AI Agent Rate Limiting Strategies: Complete Guide for 2026
AI agents require different rate limiting approaches than traditional APIs because they chain multiple calls per task. This guide covers exponential backoff, token buckets, adaptive rate limiting, and strategies for multi-step and multi-agent systems. This guide covers ai agent rate limiting with practical examples.

What Is AI Agent Rate Limiting?
AI agent rate limiting involves controlling how frequently agents make API calls, access resources, and consume credits to prevent service disruptions, manage costs, and stay within provider quotas. Traditional rate limiting was built for browsers and apps used by humans. AI agents behave differently. A single agent task can trigger dozens of sequential API calls, making traditional fixed-window limits ineffective. According to Nordic APIs, AI agents now make bursty, unpredictable calls that can look like DDoS attacks, even when the traffic is legitimate. LLM API rate limits range from 60 to 10,000+ requests per minute depending on tier. Without proper rate limiting, agents exhaust quotas in seconds, causing cascading failures across your application. Unmanaged rate limiting is the #1 cause of agent failures in production.
The core challenge: AI agents chain multiple API calls per task. A simple document summarization might involve file retrieval, chunking, three LLM calls, and storage operations. If any step hits a rate limit, the entire workflow fails.
What to check before scaling ai agent rate limiting
Rate limit errors signal that your agent exceeded API quotas. Recognizing these errors is the first step to handling them gracefully.
OpenAI:
- HTTP 429: "Rate limit exceeded"
- Error code:
rate_limit_exceeded - Headers:
x-ratelimit-remaining,x-ratelimit-reset
Anthropic (Claude):
- HTTP 429: "Too many requests"
- Error code:
rate_limit_error - Retry-After header indicates wait time
Google (Gemini):
- HTTP 429: "Resource exhausted"
- Error code:
RESOURCE_EXHAUSTED - Rate limits vary by request type (requests per minute, tokens per minute)
Common patterns across providers:
- 429 status codes universally indicate rate limiting
- Response headers include quota information
- Errors distinguish between quota types (requests vs tokens vs concurrent connections)
When your agent hits a 429, the naive approach is to retry immediately. This makes the problem worse, wasting API calls on failed retries and potentially triggering stricter throttling.

Rate Limiting Strategies by Agent Type
Different agent architectures require different rate limiting approaches. Choose based on your agent's complexity and task structure.
Simple Single-Step Agents
Profile: One API call per user request. Examples: text generation, single image analysis, basic classification.
Strategy: Fixed window with token bucket fallback
- Track requests per minute per API key
- Reserve 10-20% buffer below provider limit
- Use token bucket for burst allowances
Implementation:
- Store request timestamps in memory (last 60 seconds)
- Before calling API, check if count < (limit * 0.8)
- If limit reached, return cached response or queue request
Multi-Step Agents
Profile: Chain 3-10 API calls per task. Examples: RAG pipelines, document processing, research agents.
Strategy: Adaptive rate limiting with exponential backoff
- Predict total calls needed for task
- Reserve quota for entire workflow before starting
- Implement exponential backoff on failures (1s, 2s, 4s, 8s)
Key pattern: Check available quota BEFORE starting workflows, not during. If you'll need 5 API calls to complete a task, verify you have quota for all 5 before making the first call. Otherwise you'll get partial results and wasted quota.
Multi-Agent Systems
Profile: 10+ concurrent agents sharing quotas. Examples: autonomous research teams, distributed task processors.
Strategy: Centralized quota management with priority queues
- Shared rate limit tracker across all agents
- Priority assignment (critical tasks get quota first)
- Dynamic quota reallocation based on agent performance
Implementation patterns:
- Redis-backed quota counter for distributed systems
- Pub/sub for quota availability notifications
- Agent-level backpressure when quota is scarce
Exponential Backoff Implementation
Exponential backoff is the most effective retry strategy for rate-limited API calls. It prevents retry storms while maximizing throughput.
How It Works
When you receive a 429 error:
- Wait 1 second, retry
- If still failing, wait 2 seconds, retry
- If still failing, wait 4 seconds, retry
- Continue doubling delay up to max (typically 32-64 seconds)
- After max retries (usually 5-7), fail permanently
Add Jitter
Random jitter prevents thundering herd problems when multiple agents retry simultaneously. Instead of waiting exactly 4 seconds, wait 4 + random(0, 1) seconds. This spreads retries over time and reduces synchronized load spikes.
Production Example
Basic pattern:
import time
import random
def call_with_backoff(api_func, max_retries=5):
for attempt in range(max_retries):
try:
return api_func()
except RateLimitError as e:
if attempt == max_retries - 1:
raise
wait_time = (2 ** attempt) + random.uniform(0, 1)
time.sleep(wait_time)
When to use it: All agent systems that make external API calls. It's the industry standard for a reason.
