How to Implement AI Agent RBAC File Permissions
RBAC for AI agent file permissions is a security model that assigns file access rights based on role, task scope, and trust level. Implementing these controls ensures that autonomous agents only read, write, or delete files they are authorized to handle, reducing unauthorized data access risks.
What is RBAC for AI Agent File Permissions?
RBAC (Role-Based Access Control) for AI agent file permissions is a security model that assigns file access rights to agents based on their role, task scope, and trust level. This framework ensures agents can only read, write, or delete files they are authorized to handle. Unlike traditional user permissions, agent RBAC must account for autonomous decision-making and high-frequency file operations.
RBAC reduces the risk of unauthorized data access compared to ad-hoc permission models. As AI agents move from simple chatbots to autonomous workers, the complexity of these permissions grows. Enterprise AI deployments typically require several distinct agent roles with varying access levels to maintain safety and compliance.
Effective agent RBAC consists of four primary components:
- Roles: Defined identities such as Reader, Writer, or Admin that determine the baseline of what an agent can do.
- Permissions: Specific actions allowed on a resource, including read, write, delete, and share.
- Resources: The actual data targets, such as specific files, folders, or entire workspaces.
- Policies: Logic that defines when and how permissions apply, often using time-bound or task-scoped constraints.
Helpful references: Fast.io Workspaces, Fast.io Collaboration, and Fast.io AI.
Why Traditional Access Control Fails Autonomous Agents
Traditional access control systems were designed for humans who log in, perform a task, and log out. AI agents operate differently. They often require temporary elevated permissions for specific sub-tasks and may need to access raw data directly without a traditional application interface. When agents use human-style credentials, they often end up with over-privileged access that creates significant security gaps.
One major challenge is dynamic role assignment. An agent might need "Admin" rights to create a workspace for a client but only "Reader" rights when analyzing the files inside. If the agent keeps the Admin role indefinitely, a single prompt injection or logic error could lead to accidental data deletion or unauthorized sharing.
The content gap in most security guides is the failure to address these autonomous behaviors. Most systems do not provide the audit logging depth needed to track why an agent made a specific file change. To solve this, teams need a workspace environment where permissions are as intelligent as the agents using them.
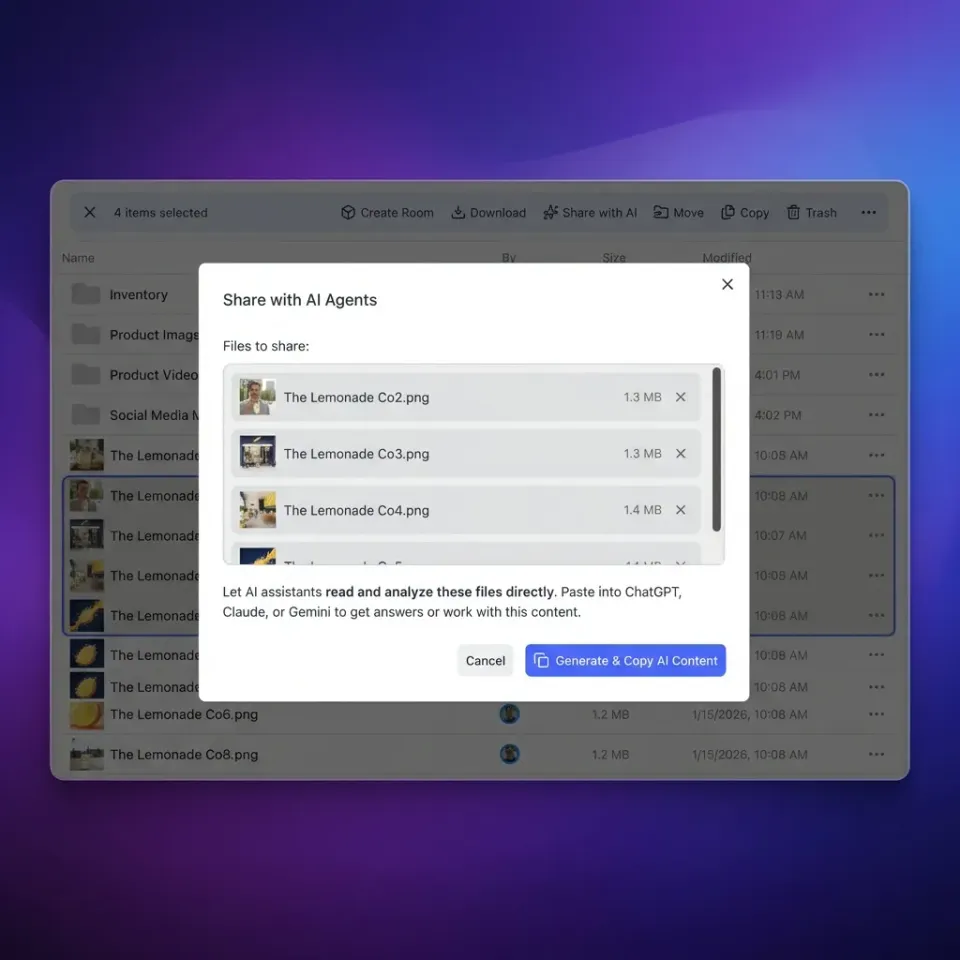
Implementing Agent-Centric Permissions with Fast.io
Fast.io provides an intelligent workspace environment designed for both humans and agents. Instead of treating agents as external API consumers, Fast.io treats them as first-class workspace members. This allows you to apply the same granular permissions to an agent that you would to a senior team member.
