaction to it, the resulting backup file will likely be corrupted. Ensuring transactional integrity requires implementing file locks or using database-specific backup commands, rather than relying on standard file-copying utilities. Agent server persistence demands that backups represent a perfectly consistent snapshot of the exact moment in time.
Another significant challenge is managing sensitive credentials. MCP configurations typically contain API keys, access tokens, and authentication certificates for numerous external services. When you backup MCP tools, you are also duplicating these highly sensitive credentials. If backup archives are not encrypted properly at rest and in transit, they become lucrative targets for security breaches. Ensuring that backup repositories maintain strict access controls is just as important as the backup process itself.
The scale of agent generated data can quickly overwhelm local storage. Agents that process images, generate large text corpuses, or scrape web data produce massive amounts of state information. Traditional daily snapshots are insufficient for this volume and velocity, necessitating continuous, incremental backup solutions that do not degrade the MCP server's active performance.
Step-by-Step: How to Backup MCP Tools and State
Implementing effective MCP server backup strategies requires a systematic approach to identifying, capturing, and securing state data. This process ensures that you can rapidly restore your agent infrastructure with minimal downtime. Follow these best practices to backup MCP tools securely and efficiently.
Step 1: Identify Critical State Components
The first step is to determine exactly what needs backing up. For a typical MCP server deployment, this includes core configuration files like mcp.json, custom prompt directories, environment variables containing API keys, and any local databases used for session management. Documenting these precise locations is essential for creating an automated, reliable backup routine.
Step 2: Implement Pre-Restore Snapshots Before applying any software updates or attempting a state restoration, always create a pre-restore snapshot of the current state. This acts as a safety net, ensuring that if a restoration fails or corrupts the environment, you do not overwrite your only working copy. Many modern MCP tools have built-in diagnostic commands that automatically generate these pre-restore backups.
Step 3: Schedule Automated Incremental Backups Manual backups are inherently unreliable. Instead, use advanced scheduling tools like cron jobs or dedicated backup software to automate the process entirely. For high-activity production servers, consider running incremental backups every hour, while daily snapshots may suffice for isolated development environments. Ensure your automated scripts copy the configuration files and databases to an isolated, secure directory without locking the main execution thread.
Step 4: Secure and Distribute Backups Off-Site Storing backups on the exact same machine as the active MCP server defeats their fundamental purpose. Implement standard backup rules: keep multiple copies of your data, spread across different media types, with at least one copy stored safely off-site. Cloud storage services are ideal for off-site backups, providing geographic redundancy and protection against localized hardware failures or network outages.
The Fast.io Advantage for MCP Server Backups
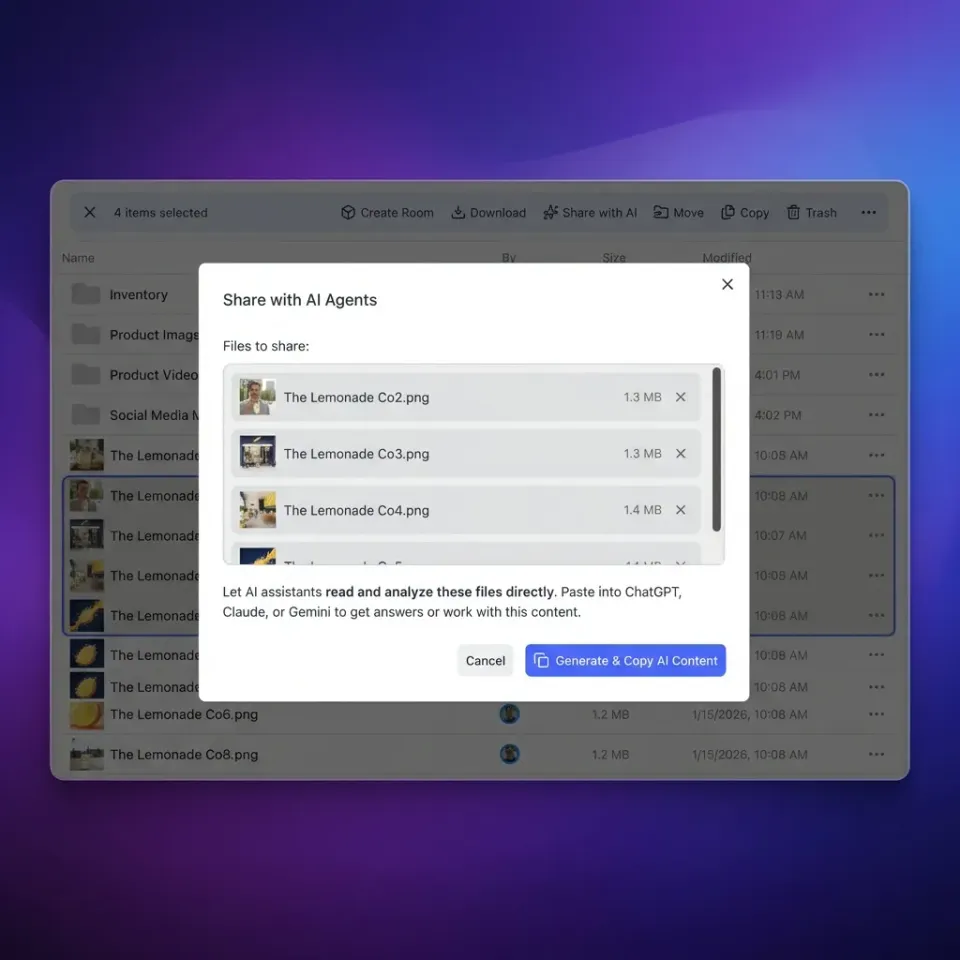
While traditional local deployments require complex, fragile scripts to backup MCP tools, modern cloud-native platforms offer a vastly superior, elegant solution. The primary competitor gap in the current AI ecosystem is the stark lack of integrated workspace backup workflows. Most platforms force developers to manage agent state manually, leading to brittle architectures. Fast.io eliminates this complexity entirely by providing intelligent workspaces where agents and humans collaborate side by side seamlessly.
The official Fast.io MCP Server provides two hundred and fifty-one powerful tools directly via Streamable HTTP and SSE transport. More importantly, session state is managed transparently in Durable Objects, ensuring high availability and built-in agent server persistence without any manual intervention required. When your autonomous agents interact with Fast.io workspaces, every single file uploaded, modified, or generated is instantly indexed and securely stored in the cloud. This organization-owned model means that critical files belong to the permanent workspace, not an ephemeral agent session.
Fast.io's cloud-native architecture inherently protects against the catastrophic data loss scenarios that consistently plague local MCP servers. With fifty gigabytes of free storage and five thousand monthly credits available specifically for AI agent accounts, developers can build reliable, persistent workflows without worrying about local disk corruption, failing cron jobs, or complex state recovery. By applying Fast.io's intelligent webhook integrations and reliable file locks, multi-agent systems can operate concurrently with guaranteed state consistency, fundamentally transforming how engineering teams approach MCP server backup strategies.


