How to Implement AI Agent Cybersecurity Monitoring
AI agent cybersecurity monitoring spots threats as they happen using automatic analysis. Teams set up specialized agents to scan logs, spot anomalies, and respond in shared workspaces. Traditional tools fall short in agentic systems without multi-agent coordination. Fast.io handles this with file locks, audit logs, and multiple MCP tools for secure collaboration. This guide covers patterns, steps to implement, Fast.io workflows, and best practices to set up effective monitoring.

What Is AI Agent Cybersecurity Monitoring?
AI agent cybersecurity monitoring detects threats in real-time using autonomous analysis. Specialized agents scan logs, network traffic, and file activities continuously. They correlate events, identify anomalies, and trigger responses without human intervention.
In agentic environments, monitoring extends to inter-agent interactions. Agents access shared threat intelligence databases and apply behavioral models to baseline activities. Alerts go out via webhooks or notifications. Agents adapt by querying updated security documentation through built-in RAG systems.
For example, a log scanner agent parses audit logs for suspicious IP addresses. An anomaly detector flags deviations from normal behavior. A response orchestrator isolates affected files using locks.
This approach handles high-velocity data that overwhelms static tools. Agents scale horizontally, processing terabytes of logs across distributed workspaces.
The key difference from traditional monitoring lies in autonomy. While conventional SIEM tools require analysts to write rules and interpret alerts, AI agents learn patterns independently. They can:
- Process unstructured data from multiple sources simultaneously
- Correlate indicators across geographically distributed workspaces
- Execute remediation playbooks without human approval for known threat patterns
- Continuously refine detection models based on new threat intelligence

The Growing Cybersecurity Threat Landscape
Cyber threats evolve rapidly. According to CrowdStrike's 2025 Global Threat Report, 79% of detections were malware-free, relying on behavior signals like vishing attacks, which surged 442% in the second half of 2024. Verizon's multiple DBIR reports ransomware in multiple% of breaches, often starting with initial access brokers. IBM's 2025 Cost of a Data Breach Report lists the average cost at $4.multiple million, with AI security tools saving $multiple.multiple million per breach through faster response. Cyber attacks have risen multiple% year-over-year, driven by AI-assisted adversaries. Traditional monitoring struggles with volume and speed. AI agents process data at scale, detecting multiple% more threats through pattern recognition. The threat landscape has shifted fundamentally over the past several years. Early cyber attacks relied heavily on malware, viruses, worms, trojans, that security tools could detect through signature matching. Modern attacks bypass these defenses entirely. Attackers use legitimate credentials, social engineering, and living-off-the-land techniques that blend with normal business activity. This shift creates detection challenges that rule-based systems cannot address. When multiple% of attacks show no malicious code, security teams cannot scan for signatures. Instead, they need behavioral analysis that identifies anomalous patterns: unusual access times, abnormal data volumes, or credential use from unexpected locations. AI agents excel at this by learning baselines and flagging deviations. The financial stakes continue rising. IBM's data shows the average breach now costs $multiple.multiple million, with detection and response time being the primary cost drivers. Organizations using AI-powered security tools identify breaches multiple% faster, saving an average of $multiple.multiple million per incident. These savings justify investment in agent-based monitoring systems.

Why Use AI Agents for Cybersecurity?
Agents excel in dynamic environments. They run asynchronously, scaling with threat volume. MCP tools enable file operations, webhooks trigger events, and RAG provides context. Example workflow: Log indexer agent uploads parsed data. Query agent searches for IOCs. Notification agent alerts via Slack or email. In multi-agent setups, coordination prevents conflicts. Shared workspaces with granular permissions and locks ensure safe access. Traditional security tools struggle with three challenges that agents address directly. First, volume: modern environments generate terabytes of logs daily, making manual review impossible. Second, velocity: attacks unfold in seconds, but human analysis takes hours. Third, variety: threats constantly evolve, requiring models that adapt without manual rule updates. Agent architectures solve these by processing data in parallel, responding to alerts instantly, and learning from new threat intelligence. Each agent handles a specific function, log parsing, anomaly detection, threat correlation, while coordinating through shared workspaces. This modular design lets teams start simple and expand capabilities over time.
Agent Advantages Over Traditional Tools
Traditional SIEMs require manual rules. Agents learn baselines autonomously.
- Speed: Real-time analysis vs batch processing. Agents process events as they occur, identifying threats within seconds rather than waiting for daily log reviews.
- Adaptability: Update models via RAG without redeploy. When new threat intelligence emerges, agents query updated documentation immediately without infrastructure changes.
- Scale: Parallel processing across workspaces. Deploy multiple agents across different environments, each handling local data while contributing to organization-wide threat visibility.
- Cost: Free agent tier covers monitoring workloads. The multiple storage and multiple monthly credits handle substantial monitoring without initial investment.
Agent Cybersecurity Patterns Table
Match threats to patterns for effective monitoring.
Multi-Agent Workflows in Shared Environments
Competitors lack multi-agent security in shared spaces. Fast.io supports it natively.
Agents join workspaces with granular permissions. File locks avoid race conditions.
Workflow:
- Scanner acquires lock on /logs/, scans IOCs.
- Releases, writes report.
- Analyzer uses RAG on threat intel.
- Webhook notifies if high risk.
OpenClaw example:
clawhub install dbalve/fast-io
Agent code:
from fastio import MCPClient
client = MCPClient("agent-key")
files = client.list_files("/logs")
for f in files:
content = client.read_file(f["path"])
if "suspicious_ip" in content:
client.acquire_lock(f["path"])
report = analyze(content)
client.write_file("/reports/" + f["name"], report)
client.release_lock(f["path"])
client.send_webhook("https://alerts.team.com", {"threat": f["name"]})
Audit logs record all actions for review. Encryption protects data at rest/transit.