Token Bucket Algorithm
Token bucket allows controlled bursts while enforcing average rate limits. It's more flexible than fixed windows for bursty agent workloads.
How It Works
Imagine a bucket that holds tokens:
- Bucket starts with N tokens (capacity)
- Tokens refill at R tokens per second
- Each API call consumes 1 token
- If bucket is empty, requests wait or fail
Benefits for AI agents:
- Allows bursts up to bucket capacity
- Smooths rate over time
- Prevents quota waste from unused capacity
Example: OpenAI allows 10,000 requests per minute. With token bucket, you can make 200 requests instantly (burst), then throttle to 166 requests per second for the rest of the minute.
Implementation
Track two values:
- Tokens available (decreases with use)
- Last refill timestamp
Before each request:
def can_make_request(bucket):
now = time.time()
elapsed = now - bucket.last_refill
tokens_to_add = elapsed * bucket.refill_rate
bucket.tokens = min(bucket.capacity, bucket.tokens + tokens_to_add)
bucket.last_refill = now
if bucket.tokens >= 1:
bucket.tokens -= 1
return True
return False
When to use it: Agents with unpredictable workloads, background processors, batch operations.
Adaptive Rate Limiting
Adaptive rate limiting adjusts quotas dynamically based on observed API behavior. It's essential for production multi-agent systems.
Why Traditional Limits Fail for Agents
Static rate limits assume consistent load. AI agents don't behave that way. They experience:
- Traffic spikes (10 users submit documents simultaneously)
- Long idle periods (no requests for minutes)
- Variable task complexity (some tasks need 2 calls, others need 20)
According to TrueFoundry, adaptive rate limiting uses dynamic quotas that adjust automatically based on real-time usage patterns.
Adaptive Strategies
Provider-based adjustment:
- Monitor actual rate limit headers from API responses
- If provider increases limits (tier upgrade), detect and use new capacity
- If provider throttles unexpectedly, reduce request rate automatically
Cost-based throttling:
- Track spend per agent
- Slow down high-cost agents when approaching budget limits
- Reserve quota for high-priority tasks
Error-rate feedback:
- If 429 errors exceed 5% of requests, reduce rate by 20%
- If error-free for 10 minutes, increase rate by 10%
- This creates a self-balancing system
Implementation Pattern
Maintain a dynamic rate multiplier (0.5 to 1.5):
current_limit = base_limit * dynamic_multiplier
### After each request
if response.status == 429:
dynamic_multiplier *= 0.9 # Reduce by 10%
elif success_streak > 100:
dynamic_multiplier = min(1.5, dynamic_multiplier * 1.05)
When to use it: Production systems with variable load, multi-tenant agent platforms, cost-sensitive applications.
Multi-Agent Coordination
When multiple agents share API quotas, centralized coordination prevents quota starvation and ensures fair distribution.
The Problem
You have 10 agents sharing a 10,000 requests/minute quota. Without coordination:
- 3 aggressive agents consume entire quota
- 7 slower agents get starved
- Total system throughput drops
Centralized Quota Manager
Implement a shared service that tracks and allocates quota:
Key components:
- Global counter (Redis, database, or in-memory)
- Reservation system (agents request quota before tasks)
- Priority queue (critical tasks get quota first)
- Reclamation (unused reserved quota returns to pool)
Fair Scheduling Algorithms
Round-robin: Each agent gets equal quota allocation. Simple but ignores task priority.
Weighted fair queuing: Agents get quota proportional to their priority score. High-value agents get more quota.
Deficit round-robin: Tracks quota "debt" and compensates agents that were starved in previous cycles.
Practical Pattern
Before starting work:
quota_needed = estimate_api_calls(task)
if quota_manager.reserve(agent_id, quota_needed):
execute_task()
quota_manager.release_unused(agent_id)
else:
queue_task_for_later()
This stops agents from starting work they can't finish.
Rate Limiting for File-Heavy Agents
Agents that process large files face compound rate limits: API requests, bandwidth, storage operations, and document ingestion costs.
The Bandwidth Problem
LLM providers charge for input tokens. A 100MB PDF might contain 50,000 tokens. If you're processing 100 documents per hour, that's 5M tokens, potentially hitting token-per-minute limits before request limits.
