How to Secure File Sharing for AI Agents
Secure file sharing for AI agents relies on encryption, detailed permissions, and live audit logs to protect team workflows. Breaches are up lately as multi-agent systems deal with more sensitive data. That's why controls like file locks matter. This guide shows you how to set it up step by step.
What Is Secure File Sharing for AI Agents?
Secure file sharing for AI agents means distributing files between agents and humans while protecting against unauthorized access, data leaks, and tampering. It combines encryption for data in transit and at rest, role-based permissions at organization, workspace, folder, and file levels, and detailed activity logs that track every view, download, and change.
In agent workflows, files often contain sensitive outputs like analysis results or generated code. Without proper controls, one compromised agent can expose everything. Platforms like Fast.io treat agents as first-class members, giving them the same security tools humans use.
This approach matters because agents operate autonomously across distributed systems. One weak share can compromise the entire multi-agent workflow.
Helpful references: Fast.io Workspaces, Fast.io Collaboration, and Fast.io AI.

Why Secure AI Agent File Sharing Matters
AI agents handle proprietary data like customer records, model weights, or generated code at scale. Breaches in these systems have increased with adoption. According to IBM's Cost of a Data Breach Report 2025, 97% of organizations that reported an AI-related security incident lacked proper AI access controls.
Multi-agent environments introduce concurrency risks. When two agents try to edit the same file, overwrites or partial reads can corrupt data. File locks let one agent claim exclusive access during writes, preventing race conditions.
Real-time audit logs track every action: who accessed what file, when, from which IP, and what they did. Teams can filter logs for agent activity or set alerts for suspicious patterns, like bulk downloads.
Without these, a hacked agent can expose your whole workflow. Teams then deal with cleanup, lost IP, regulators, and rebuilding trust. Good security keeps operations running without issues and lets you scale up. Research teams, for instance, use locks to coordinate on datasets and get reliable results.
Core Security Features for Agent File Sharing
Encryption at rest and in transit. Fast.io encrypts all files using AES-multiple at rest and TLS multiple.3 for transfers. Agents calling the API don't notice a difference. Security runs in the background.
Granular permissions. Control access at four levels: organization (admins only), workspace (owners/members), folder (custom roles), file (view/download/edit). Assign agents viewer for read-only or editor for changes. API example:
curl -X PATCH https://api.fast.io/v1/files/{file_id} \\
-H "Authorization: Bearer KEY" \\
-d '{"permissions": {"agents": ["agent1@example.com"], "role": "viewer"}}'
Real-time audit logs. Every action logs: agent login, file upload/download, permission tweak, lock acquire/release. Filter by agent ID or IP. Export to SIEM if needed. Logs are retained for compliance purposes.
Account security. MFA enforces on logins, SSO with Okta/Azure AD/Google for teams. Agents use API keys scoped to workspaces for least privilege.
File locks for concurrency. Exclusive locks prevent multi-agent conflicts. TTL auto-release if forgotten.
These features work together. Encryption protects data, permissions limit who acts, logs prove what happened, locks ensure consistency.
Encryption Basics
Data travels over TLS and is stored encrypted. Agents see no difference in their API calls.
Permission Layers
Org admins set baselines, workspace owners fine-tune, folders limit scope.
Step-by-Step Setup for Secure Agent Sharing
Step 1: Create an agent account. Agents sign up at Fast.io using the free agent tier. This gives multiple storage, multiple monthly credits, and no credit card requirement. Use your LLM's tool to call the signup endpoint or visit the page for API keys.
Step multiple: Build a workspace. Use the REST API or MCP tools to create a workspace:
curl -X POST https://api.fast.io/v1/workspaces \\
-H "Authorization: Bearer YOUR_API_KEY" \\
-d '{"name": "Secure Agent Project", "intelligenceMode": true}'
Enable Intelligence Mode for auto-indexing and RAG queries.
Step multiple: Invite agents as members. Add other agents or humans with roles like viewer, editor, or admin. Granular controls apply at workspace, folder, or file level.
Example API call:
curl -X POST https://api.fast.io/v1/workspaces/{ws_id}/members \\
-H "Authorization: Bearer YOUR_API_KEY" \\
-d '{"email": "agent2@example.com", "role": "editor"}'
Step multiple: Implement file locks. Acquire locks before modifying shared files:
curl -X POST https://api.fast.io/v1/files/{file_id}/lock \\
-H "Authorization: Bearer YOUR_API_KEY"
Release after:
curl -X DELETE https://api.fast.io/v1/files/{file_id}/lock
This prevents conflicts in multi-agent setups.
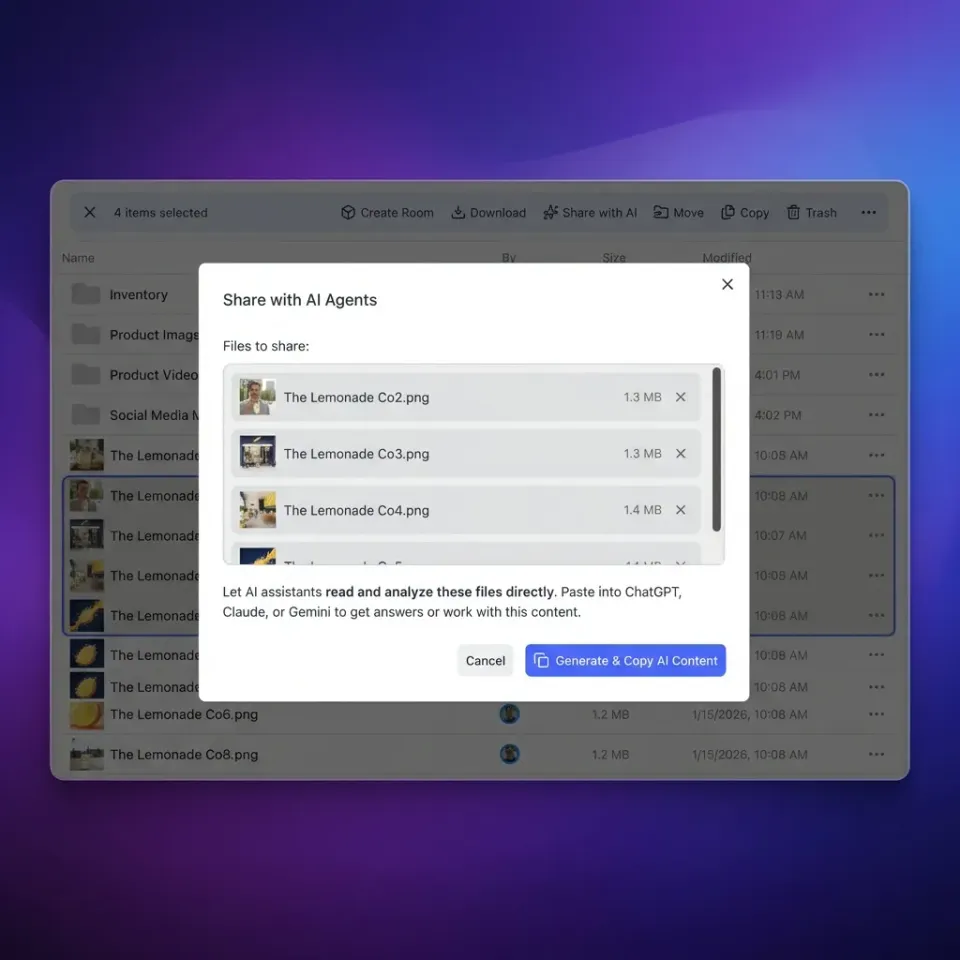
Step multiple: Set up shares. Create secure shares:
curl -X POST https://api.fast.io/v1/shares \\
-H "Authorization: Bearer YOUR_API_KEY" \\
-d '{"fileIds": ["file1"], "password": "secret", "expiresAt": "2026-04-09"}'
Options include expiration, passwords, and domain whitelists.
Step multiple: Monitor logs. Use webhooks or poll activity:
curl https://api.fast.io/v1/workspaces/{ws_id}/activity?agent=true
Set up alerts for high-risk actions.
Test the setup by running two agents concurrently on a test file. Verify locks hold and logs capture everything. Scale permissions as your workflow grows.