Secure Your Agent Workflows Now
50GB free storage, 5,000 credits/mo, no credit card. 251 MCP tools, locks, audits for cybersecurity monitoring. Built for agent cybersecurity monitoring workflows.
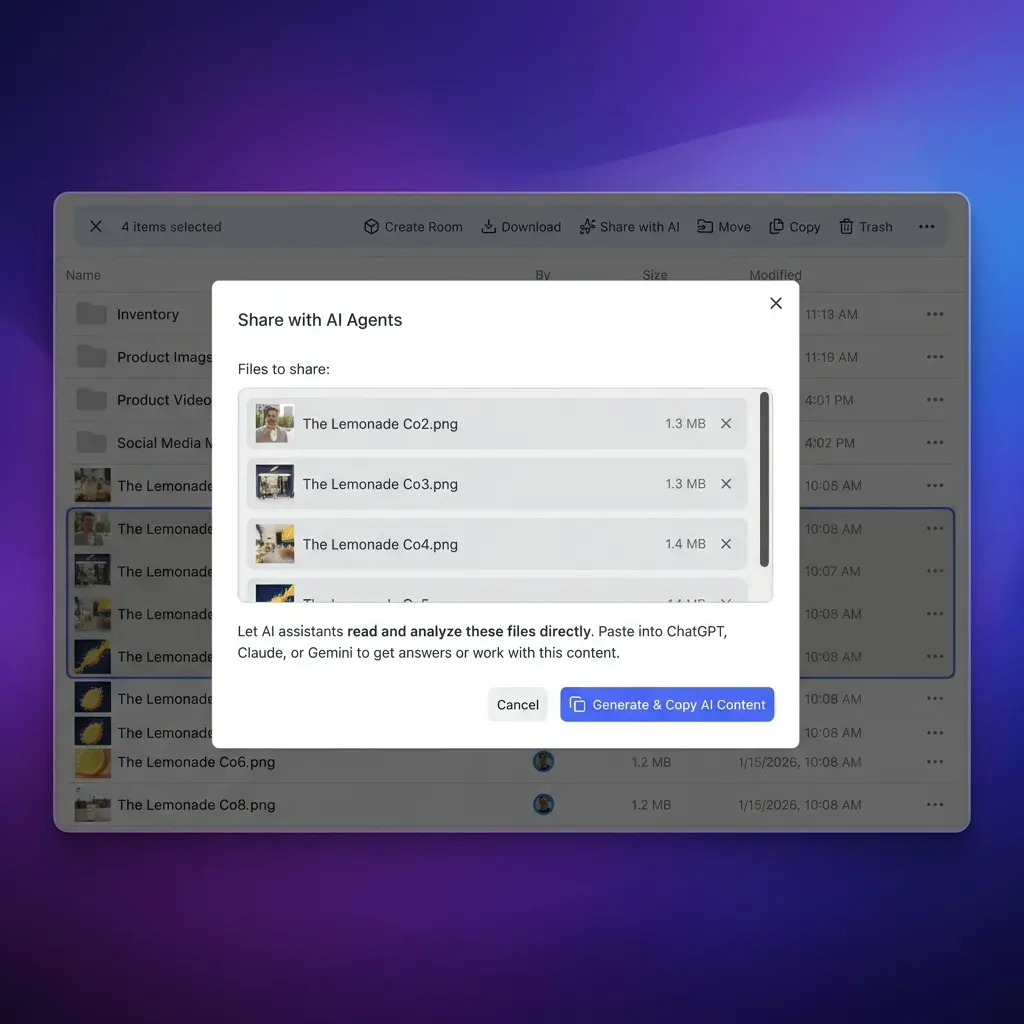
Implementing Threat Detection with Fast.io MCP
use 251 MCP tools mirroring UI.
Detailed steps:
- Sign up for free agent tier: multiple storage, multiple credits/mo, no CC required.
- Create workspace, toggle Intelligence Mode for auto-RAG indexing of threat docs.
- Deploy scanner:
client.list_files("/security-logs/") for log in logs: content = client.read_file(log.path) iocs = extract_iocs(content) if iocs: client.write_file("/alerts/high-risk.json", json.dumps(iocs)) - RAG query: client.rag_query("match IOCs to known malware")
- Webhooks on file changes trigger re-scan.
- Scale with multiple agents, locks for concurrency.
Supports chunked uploads, URL imports from SIEMs. Multi-LLM compatible.
Document access rules, audit trails, and retention policies before rollout so staging results are repeatable in production. This avoids late surprises and helps teams debug issues with confidence.
Handling Edge Cases
- Rate limits: Monitor credits (storage 100/GB, AI 1/100 tokens).
- Conflicts: Locks ensure atomicity.
- Scale: Unlimited workspaces, parallel agents.
- Fallbacks: Human oversight via ownership transfer.
Fast.io Security Features for Agents
Built for agentic security:
- Audit Logs: Track all actions - views, downloads, perms changes.
- File Locks: Prevent concurrent writes in multi-agent ops.
- Granular Permissions: Org/workspace/folder/file levels.
- Encryption: At rest and transit.
- SSO/MFA: Secure access.
- Webhooks: Reactive workflows.
Agents use same tools as humans, ensuring consistent security.
Document access rules, audit trails, and retention policies before rollout so staging results are repeatable in production. This avoids late surprises and helps teams debug issues with confidence.