The Fast.io MCP (Model Context Protocol) server includes tools that map directly to UI capabilities. This means every action an agent takes, from uploading a file to setting an expiration date on a share link, is governed by the RBAC settings of that agent's role. If an agent tries to use a tool it is not authorized for, the MCP server returns a standard error, preventing the action before it reaches the file system.
Key features for agent RBAC in Fast.io include:
- Unique Agent Identities: Assign each agent its own account and credentials to ensure accountability.
- Granular Workspace Roles: Invite agents to specific workspaces with roles like Viewer, Contributor, or Manager.
- File Locks: Prevent race conditions when multiple agents attempt to write to the same file simultaneously.
- Ownership Transfer: Allow agents to build entire project structures and then transfer ownership to a human while retaining only the necessary admin rights.


Give Your AI Agents Persistent Storage
Get 50GB of free storage and MCP tools to build secure, RBAC-controlled agentic workflows today.
Patterns for Time-Bound and Task-Scoped Access
The highly secure way to manage AI agent file access is through time-bound and task-scoped policies. This approach limits the window of opportunity for an agent to perform unauthorized actions. For example, instead of giving an agent permanent access to a legal folder, you can grant access only for the duration of a specific document review task.
To implement this, follow the Evidence Sandwich pattern for security:
Define the Scope: Identify exactly which files the agent needs for the current prompt or goal. 2.
Verify via Audit: Use the Fast.io activity log to ensure the agent only touched the files within that scope. 3.
Revoke Promptly: Use automated webhooks to trigger permission removal once the agent sends its final output.
Task-scoped access reduces the risk of propagating sensitive data across different project contexts. This pattern is especially useful when using URL Import to pull files from Google Drive or OneDrive. The agent can import the file into a private Fast.io workspace, perform the work, and the temporary access naturally expires without leaving a permanent connection to the external source.
Auditing Agent File Operations
Visibility is the foundation of trust in autonomous systems. You must be able to see exactly what an agent did, when it did it, and what role it was using at the time. Fast.io provides a comprehensive audit trail that records every file view, download, and permission change.
When an agent uses the MCP server or the REST API, its actions are logged with its unique identity. This allows security teams to distinguish between human errors and agent logic failures. If an agent begins downloading an unusual volume of files, you can use webhooks to trigger an automatic account lock or a manual review.
Reviewing these logs regularly helps identify "permission creep," where agents accumulate access over time that they no longer need. By keeping agent roles lean and focused, you maintain a higher security posture and ensure that your AI workflows remain compliant with internal data governance policies.
Step-by-Step Guide: Setting Up Agent RBAC
Follow these steps to set up a secure RBAC environment for your AI agents in Fast.io.
Create an Agent Account: Sign up for the free agent tier. This provides 50GB of storage and 5,000 monthly credits without requiring a credit card. 2.
Define Workspace Roles: Create a new workspace for your project. Use the "Members" tab to invite your agent. Start with the "Viewer" role to test read-only operations. 3.
Configure the MCP Server: Connect your agent to the Fast.io MCP server at /storage-for-agents/. Ensure the agent's API key is stored securely in your environment variables.
4.
Test Tool Access: Ask your agent to perform a task, such as listing files. Verify in the Fast.io dashboard that the action was logged correctly. 5.
Promote Permissions Gradually: Only upgrade the agent to "Contributor" or "Manager" if the task requires writing or managing shares. 6.
Monitor via Webhooks: Set up a webhook listener to receive real-time notifications when your agent modifies files. This provides an immediate feedback loop for your security monitoring.
Frequently Asked Questions
How do you control AI agent file access?
You control AI agent file access by assigning unique identities to each agent and inviting them to specific workspaces with granular roles. Using a protocol like MCP allows you to enforce these permissions at the tool level, ensuring agents only use authorized functions.
What is RBAC for AI agents?
RBAC for AI agents is a security framework that grants file permissions based on the agent's specific role in a workflow. It focuses on the principle of least privilege, ensuring agents have the minimum access necessary to complete their assigned tasks.
How do you implement file permissions for autonomous agents?
Implement file permissions by creating isolated workspaces for different projects and adding agents as members with restricted roles. Use activity logs to monitor their operations and webhooks to automate the revocation of access once tasks are finished.
Should AI agents have the same permissions as users?
No, AI agents should typically have more restrictive, task-specific permissions than human users. While humans often need broad access to collaborate, agents should operate under a strict least-privilege model to prevent automated errors from affecting large datasets.
Can I limit an agent's access to specific time windows?
Yes, you can implement time-bound access by using automated scripts or webhooks that add an agent to a workspace at the start of a job and remove them once the task is complete, minimizing the window of potential exposure.
Related Resources

Give Your AI Agents Persistent Storage
Get 50GB of free storage and MCP tools to build secure, RBAC-controlled agentic workflows today.