Ready to solve agent server persistence?
Stop worrying about local backups and fragile scripts. Deploy your autonomous agents on Fast.io's intelligent workspaces with built-in persistence, powerful MCP tools, and free forever storage.
Comparing Backup Approaches for Agent Infrastructure
Choosing the right architectural approach for agent server persistence depends heavily on your team's technical capabilities, security requirements, and the scale of your AI deployments. Below is a comprehensive comparison of the most common strategies used to backup MCP tools and maintain long-term state.
For individual developers building local prototypes, simple bash scripts that copy mcp.json and SQLite databases to an external USB drive are often sufficient. However, as these fragile workflows move to production, relying on local snapshots quickly becomes a severe liability. Cloud object storage improves durability significantly but still requires specialized teams to build and maintain the complex plumbing that connects the active MCP server to the storage bucket.
The absolute most reliable MCP server backup strategies actively leverage intelligent cloud workspaces that abstract state management entirely. By using modern platforms that inherently persist data globally and provide rich API access, engineering teams can focus exclusively on building highly capable agents rather than maintaining brittle backup cron jobs.
Evidence and Benchmarks for State Recovery
Regularly testing your MCP server backup strategies is the only proven way to guarantee they will actually work when disaster strikes. A backup archive that cannot be restored rapidly is practically useless in a production emergency. Industry data shows that organizations that conduct rigorous monthly recovery drills experience significantly fewer prolonged outages than those that simply assume their automated backup scripts are functioning correctly in the background.
The performance metrics clearly favor automated, cloud-native storage approaches. Systems that rely on continuous active replication or globally distributed Durable Objects recover from transient failures almost instantaneously. In stark contrast, local servers relying exclusively on nightly daily snapshots may lose up to an entire day of valuable agent context and generated data. This massive discrepancy clearly highlights the importance of choosing an underlying architecture designed specifically from the ground up for agent server persistence.
Implementing proper file locks and concurrent access controls proactively prevents state corruption during the backup process itself. If an autonomous agent is writing to a session database while a system snapshot is being taken concurrently, the resulting backup archive will likely be unreadable. Proper MCP server backup strategies account for these complex edge cases by momentarily pausing non-critical operations or applying atomic write patterns to strictly ensure the integrity of the backup payload.

Frequently Asked Questions
Best MCP backup strategies?
The absolute best MCP server backup strategies use automated, off-site snapshots combined seamlessly with cloud-native persistence. For local setups, script the immediate duplication of configuration files and SQLite databases to a secure external location. For production, leverage advanced platforms with built-in agent server persistence, such as Durable Objects, to eliminate manual backup management entirely and ensure high availability.
How to backup MCP state?
To backup MCP state properly, identify the critical files including your `mcp.json` configuration, prompt directories, and any local databases. Use automated backup tools to copy these files continuously to a separate storage medium, applying a multi-location backup rule. Always create a pre-restore snapshot before attempting to recover an agent's state to prevent accidental overwrites and data corruption.
Why is agent server persistence important?
Agent server persistence ensures that complex AI workflows can recover gracefully from crashes without losing their valuable context. Without persistent state, agents completely forget their active tasks, API tokens, and chat history, forcing complex operations to restart from the very beginning and wasting significant computational resources and time.
How do I secure my MCP server backups?
Secure your agent backups by encrypting the sensitive data both at rest and in transit. Restrict access permissions tightly to the backup directories so that only authorized administrators or verified automated service accounts can read or modify the snapshots. Never store unencrypted API keys or authentication certificates in plain text backup archives.
Related Resources

Ready to solve agent server persistence?
Stop worrying about local backups and fragile scripts. Deploy your autonomous agents on Fast.io's intelligent workspaces with built-in persistence, powerful MCP tools, and free forever storage.