OpenClaw Integration for Monitoring
Zero-config OpenClaw support:
Install: clawhub install dbalve/fast-io
multiple tools for natural language ops: list logs, read suspicious files, query RAG.
Example agent prompt: "Scan /logs/ for anomalies using threat intel in workspace."
Handles locks automatically, audits all actions.
Best Practices and Troubleshooting
Best Practices:
- Start single-agent on critical logs.
- Scale to swarm by threat type (network, file, behavior).
- Baseline normal activity first.
- Rotate agent keys regularly.
- Test failover with ownership transfer.
Troubleshooting:
Links: MCP docs, /storage-for-agents/, /pricing/
Frequently Asked Questions
What are AI agents for cybersecurity?
Autonomous agents scan, detect, and respond to threats using file operations, RAG analysis, and webhook notifications in shared workspaces. They operate continuously without human intervention, processing logs and network data to identify malicious patterns. Unlike static tools, AI agents learn from new threats and adapt detection models automatically, making them effective against evolving attack vectors.
How to monitor threats with AI agents?
Deploy monitoring agents to workspaces containing security logs and threat data. Use MCP tools to list and read files, query the RAG system to correlate IOCs with known threats, and configure webhooks to alert teams when high-risk indicators appear. File locks ensure safe access in multi-agent scenarios. Start with a single scanner agent on critical log directories, then expand to coordinated agent swarms as detection needs grow.
What makes Fast.io suitable for agent security?
Fast.io provides multiple MCP tools that mirror every UI capability, file locks for safe concurrent operations, comprehensive audit logs for compliance tracking, and Intelligence Mode with built-in RAG for semantic threat intelligence queries. The free agent tier includes multiple storage and multiple credits monthly, enough to pilot monitoring workflows without upfront investment. Agents and humans share the same workspaces, ensuring consistent security policies across automated and manual operations.
Are there risks with multi-agent monitoring?
Multi-agent systems introduce specific risks including permission conflicts, race conditions on shared files, and over-privileged access chains. Mitigate these through granular permission scoping at the organization, workspace, folder, and file levels. Always acquire file locks before writes in multi-agent workflows. Maintain audit trails to trace actions across agent interactions. Establish human oversight through ownership transfer workflows where agents can hand off alerts for human review.
How does AI improve threat detection?
AI agents handle volume and velocity that overwhelms manual analysis. According to IBM's multiple report, organizations using AI security tools save an average of $multiple.multiple million per breach through faster detection and response. AI detects approximately multiple% more threats than traditional rule-based systems by recognizing patterns across millions of events. Machine learning models adapt to new attack techniques without requiring analysts to write new detection rules for each variant.
Can OpenClaw agents do cybersecurity monitoring?
Yes. Install the Fast.io OpenClaw skill via `clawhub install dbalve/fast-io` to access multiple natural language tools for security operations. Agents can scan log directories, read suspicious files, query threat intelligence via RAG, and trigger alerts using plain English prompts. OpenClaw handles file locks automatically and maintains audit trails for all operations. This approach works well for teams wanting agentic security without complex MCP configuration.
What Fast.io features support compliance?
Fast.io provides audit logs tracking all file views, downloads, and permission changes at the organization level. Granular permissions operate across four levels: organization, workspace, folder, and individual files. Data encryption protects information at rest and in transit. SSO and MFA options add authentication layers. For compliance reporting, export audit logs regularly and use workspace versioning to maintain historical records of security-related file access.
How to scale agent monitoring?
Fast.io supports unlimited workspaces, allowing you to partition monitoring by environment, region, or threat type. Deploy parallel agents across workspaces with consistent lock acquisition patterns. The free tier works for pilot programs; upgrade to paid plans for higher storage and credit limits as detection coverage expands. Use ownership transfer to move monitoring configurations between agent and human administrators as operational needs evolve.
Related Resources

Secure Your Agent Workflows Now
50GB free storage, 5,000 credits/mo, no credit card. 251 MCP tools, locks, audits for cybersecurity monitoring. Built for agent cybersecurity monitoring workflows.