Strategies:
- Chunk large files and process incrementally
- Cache processed chunks to avoid re-processing
- Use streaming APIs where available (reduces memory, spreads token usage)
Storage-Aware Rate Limiting
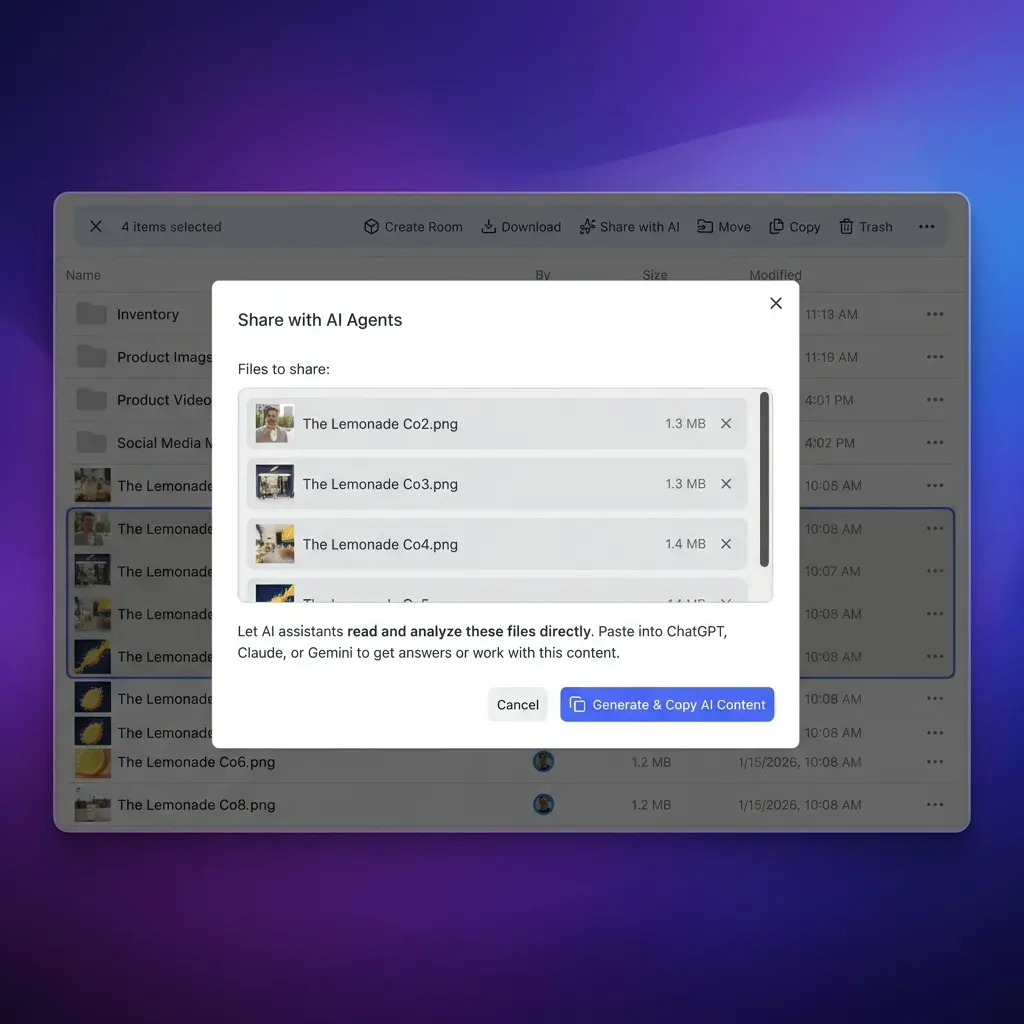
Fast.io provides 50GB free storage for AI agents with 5,000 monthly credits. Credits cover:
- Storage: 100 credits/GB
- Bandwidth: 212 credits/GB
- Document ingestion: 10 credits/page
Budget your usage:
- Uploading 1GB file: 100 credits + bandwidth charges
- Processing 500-page PDF: 5,000 credits (your entire monthly allowance)
Implement credit tracking:
estimated_cost = (file_size_gb * 100) + (pages * 10)
if remaining_credits >= estimated_cost:
process_file()
else:
defer_to_next_period()
File Locks for Concurrent Access
When multiple agents process the same files, use Fast.io's file locks to prevent conflicts:
Pattern:
- Agent A acquires lock on document.pdf
- Agent B attempts lock, receives "locked" response
- Agent B waits or processes different file
- Agent A releases lock when done
This stops wasted API calls from processing the same file twice.

Monitoring and Debugging Rate Limits
You can't optimize what you don't measure. Track these metrics to understand your rate limit behavior.
Key Metrics
Request patterns:
- Requests per minute (current vs limit)
- 429 error rate (should be <1%)
- Average retry count per failed request
Cost metrics:
- API spend per agent
- Cost per completed task
- Quota utilization percentage
Performance indicators:
- Task completion time (increases when rate-limited)
- Queue depth (requests waiting for quota)
- Agent idle time (wasted capacity)
Response Header Analysis
Most providers return quota information in headers:
x-ratelimit-limit: 10000
x-ratelimit-remaining: 8234
x-ratelimit-reset: 1643723400
Log these on every request. They tell you:
- How close you are to limits
- When limits reset
- Whether limits changed (provider tier upgrade)
Alert Thresholds
Set alerts for:
- 429 error rate >5% (immediate issue)
- Quota utilization >90% (capacity planning)
- Average wait time >2 seconds (user experience impact)
Fast.io's audit logs track all file operations with timestamps and agent IDs. Use this to correlate storage operations with API rate limit events.