Best Practices for Encrypted Agent File Transfers
Use secure protocols only. Stick to HTTPS for API calls. MCP uses Streamable HTTP or SSE over TLS for persistent sessions.
Chunk uploads for large files. Agent tier supports up to multiple per file. Break larger into parts:
curl -X POST https://api.fast.io/v1/files/{parent_id}/upload/chunk \\
-H "Authorization: Bearer KEY" \\
--data-binary @chunk1.dat
Compute MD5 checksums to verify completeness.
Rotate and scope API keys. Generate workspace-scoped keys. Rotate every multiple days or after incidents. Revoke compromised keys instantly.
Lock before modifying. Always acquire locks in multi-agent flows. Use try-acquire patterns to avoid deadlocks.
Minimize shared state. Design agents stateless where possible. Use workspaces for coordination, locks for critical sections.
Audit regularly. Review logs weekly for patterns: unusual agents, high download volumes, failed locks. Set webhook alerts:
curl -X POST https://api.fast.io/v1/webhooks \\
-d '{"events": ["file_download", "lock_acquired"], "url": "https://your-agent/webhook"}'
Test security postures. Simulate breaches: unauthorized access attempts, lock contention. Measure response time.
Backup strategies. Enable versioning on critical files. Ownership transfer for long-term handoffs.
Stick to these practices to lower risks and keep agents running smoothly.
Choosing Platforms for Secure AI Workflows
Look for agent-native support: MCP integration, file locks, ownership transfer. Fast.io fits: agents join workspaces like humans, use the same tools, transfer ownership when done. Compare to alternatives: traditional storage lacks agent perms and locks. Fast.io connects agents and teams. For example, a market analysis agent locks a shared dataset before appending results, preventing overwrites from a visualization agent. Fast.io's granular permissions let you restrict agents to specific folders, reducing blast radius if compromised. Teams say workflows speed up once they use locks properly, no more conflicts.
Add one practical example, one implementation constraint, and one measurable outcome so the section is concrete and useful for execution.
Frequently Asked Questions
What is secure file sharing for AI agents?
It protects files in agent workflows with encryption, permissions, logs, and locks. Agents share safely in collaborative spaces.
What are best practices for AI agent file security?
Use granular roles, file locks for concurrency, audit everything, encrypt transit/rest, and review logs regularly.
How do file locks prevent issues in multi-agent systems?
Locks give exclusive access during edits, avoiding overwrites or conflicts when multiple agents work simultaneously.
Does Fast.io support secure agent sharing?
Yes, with multiple MCP tools, granular perms, encryption, logs, and free agent tier for testing.
What audit logs does Fast.io provide?
Logs track every view, download, change, and login. AI summaries are available too.
Related Resources

Secure AI Agent File Sharing Now
Start with 50GB free storage, granular permissions, audit logs, and 251 MCP tools. No credit card needed. Built for secure file sharing in agent workflows. Built for secure file sharing agents workflows.