Best Practices for Production Agents
These patterns prevent rate limit issues before they occur.
Design for Failure
Assume rate limits will be hit. Build recovery into your architecture:
- Every API call should have retry logic
- Tasks should be resumable (save state after each step)
- Agents should gracefully degrade (return partial results when quota is exhausted)
Pre-Flight Quota Checks
Before starting expensive workflows, verify quota availability:
workflow_cost = estimate_total_calls(task)
available = get_available_quota()
if available >= workflow_cost:
execute_workflow()
else:
schedule_for_later()
This stops you from starting work you can't finish.
Circuit Breakers
When error rates spike, stop sending requests temporarily:
Pattern:
- Track error rate over sliding 1-minute window
- If errors >10%, open circuit (stop requests)
- After 30 seconds, try one request (half-open state)
- If successful, close circuit (resume normal operation)
This stops cascading failures and gives APIs time to recover.
Use Webhooks Instead of Polling
Fast.io provides webhooks for file events. Instead of polling for changes (wastes quota), register webhooks:
Bad (polling):
while True:
check_for_new_files() # API call every 5 seconds = 720 calls/hour
time.sleep(5)
Good (webhooks):
### Register once
register_webhook("https://your-agent.com/on-file-upload")
### Receive notifications when files change (0 API calls)
Webhooks eliminate unnecessary API calls, saving quota for actual work.
Frequently Asked Questions
What happens when an AI agent hits a rate limit?
The API returns a 429 HTTP status code with an error message. The agent should implement exponential backoff, waiting progressively longer between retries (1s, 2s, 4s, 8s). Most providers include a Retry-After header indicating how long to wait. Without proper handling, the agent fails and wastes quota on unsuccessful retries.
How do I implement rate limiting for AI agents?
Start with exponential backoff for all API calls. Track requests per minute and stay 10-20% below provider limits. For multi-step agents, reserve quota for entire workflows before starting. For multi-agent systems, use centralized quota management with Redis or a database to coordinate requests across agents. Add jitter to retry delays to prevent synchronized retry storms.
What are common rate limit errors in agent systems?
HTTP 429 errors are universal across providers. OpenAI returns 'rate_limit_exceeded', Anthropic returns 'rate_limit_error', and Google returns 'RESOURCE_EXHAUSTED'. These errors indicate you've exceeded requests per minute, tokens per minute, or concurrent connection limits. Check response headers for quota details and reset timestamps.
How do AI agents handle rate limits differently than traditional apps?
Traditional apps make one API call per user action. AI agents chain multiple calls per task, making rate limits more complex. A single agent workflow might trigger 10-20 sequential API calls. If any step hits a limit, the entire task fails. Agents need workflow-aware rate limiting that reserves quota for complete tasks, not individual requests.
What is adaptive rate limiting for AI agents?
Adaptive rate limiting adjusts quotas dynamically based on real-time API behavior. It monitors error rates, cost patterns, and provider signals to automatically increase limits when capacity is available and reduce limits when errors spike. This self-balancing approach prevents both quota waste and cascading failures in production systems.
How do I prevent multiple agents from exceeding shared rate limits?
Implement centralized quota management using Redis or a database. Agents request quota reservations before starting work, ensuring total requests stay within limits. Use priority queues to allocate quota to critical tasks first. Implement quota reclamation so unused reservations return to the pool for other agents.
What's the difference between token bucket and fixed window rate limiting?
Fixed window counting resets quota at fixed intervals (every minute, every hour). If your limit is 100 requests per minute, you can make 100 requests in the first second, then wait 59 seconds. Token bucket allows controlled bursts while enforcing average rates. It refills tokens continuously, smoothing traffic and preventing quota waste from unused capacity.
How can I reduce API rate limit pressure for file-heavy agents?
Use persistent storage like Fast.io to cache processed files and intermediate results. Implement chunking for large files to spread API calls over time. Use webhooks instead of polling to eliminate unnecessary requests. Process files incrementally and save state after each step so you can resume without re-processing.
Related Resources

Run AI Agent Rate Limiting Strategies Complete Guide For 2026 workflows on Fast.io
Fast.io gives AI agents 50GB free storage, 251 MCP tools, built-in RAG, and webhooks to eliminate polling. Stop wasting quota on file operations.